Scientists have disclosed a new offensive framework named Manjusaka that they phone a “Chinese sibling of Sliver and Cobalt Strike.”
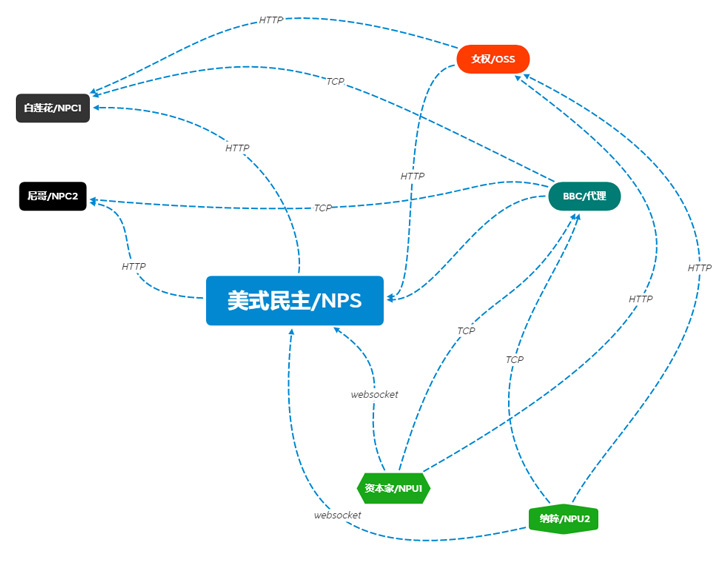
“A absolutely practical version of the command-and-management (C2), composed in GoLang with a Person Interface in Simplified Chinese, is freely readily available and can create new implants with customized configurations with ease, raising the chance of broader adoption of this framework by destructive actors,” Cisco Talos reported in a new report.
Sliver and Cobalt Strike are legitimate adversary emulation frameworks that have been used by menace actors to carry out article-exploitation activities this kind of as network reconnaissance, lateral movement, and facilitating the deployment of adhere to-on payloads.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Penned in Rust, Manjusaka — which means “cow flower” — is advertised as an equal to the Cobalt Strike framework with abilities to focus on both equally Windows and Linux operating programs. Its developer is considered to be situated in the GuangDong location of China.

“The implant consists of a multitude of distant entry trojan (RAT) capabilities that include some common operation and a devoted file administration module,” the researchers noted.
Some of the supported functions involve executing arbitrary instructions, harvesting browser qualifications from Google Chrome, Microsoft Edge, Qihoo 360, Tencent QQ Browser, Opera, Courageous, and Vivaldi, collecting Wi-Fi passwords, capturing screenshots, and getting complete system info.
It is really also built to start the file management module to have out a broad selection of activities this kind of as enumerating information as perfectly as handling documents and directories on the compromised system.
On the other hand, the ELF variant of the backdoor, whilst together with most of the functionalities as its Windows counterpart, isn’t going to include the potential to obtain qualifications from Chromium-based browsers and harvest Wi-Fi login passwords.
Also, element of the Chinese language framework is a C2 server executable that is coded in Golang and is out there on GitHub at “hxxps://github[.]com/YDHCUI/manjusaka.” A 3rd part is an admin panel built on the Gin web framework that enables an operator to create the Rust implant.
The server binary, for its component, is engineered to observe and administer an contaminated endpoint, in addition to building the ideal Rust implants depending on the running technique and issuing the necessary commands.
That mentioned, the chain of evidence suggests that it’s both below lively progress or its parts are provided to other actors as a assistance.

Talos explained it designed the discovery all through its investigation of a maldoc an infection chain that leverages COVID-19-themed lures in China to supply Cobalt Strike beacons on infected units, introducing the same menace actor also utilized the implants from the Manjusaka framework in the wild.
The results get there months following it emerged that malicious actors have been observed abusing yet another legitimate adversary simulation software package termed Brute Ratel (BRc4) in their attacks in an try to stay underneath the radar and evade detection.
“The availability of the Manjusaka offensive framework is an sign of the attractiveness of extensively offered offensive systems with each crimeware and APT operators,” the scientists reported.
“This new attack framework incorporates all the attributes that a person would count on from an implant, on the other hand, it is published in the most modern-day and moveable programming languages. The developer of the framework can quickly integrate new target platforms like MacOSX or a lot more unique flavors of Linux as the kinds working on embedded products.”
Discovered this short article interesting? Comply with THN on Fb, Twitter and LinkedIn to read a lot more exclusive written content we article.
Some components of this article are sourced from:
thehackernews.com

 Google Patches Critical Android Bluetooth Flaw in August Security Bulletin
Google Patches Critical Android Bluetooth Flaw in August Security Bulletin