Following Microsoft’s release of out-of-band patches to handle numerous zero-day flaws in on-premises versions of Microsoft Exchange Server, the U.S. Cybersecurity and Infrastructure Security Company (CISA) has issued an emergency directive warning of “lively exploitation” of the vulnerabilities.
The warn comes on the heels of Microsoft’s disclosure that China-centered hackers ended up exploiting unidentified software program bugs in Trade server to steal delicate knowledge from select targets, marking the 2nd time in four months that the U.S. has scrambled to address a widespread hacking marketing campaign believed to be the get the job done of international threat actors.
Whilst the corporation mainly attributed the marketing campaign to a danger team termed HAFNIUM, Slovakian cybersecurity agency ESET said it found proof of CVE-2021-26855 currently being actively exploited in the wild by several cyber espionage groups, including LuckyMouse, Tick, and Calypso concentrating on servers found in the U.S., Europe, Asia, and the Middle East.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
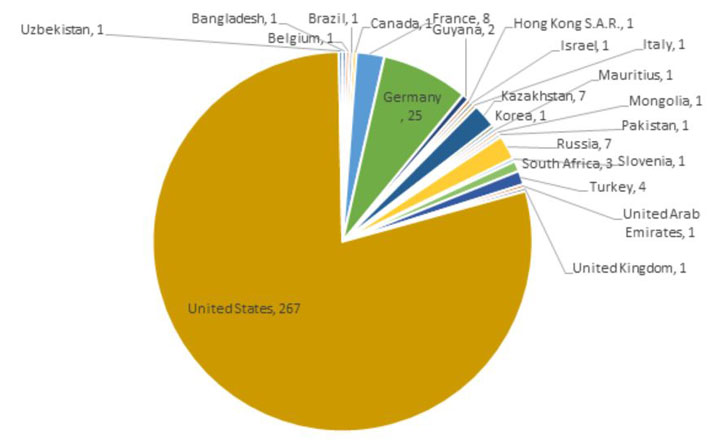
Researchers at Huntress Labs have also sounded the alarm about mass exploitation of Trade servers, noting that about 350 web shells have been found throughout close to 2,000 susceptible servers.
“Among the the susceptible servers, we also identified over 350 web shells — some targets may perhaps have far more than one web shell, probably indicating automated deployment or various uncoordinated actors,” Huntress senior security researcher John Hammond mentioned. “These endpoints do have antivirus or EDR alternatives set up, but this has seemingly slipped earlier a bulk of preventative security items.”
The latest advancement indicates a a lot more substantial spread that extends outside of the “constrained and specific” attack documented by Microsoft before this week.
It can be not obvious if any U.S. government agencies have been breached in the campaign, but the CISA directive underscores the urgency of the menace.
Strongly urging organizations to implement the patches as shortly as probable, the company cited the “probability of prevalent exploitation of the vulnerabilities after community disclosure and the risk that federal govt expert services to the American community could be degraded.”
Found this article interesting? Stick to THN on Facebook, Twitter and LinkedIn to examine a lot more exclusive articles we write-up.
Some pieces of this posting are sourced from:
thehackernews.com


 Hackers, nation-states, target US black community to commit fraud, sow division
Hackers, nation-states, target US black community to commit fraud, sow division