Cybersecurity researchers from FireEye unmasked extra strategies, techniques, and procedures (TTPs) adopted by Chinese risk actors who were being just lately found abusing Pulse Secure VPN devices to fall malicious web shells and exfiltrate sensitive information from organization networks.
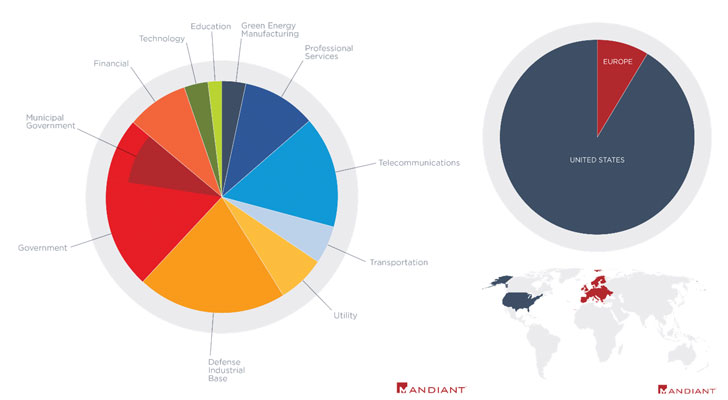
FireEye’s Mandiant threat intelligence crew, which is monitoring the cyberespionage activity under two threat clusters UNC2630 and UNC2717, claimed the intrusions lines up with critical Chinese govt priorities, including “many compromised businesses operate in verticals and industries aligned with Beijing’s strategic objectives outlined in China’s recent 14th 5 Year Plan.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
On April 20, the cybersecurity agency disclosed 12 unique malware households, including STEADYPULSE and LOCKPICK, that have been designed with the specific intent to infect Pulse Safe VPN appliances and place to use by quite a few cyberespionage teams believed to be affiliated with the Chinese governing administration.
- UNC2630 – SLOWPULSE, RADIALPULSE, THINBLOOD, ATRIUM, PACEMAKER, SLIGHTPULSE, and PULSECHECK
- UNC2717 – HARDPULSE, QUIETPULSE, AND PULSEJUMP
FireEye’s continued investigation into the attacks as component of its incident reaction endeavours has uncovered 4 extra malware families deployed by UNC2630 — BLOODMINE, BLOODBANK, CLEANPULSE, and RAPIDPULSE — for applications of harvesting qualifications and sensitive technique facts, permitting arbitrary file execution, and eliminating forensic proof.
In addition, the danger actors ended up also observed getting rid of web shells, ATRIUM, and SLIGHTPULSE, from dozens of compromised VPN gadgets in between April 17 and April 20 in what the scientists explain as “unconventional,” suggesting “this motion shows an attention-grabbing worry for operational security and a sensitivity to publicity.”
At the heart of these intrusions lies CVE-2021-22893, a recently patched vulnerability in Pulse Safe VPN products that the adversaries exploited to acquire an preliminary foothold on the focus on network, working with it to steal qualifications, escalate privileges, conduct inner reconnaissance by relocating laterally throughout the network, ahead of keeping long-time period persistent accessibility, and accessing delicate information.
“Each UNC2630 and UNC2717 display superior tradecraft and go to amazing lengths to stay away from detection. The actors modify file timestamps and consistently edit or delete forensic proof these kinds of as logs, web server core dumps, and files staged for exfiltration,” the researchers mentioned. “They also exhibit a deep knowing of network appliances and highly developed expertise of a targeted network. This tradecraft can make it complicated for network defenders to establish a finish listing of instruments made use of, qualifications stolen, the preliminary intrusion vector, or the intrusion start day.”
Located this write-up fascinating? Stick to THN on Fb, Twitter and LinkedIn to examine additional unique information we post.
Some pieces of this post are sourced from:
thehackernews.com


 What is DMARC and how can it improve your email security?
What is DMARC and how can it improve your email security?