Cisco yesterday unveiled security patches for two large-severity vulnerabilities influencing its IOS XR application that had been uncovered exploited in the wild a month ago.
Tracked as CVE-2020-3566 and CVE-2020-3569, aspects for equally zero-working day unauthenticated DoS vulnerabilities ended up designed public by Cisco late final month when the company located hackers actively exploiting Cisco IOS XR Software program that is mounted on a vary of Cisco’s carrier-grade and facts middle routers.
The two DoS vulnerabilities resided in Cisco IOS XR Software’s Distance Vector Multicast Routing Protocol (DVMRP) characteristic and existed owing to incorrect implementation of queue management for Internet Team Management Protocol (IGMP) packets on afflicted units.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

IGMP is a interaction protocol typically utilised by hosts and adjacent routers to proficiently use assets for multicasting apps when supporting streaming material these types of as on line video clip streaming and gaming.
“These vulnerabilities have an impact on any Cisco system that is jogging any release of Cisco IOS XR Program if an lively interface is configured below multicast routing and it is receiving DVMRP targeted traffic,” Cisco reported in an advisory.
“An administrator can decide whether or not multicast routing is enabled on a product by issuing the present igmp interface command.”
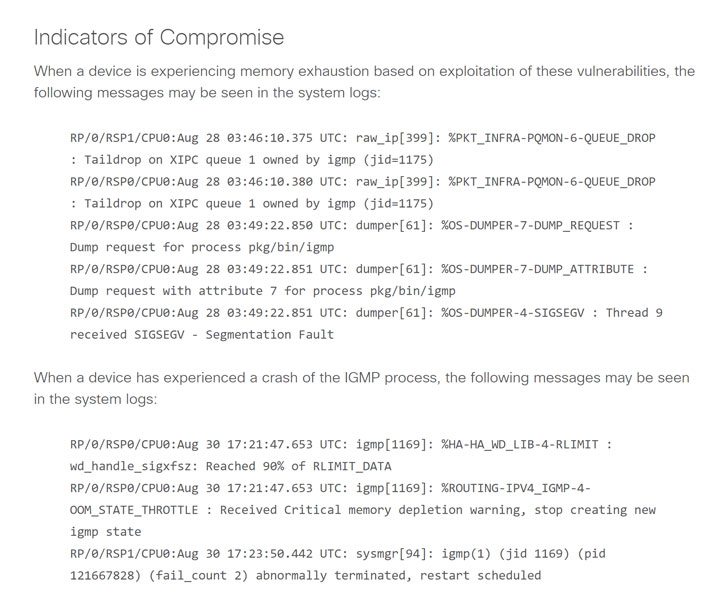
Productive exploitation of these vulnerabilities could make it possible for distant unauthenticated hackers to deliver specifically crafted IGMP packets to influenced equipment to possibly instantly crash the IGMP approach or exhaust system memory and at some point crash.
The memory usage may well negatively final result in instability of other processes running on the gadget, like routing protocols for equally interior and external networks.
The vulnerabilities impact all Cisco devices managing any launch of Cisco IOS XR Computer software if an lively interface is configured underneath multicast routing, and it is acquiring DVMRP traffic.
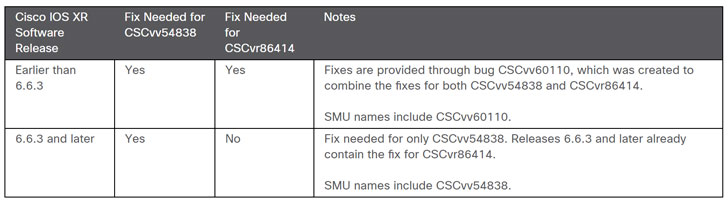
At the time Cisco in the beginning produced these vulnerabilities general public, the enterprise offered some mitigation to take care of the issues and block the active exploitation attempts, but now it has ultimately launched Computer software Routine maintenance Updates (SMUs) to handle the vulnerabilities totally.
“Despite the fact that there are no workarounds for these vulnerabilities, there are several mitigations available to consumers dependent on their requirements,” the company claimed.
“When thinking about mitigations, it really should be recognized that for the memory exhaustion circumstance, the rate limiter and the access control approaches are productive. For the fast IGMP system crash circumstance, only the entry regulate process is efficient.”
Cisco prospects are highly suggested to make certain they are managing the latest Cisco IOS XR Software program release previously than 6.6.3 and Cisco IOS XR Software program release 6.6.3 and afterwards.
Observed this article appealing? Abide by THN on Fb, Twitter and LinkedIn to study much more special articles we put up.
Some parts of this article is sourced from:
thehackernews.com


 One in Three Not Worried About Cybersecurity Despite Rise in Threats
One in Three Not Worried About Cybersecurity Despite Rise in Threats