A security vulnerability in Cisco Adaptive Security Equipment (ASA) that was tackled by the organization final October and once more before this April, has been subjected to active in-the-wild attacks pursuing the release of proof-of-strategy (PoC) exploit code.
The PoC was printed by researchers from cybersecurity agency Positive Technologies on June 24, next which reviews emerged that attackers are chasing immediately after an exploit for the bug.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Tenable has also obtained a report that attackers are exploiting CVE-2020-3580 in the wild,” the cyber publicity company explained.
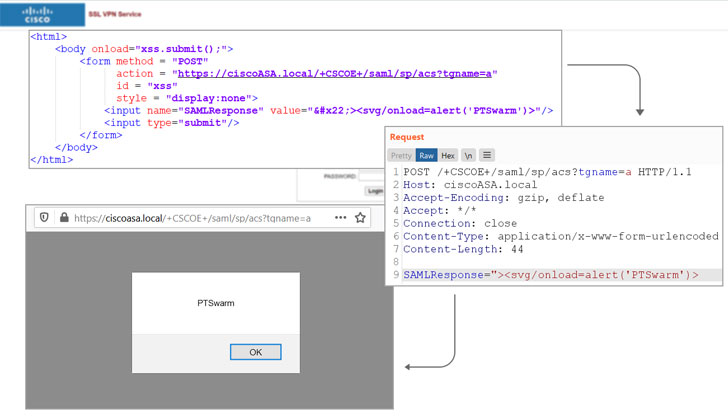
Tracked as CVE-2020-3580 (CVSS score: 6.1), the issue considerations multiple vulnerabilities in the web services interface of Cisco ASA computer software and Cisco Firepower Threat Protection (FTD) software that could let an unauthenticated, remote attacker to carry out cross-site scripting (XSS) attacks on an influenced gadget.
As of July 2020, there had been a little more than 85,000 ASA/FTD units, 398 of which are unfold across 17% of the Fortune 500 corporations, in accordance to cybersecurity organization Rapid7.

Thriving exploitation, such as eventualities in which a person of the interface is certain to click on a specifically-crafted connection, could permit the adversary to execute arbitrary JavaScript code in the context of the interface or entry sensitive, browser-dependent facts.
Even though Cisco remediated the flaw in Oct 2020, the network tools business subsequently determined the resolve be “incomplete,” thus requiring a 2nd spherical of patches that have been produced on April 28, 2021.
In gentle of public PoC availability, it is advised that organizations prioritize patching CVE-2020-3580 to mitigate the risk affiliated with the flaw.
Uncovered this article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to read through far more exceptional written content we post.
Some areas of this article are sourced from:
thehackernews.com


 SolarWinds Hackers Breach Microsoft Customer Support to Target its Customers
SolarWinds Hackers Breach Microsoft Customer Support to Target its Customers