The operators of the Mozi IoT botnet have been taken into custody by Chinese law enforcement authorities, just about two years immediately after the malware emerged on the danger landscape in September 2019.
Information of the arrest, which at first occurred in June, was disclosed by scientists from Netlab, the network exploration division of Chinese internet security company Qihoo 360, before this Monday, detailing its involvement in the operation. The
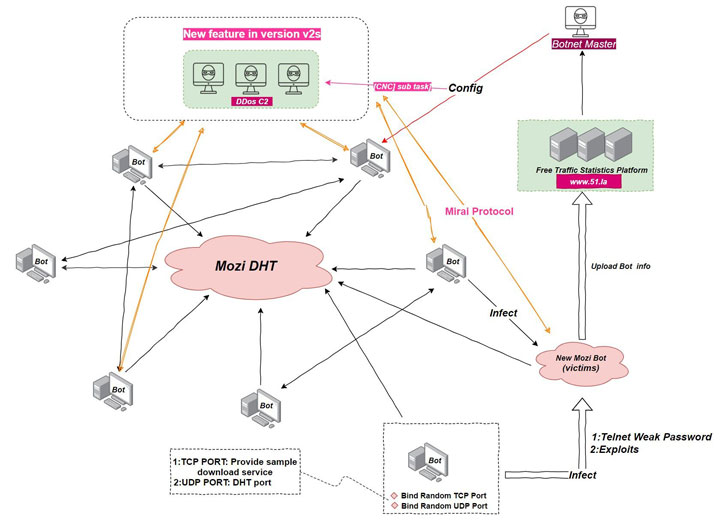
“Mozi uses a P2P [peer-to-peer] network framework, and one particular of the ‘advantages’ of a P2P network is that it is strong, so even if some of the nodes go down, the entire network will have on, and the remaining nodes will still infect other susceptible gadgets, that is why we can nevertheless see Mozi spreading,” mentioned Netlab, which noticed the botnet for the initially time in late 2019.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The progress also arrives fewer than two months following Microsoft Security Threat Intelligence Centre discovered the botnet’s new abilities that allow it to interfere with the web visitors of contaminated units by using techniques these types of as DNS spoofing and HTTP session hijacking with the aim of redirecting buyers to destructive domains.
Mozi, which progressed from the source code of a number of recognised malware families these kinds of as Gafgyt, Mirai, and IoT Reaper, is reported to have amassed much more than 15,800 command-and-management nodes, according to a report from Lumen’s Black Lotus Labs launched in April 2020, a selection that has due to the fact ballooned to 1.5 million, with China and India accounting for the most bacterial infections.
Exploiting the use of weak and default remote obtain passwords as properly as through unpatched vulnerabilities, the botnet propagates by infecting routers and digital video recorders to co-choose the gadgets into an IoT botnet, which could be abused for launching dispersed denial-of-service (DDoS) attacks, facts exfiltration, and payload execution.
Now in accordance to Netlab, the Mozi authors also packed in supplemental updates, which contains a mining trojan that spreads in a worm-like fashion through weak FTP and SSH passwords, increasing on the botnet’s options by following a plug-in like method to creating tailor made tag instructions for distinctive functional nodes. “This advantage is one particular of the motives for the quick enlargement of the Mozi botnet,” the scientists mentioned.
What is actually more, Mozi’s reliance on a BitTorrent-like Dispersed Hash Table (DHT) to talk with other nodes in the botnet as an alternative of a centralized command-and-management server will allow it to purpose unimpeded, earning it challenging to remotely activate a get rid of switch and render the malware ineffective on compromised hosts.
“The Mozi botnet samples have stopped updating for fairly some time, but this does not signify that the menace posed by Mozi has finished,” the researchers cautioned. “Considering that the parts of the network that are currently unfold throughout the Internet have the capability to continue on to be contaminated, new products are infected each individual working day.”
Observed this post intriguing? Follow THN on Fb, Twitter and LinkedIn to browse much more exclusive material we publish.
Some parts of this short article are sourced from:
thehackernews.com

 Sacked Employee Deletes 21GB of Credit Union Files
Sacked Employee Deletes 21GB of Credit Union Files