China-linked adversaries have been attributed to an ongoing onslaught versus Indian electricity grid corporations, just one 12 months after a concerted campaign focusing on critical infrastructure in the region came to light.
Most of the intrusions associated a modular backdoor named ShadowPad, in accordance to Recorded Future’s Insikt Team, a refined remote accessibility trojan which has been dubbed a “masterpiece of privately sold malware in Chinese espionage.”
“ShadowPad proceeds to be used by an ever-expanding selection of People’s Liberation Military (PLA) and Ministry of State Security (MSS)-connected teams, with its origins joined to known MSS contractors very first making use of the tool in their individual operations and later probable performing as a digital quartermaster,” the researchers claimed.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The aim of the sustained campaign, the cybersecurity corporation stated, is to facilitate intelligence gathering pertaining to critical infrastructure units in preparing for future contingency operations. The focusing on is believed to have commenced in September 2021.
The attacks took intention at 7 State Load Despatch Centres (SDLCs) positioned mostly in Northern India, in individual these near to the disputed India-China border in Ladakh, with a single of the targets victimized in a identical attack disclosed in February 2021 and attributed to the RedEcho group.
The 2021 RedEcho attacks associated the compromise of 10 unique Indian ability sector companies, which include 6 of the country’s regional and condition load despatch centres (RLDC), two ports, a country electric power plant, and a substation.
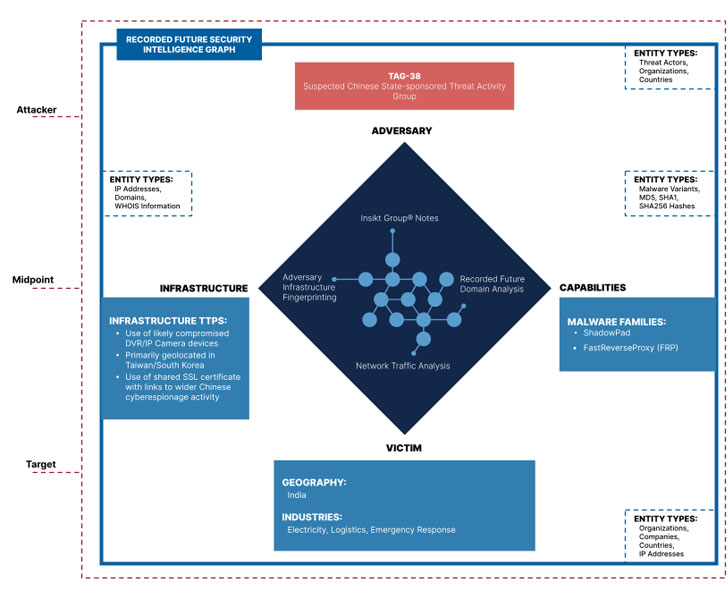
Recorded Long term connected the latest set of destructive actions to an rising danger cluster it really is monitoring beneath the moniker Threat Exercise Group 38 aka TAG-38 (related to the UNC#### and DEV-#### designations presented by Mandiant and Microsoft), citing “noteworthy distinctions” from that of the formerly recognized RedEcho TTPs.
In addition to attacking power grid belongings, TAG-38 impacted a nationwide crisis reaction procedure and the Indian subsidiary of a multinational logistics organization.
Even though the initial infection vector utilised to breach the networks is unfamiliar, the ShadowPad malware on the host methods were being commandeered by suggests of a network of infected internet-struggling with DVR/IP camera products geolocated in Taiwan and South Korea.
“The use of ShadowPad across Chinese action teams carries on to mature about time, with new clusters of activity on a regular basis discovered applying the backdoor as perfectly as ongoing adoption by previously tracked clusters,” the scientists reported, incorporating it is monitoring at least 10 distinctive teams with obtain to the malware.
Following the disclosure, India’s Union Ability Minister R. K. Singh characterised the intrusions as unsuccessful “probing attempts” at hacking which occurred in January and February, and that the federal government is continuously reviewing its cybersecurity mechanisms to bolster defenses.
China, for its portion, reiterated that it “firmly opposes and combats all sorts of cyber attacks” and that “cybersecurity is a frequent obstacle dealing with all countries that really should be jointly dealt with by dialogue and cooperation.”
“Not long ago, Chinese cybersecurity organizations released a series of stories, revealing that the U.S. govt introduced cyber attacks on a lot of countries about the entire world, including China, severely jeopardizing the security of critical infrastructure of these nations around the world,” China’s Overseas Ministry spokesperson, Zhao Lijian, reported.
“It is well worth noting that several of U.S. allies or nations around the world with which it cooperates on cyber security are also victims of U.S. cyber attacks. We believe that the international group, specially China’s neighboring international locations, will continue to keep their eyes large open up and make their individual judgment on the genuine intentions of the U.S. side.”
Identified this posting intriguing? Follow THN on Facebook, Twitter and LinkedIn to study additional special information we put up.
Some parts of this write-up are sourced from:
thehackernews.com


 Researchers Connect BlackCat Ransomware with Past BlackMatter Malware Activity
Researchers Connect BlackCat Ransomware with Past BlackMatter Malware Activity