Cisco on Wednesday rolled out patches to deal with 8 security vulnerabilities, three of which could be weaponized by an unauthenticated attacker to get remote code execution (RCE) or induce a denial-of-provider (DoS) situation on impacted devices.
The most critical of the flaws affect Cisco Modest Business enterprise RV160, RV260, RV340, and RV345 Collection routers. Tracked as CVE-2022-20842 (CVSS score: 9.8), the weak point stems from an insufficient validation of person-equipped input to the web-based mostly administration interface of the appliances.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“An attacker could exploit this vulnerability by sending crafted HTTP enter to an afflicted device,” Cisco mentioned in an advisory. “A prosperous exploit could let the attacker to execute arbitrary code as the root user on the fundamental functioning system or lead to the device to reload, ensuing in a DoS affliction.”
A second shortcoming relates to a command injection vulnerability residing in the routers’ web filter database update function (CVE-2022-20827, CVSS score: 9.), which could be exploited by an adversary to inject and execute arbitrary commands on the fundamental operating procedure with root privileges.
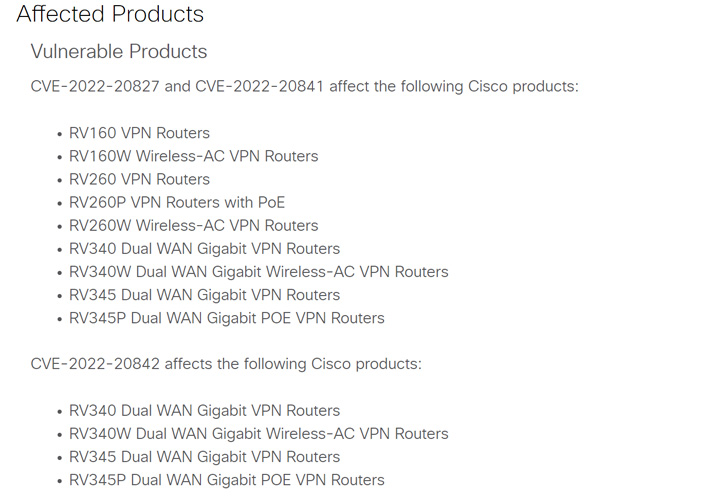
The third router-similar flaw to be fixed (CVE-2022-20841, CVSS rating: 8.) is also a command injection bug in the Open up Plug-n-Perform (PnP) module that could be abused by sending a destructive enter to reach code execution on the qualified Linux host.

“To exploit this vulnerability, an attacker need to leverage a guy-in-the-middle placement or have an proven foothold on a precise network gadget that is linked to the affected router,” the networking equipment maker observed.
Also patched by Cisco are five medium security flaws impacting Webex Meetings, Identity Providers Engine, Unified Communications Manager, and BroadWorks Application Shipping and delivery System.
The organization supplied no workarounds to remediate the issues, introducing there is no proof of these vulnerabilities currently being exploited in the wild. That said, clients are encouraged to transfer swiftly to utilize the updates.
Found this short article interesting? Adhere to THN on Fb, Twitter and LinkedIn to read through more unique content material we submit.
Some sections of this post are sourced from:
thehackernews.com


 Large-Scale Phishing Attacks Targeting Microsoft Enterprise Email Services
Large-Scale Phishing Attacks Targeting Microsoft Enterprise Email Services