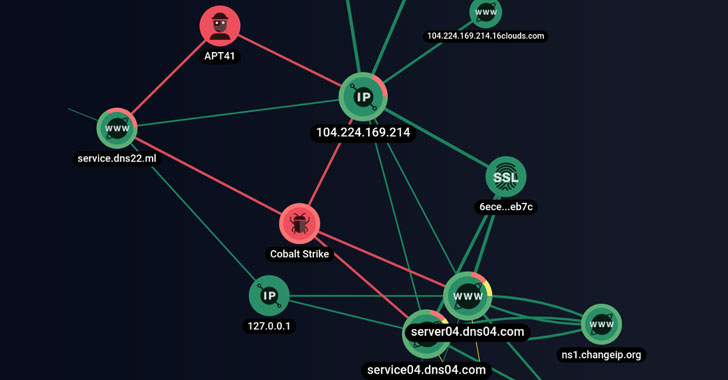
The cyber assault on Air India that came to mild last thirty day period lasted for a time period of at least two months and 26 times, new research has revealed, which attributed the incident with average assurance to a Chinese nation-point out risk actor called APT41.
Group-IB dubbed the campaign “ColunmTK” dependent on the names of the command-and-manage (C2) server domains that were being made use of for communications. “The probable ramifications of this incident for the whole airline sector and carriers that could nonetheless find out traces of ColunmTK in their networks are important,” the Singapore-headquartered danger looking firm mentioned.
Also recognised by other monikers these as Winnti Umbrella, Axiom, and Barium, APT41 is a prolific Chinese-speaking nation-state highly developed persistent risk identified for its campaigns centered all over data theft and espionage in opposition to healthcare, significant-tech, and telecommunications sectors to build and keep strategic access for thieving intellectual house and committing monetarily determined cybercrimes.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Their cyber crime intrusions are most obvious amongst video video game field targeting, including the manipulation of digital currencies, and tried deployment of ransomware,” in accordance to FireEye. “APT41 functions in opposition to increased schooling, travel solutions, and information/media companies give some sign that the team also tracks men and women and conducts surveillance.”
On Could 21, India’s flag provider airline, Air India, disclosed a info breach affecting 4.5 million of its shoppers over a interval stretching nearly 10 a long time in the wake of a source chain attack directed at its Passenger Service Method (PSS) supplier SITA before this February.
The breach associated private information registered amongst Aug. 26, 2011, and Feb. 3, 2021, which include information these types of as names, dates of delivery, speak to info, passport info, ticket facts, Star Alliance, and Air India regular flyer knowledge, as properly as credit history card data.

Team-IB’s examination into the incident has uncovered that at the very least considering the fact that Feb. 23, an contaminated product inside Air India’s network (named “SITASERVER4”) communicated with a server hosting Cobalt Strike payloads dating all the way again to Dec. 11, 2020. Next this preliminary compromise, the attackers are stated to have set up persistence and obtained passwords in get to pivot laterally to the broader network with the aim of collecting details inside of the nearby network.
No less than 20 gadgets have been infected during the training course of lateral motion, the company reported. “The attackers exfiltrated NTLM hashes and basic-text passwords from regional workstations making use of hashdump and mimikatz,” Team-IB Threat Intelligence Analyst Nikita Rostovcev mentioned. “The attackers tried using to escalate area privileges with the assist of BadPotato malware.”

In all, the adversary extracted 23.33 MB of knowledge from five products named SITASERVER4, AILCCUALHSV001, AILDELCCPOSCE01, AILDELCCPDB01, and WEBSERVER3, with the attackers using 24 several hours and 5 minutes to spread Cobalt Strike beacons to other units in the airline’s network.
Whilst the first entry issue stays unfamiliar, the actuality that “the very first product that started off speaking with the adversary-managed C&C server was a SITA server and the reality that SITA notified Air India about its security incident give sensible floor to feel that the compromise of Air India’s network was the result of a innovative supply chain attack, which may well have began with SITA.”
Connections to Barium are grounded on the foundation of overlaps among the C2 servers discovered in the attack infrastructure with people employed in previously attacks and ways utilized by the threat actor to park their domains once their functions are more than. Team-IB also mentioned it uncovered a file named “Install.bat” that bore similarities to payloads deployed in a 2020 worldwide intrusion marketing campaign.
Indicators of compromise (IoC) connected with the incident can be accessed listed here.
Discovered this article fascinating? Adhere to THN on Fb, Twitter and LinkedIn to read more unique written content we publish.
UPDATE
SITA would like to clarify a few points regarding your article https://thecybersecurity.news/general-cyber-security-news/chinese-hackers-believed-to-be-behind-sita-air-india-data-breach-10093/ and share SITA’s side of the story.
On 10 June 2021, Group-IB published a blog post, which mentioned SITA, Air India, and a group called APT41. In this blog, Group-IB described with technical detail an alleged cyber-attack on Air India. The blog post has since been updated, and the link to the updated blog post is available here: https://blog.group-ib.com/colunmtk_apt41
Please note that SITA’s position is as follows:
• The blog post previously suggested there was a link between the attacks on SITA PSS and Air India (the attack which is further considered in the blog).
• According to SITA’s analysis, none of the methods that the blog suggests were used to attack Air India were employed in the attack on SITA PSS.
• The threat actor that attacked SITA PSS was expelled from our network several weeks before the blog suggests the attack on Air India began.
• SITA’s position is that there is no link between the attack on Air India and the separate attack on SITA PSS, nor were these attacks carried out by the same threat actor.We therefore kindly ask you to amend your article, which was based on the original blog post, accordingly.
SITA Corporate Communications
Some sections of this report are sourced from:
thehackernews.com

 Motives for ransomware attack against nuclear contractor Sol Oriens remain unclear
Motives for ransomware attack against nuclear contractor Sol Oriens remain unclear
Sandro Hofer
SITA would like to clarify a few points regarding your article https://thecybersecurity.news/general-cyber-security-news/chinese-hackers-believed-to-be-behind-sita-air-india-data-breach-10093/ and share SITA’s side of the story.
On 10 June 2021, Group-IB published a blog post, which mentioned SITA, Air India, and a group called APT41. In this blog, Group-IB described with technical detail an alleged cyber-attack on Air India. The blog post has since been updated, and the link to the updated blog post is available here: https://blog.group-ib.com/colunmtk_apt41
Please note that SITA’s position is as follows:
• The blog post previously suggested there was a link between the attacks on SITA PSS and Air India (the attack which is further considered in the blog).
• According to SITA’s analysis, none of the methods that the blog suggests were used to attack Air India were employed in the attack on SITA PSS.
• The threat actor that attacked SITA PSS was expelled from our network several weeks before the blog suggests the attack on Air India began.
• SITA’s position is that there is no link between the attack on Air India and the separate attack on SITA PSS, nor were these attacks carried out by the same threat actor.
We therefore kindly ask you to amend your article, which was based on the original blog post, accordingly.
SITA Corporate Communications
TheCyberSecurity.News
Thank you for your comment. We added your comment to the first post as an update.