Cybersecurity scientists on Wednesday uncovered a new cyberespionage campaign targeting navy businesses in Southeast Asia.
Attributing the attacks to a risk actor dubbed “Naikon APT,” cybersecurity firm Bitdefender laid out the ever-switching methods, approaches, and treatments adopted by the team, together with weaving new backdoors named “Nebulae” and “RainyDay” into their knowledge-stealing missions. The destructive exercise is claimed to have been executed involving June 2019 and March 2021.
“In the commencing of the procedure the risk actors applied Aria-Physique loader and Nebulae as the to start with stage of the attack,” the researchers explained. “Beginning with September 2020, the risk actors involved the RainyDay backdoor in their toolkit. The goal of this procedure was cyberespionage and facts theft.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Alleged to be tied to China, Naikon (aka Override Panda, Lotus Panda, or Hellsing) has a observe report of focusing on government entities in the Asia-Pacific (APAC) region in lookup of geopolitical intelligence. Though originally assumed to have long gone given that 2015, evidence emerged to the opposite very last Could when the adversary was noticed using a new backdoor identified as “Aria-Overall body” to stealthily break into networks and leverage the compromised infrastructure as a command-and-handle (C2) server to launch added attacks against other companies.
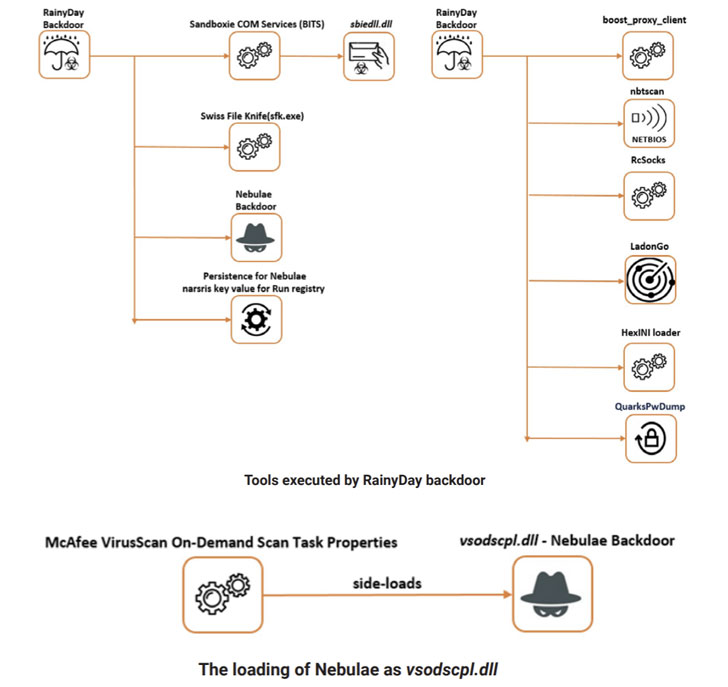
The new wave of attacks discovered by Bitdefender employed RainyDay as the most important backdoor, with the actors employing it to carry out reconnaissance, deliver more payloads, accomplish lateral movement across the network, and exfiltrate delicate facts. The backdoor was executed by usually means of a procedure recognised as DLL facet-loading, which refers to the tried out-and-examined approach of loading malicious DLLs in an attempt to hijack the execution circulation of a genuine software like Outlook Merchandise Finder.

As an more precaution, the malware also installed a 2nd implant termed Nebulae to amass procedure facts, have out file operations, and down load and upload arbitrary files from and to the C2 server. “The 2nd backdoor […] is supposedly applied as a measure of precaution to not shed the persistence in case any signs of infections get detected,” the scientists explained.
Other applications deployed by the RainyDay backdoor incorporate a resource that picks up not long ago changed data files with specific extensions and uploads them to Dropbox, a credential harvester, and various networking utilities these kinds of as NetBIOS scanners and proxies.
What is actually extra, Bitdefender explained RainyDay is very likely the very same malware that Kaspersky disclosed before this month, citing similarities in the operation and the use of DLL aspect-loading to attain execution. Called “FoundCore,” the backdoor was attributed to a Chinese-speaking actor named Cycldek as aspect of a cyberespionage marketing campaign directed from governing administration and army organizations in Vietnam.
Observed this posting fascinating? Follow THN on Fb, Twitter and LinkedIn to go through a lot more exceptional written content we article.
Some parts of this posting are sourced from:
thehackernews.com

 Ransomware Task Force releases long-awaited recommendations
Ransomware Task Force releases long-awaited recommendations