Cisco has at the time once again preset four earlier disclosed critical bugs in its Jabber video conferencing and messaging app that were inadequately dealt with, leaving its consumers susceptible to distant attacks.
The vulnerabilities, if efficiently exploited, could allow for an authenticated, remote attacker to execute arbitrary code on target programs by sending specially-crafted chat messages in team conversations or precise persons.
They were reported to the networking tools maker on September 25 by Watchcom, a few months after the Norwegian cybersecurity organization publicly disclosed multiple security shortcomings in Jabber that were observed all through a penetration exam for a customer in June.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The new flaws, which were being uncovered right after a person of its clients asked for a verification audit of the patch, has an effect on all at present supported versions of the Cisco Jabber consumer (12.1 – 12.9).
“3 of the four vulnerabilities Watchcom disclosed in September have not been sufficiently mitigated,” Watchcom said in a report printed nowadays. “Cisco introduced a patch that set the injection factors we noted, but the underlying trouble has not been mounted. As these, we had been able to 7ind new injection details that could be made use of to exploit the vulnerabilities.”
Most critical between the flaws is CVE-2020-26085 (identical to CVE-2020-3495), which has a severity ranking of 9.9 out of 10, a zero-simply click cross-web page scripting (XSS) vulnerability that can be used to achieve remote code execution by escaping the CEF sandbox.
CEF or Chromium Embedded Framework is an open-resource framework that’s employed to embed a Chromium-dependent web browser inside of other apps.
When the embedded browser is sandboxed to stop unauthorized access to information, the scientists found a way to bypass the protections by abusing the window.CallCppFunction, which is created to open up data files despatched by other Cisco Jabber end users.
All an adversary has to do is initiate a file transfer made up of a destructive “.exe” file and drive the sufferer to settle for it employing an XSS attack, then trigger a call to the aforementioned function, leading to the executable to be run on the victim’s machine.
Worse, this vulnerability does not demand consumer interaction and is wormable, meaning it can be utilised to automatically distribute the malware to other units by disguising the payload in a chat message.
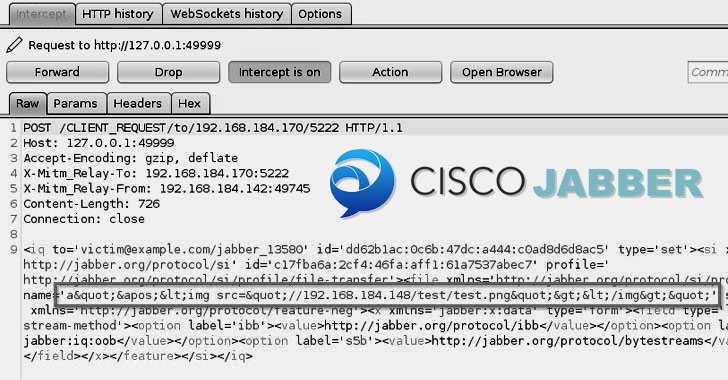
A second flaw, CVE-2020-27132, stems from the way it parses HTML tags in XMPP messages, an XML-based mostly communications protocol utilised for facilitating fast messaging amongst any two or additional network entities.
Because of to the absence of appropriate sanitization of these tags, a harmless file transfer information can be manipulated by injecting, say, an image HTML tag pointing to a malicious URL or even execute malicious JavaScript code.
“No additional security actions had been put in spot and it was therefore doable to both equally acquire remote code execution and steal NTLM password hashes working with this new injection point,” the researchers stated.
The 3rd and final vulnerability (CVE-2020-27127) is a command injection flaw regarding protocol handlers, which are employed to advise the working system to open up distinct URLs (e.g., XMPP://, IM://, and TEL://) in Jabber, creating it possible for an attacker to insert arbitrary command-line flags by simply together with a space the URL.
Supplied the self-replicating nature of the attacks, it is advised that Jabber consumers update to the latest version of the software program to mitigate the risk.
Watchcom also suggests that corporations contemplate disabling conversation with external entities by means of Cisco Jabber until eventually all workers have installed the update.
Identified this posting appealing? Observe THN on Fb, Twitter and LinkedIn to browse more special articles we submit.
Some parts of this report are sourced from:
thehackernews.com

 Cyber Helpline Receives Lottery Funding to Help Growing Number of Victims
Cyber Helpline Receives Lottery Funding to Help Growing Number of Victims