A Chinese sophisticated persistent danger tracked as Deep Panda has been noticed exploiting the Log4Shell vulnerability in VMware Horizon servers to deploy a backdoor and a novel rootkit on contaminated devices with the intention of thieving sensitive knowledge.
“The character of targeting was opportunistic insofar that many infections in quite a few countries and many sectors occurred on the identical dates,” explained Rotem Sde-Or and Eliran Voronovitch, researchers with Fortinet’s FortiGuard Labs, in a report released this 7 days. “The victims belong to the money, educational, cosmetics, and travel industries.”
Deep Panda, also acknowledged by the monikers Shell Crew, KungFu Kittens, and Bronze Firestone, is mentioned to have been energetic since at the very least 2010, with recent attacks “focusing on authorized firms for knowledge exfiltration and technology vendors for command-and-command infrastructure creating,” in accordance to Secureworks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Cybersecurity firm CrowdStrike, which assigned the panda-themed name to the group all the way again in July 2014, known as it “a person of the most state-of-the-art Chinese nation-condition cyber intrusion groups.”
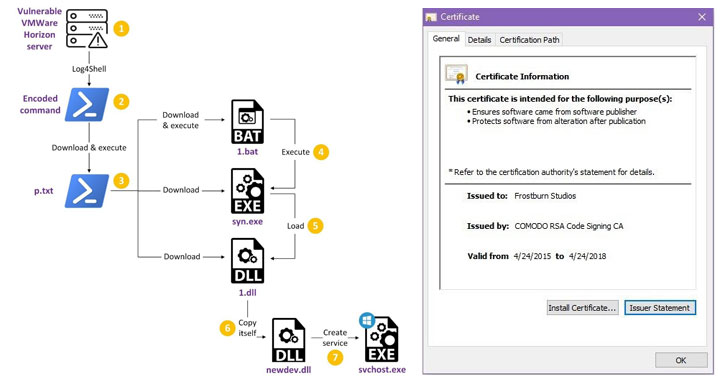
The newest established of attacks documented by Fortinet reveals that the an infection method included the exploitation of the Log4j distant code execution flaw (aka Log4Shell) in vulnerable VMware Horizon servers to spawn a chain of intermediate levels, ultimately foremost to the deployment of a backdoor dubbed Milestone (“1.dll”).
Based on the leaked resource code of the infamous Gh0st RAT but with notable variances in the command-and-handle (C2) communication mechanism used, Milestone is also made to send information about the current classes on the program to the remote server.
Also detected through the attacks is a kernel rootkit named “Fireplace Chili” which is digitally signed with stolen certificates from recreation enhancement organizations, enabling it to evade detection by security software and conceal destructive file operations, processes, registry critical additions, and network connections.
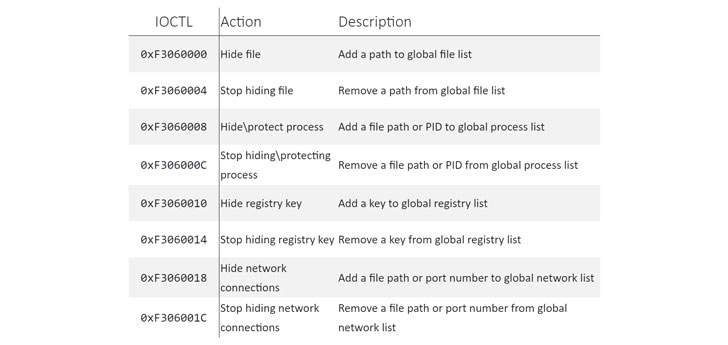
This is achieved by signifies of ioctl (input/output manage) process phone calls to conceal the driver rootkit’s registry essential, the Milestone backdoor information, and the loader file and procedure used to start the implant.
Fortinet’s attribution to Deep Panda stems from overlaps concerning Milestone and Infoadmin RAT, a distant entry trojan utilized by the innovative hacking collective in the early 2010s, with more clues pointing to tactical similarities to that of the Winnti group.
This is backed by the use of compromised digital signatures belonging to gaming organizations, a focus on of option for Winnti, as very well as a C2 area (gnisoft[.]com), which has been previously connected to the Chinese condition-sponsored actor in 2020.
“The motive these applications are connected to two different groups is unclear at this time,” the scientists reported. “It truly is achievable that the groups’ developers shared means, such as stolen certificates and C2 infrastructure, with every other. This may perhaps explain why the samples were being only signed quite a few hrs following remaining compiled.”
The disclosure provides to a extended record of hacking groups that have exploited the Log4Shell vulnerability concentrating on VMware’s virtualization system.
In December 2021, CrowdStrike explained an unsuccessful campaign carried out by an adversary dubbed Aquatic Panda that leveraged the flaw to conduct many submit-exploitation operations, which include reconnaissance and credential harvesting on specific devices.
Due to the fact then, several teams have joined the fray, including the Iranian TunnelVision team, which was observed actively exploiting the Log4j logging library defect to compromise unpatched VMware Horizon servers with ransomware.
Most lately, cybersecurity enterprise Sophos highlighted a slew of attacks in opposition to susceptible Horizon servers that have been ongoing due to the fact January and have been mounted by danger actors to illicitly mine cryptocurrency, install PowerShell-dependent reverse shells, or to deploy Atera brokers to remotely deliver additional payloads.
“Makes an attempt to compromise Horizon servers are among the far more qualified exploits of Log4Shell vulnerabilities simply because of their character,” Sophos researchers mentioned, introducing “platforms this kind of as Horizon are significantly eye-catching targets to all kinds of destructive actors because they are popular and can (if nevertheless susceptible) simply identified and exploited with perfectly-tested applications.”
Located this write-up interesting? Observe THN on Facebook, Twitter and LinkedIn to browse additional distinctive written content we article.
Some parts of this report are sourced from:
thehackernews.com


 Results Overview: 2022 MITRE ATT&CK Evaluation – Wizard Spider and Sandworm Edition
Results Overview: 2022 MITRE ATT&CK Evaluation – Wizard Spider and Sandworm Edition