Web infrastructure and website security firm Cloudflare final month mounted a critical vulnerability in its CDNJS library that’s employed by 12.7% of all internet sites on the internet.
CDNJS is a free and open-supply content shipping and delivery network (CDN) that serves about 4,041 JavaScript and CSS libraries, generating it the second most well known CDN for JavaScript following Google Hosted Libraries.
The weak point anxious an issue in the CDNJS library update server that could likely allow for an attacker to execute arbitrary commands, top to a full compromise.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The vulnerability was found out and documented by security researcher RyotaK on April 6, 2021. There is no evidence of in-the-wild attacks abusing this flaw.
Particularly, the vulnerability functions by publishing packages to Cloudflare’s CDNJS working with GitHub and npm, employing it to trigger a route traversal vulnerability, and ultimately trick the server into executing arbitrary code, as a result accomplishing remote code execution.
It’s well worth noting that the CDNJS infrastructure features characteristics to automate library updates by periodically running scripts on the server to obtain appropriate documents from the respective consumer-managed Git repository or npm deal registry.
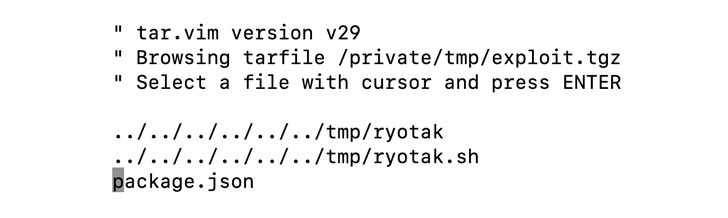
By uncovering an issue with how the system sanitizes offer paths, RyotaK observed that “arbitrary code can be executed following accomplishing path traversal from the .tgz file printed to npm and overwriting the script that is executed on a regular basis on the server.”
In other text, the intention of the attack is to publish a new edition of a specifically-crafted package to the repository, which is then picked up the CDNJS library update server for publishing, in the approach copying the contents of the destructive package into a regularly executed script file hosted on the server, therefore gaining arbitrary code execution.

“Though this vulnerability could be exploited devoid of any particular expertise, it could impression numerous websites,” RyotaK reported. “Specified that there are several vulnerabilities in the offer chain, which are simple to exploit but have a huge affect, I come to feel that it is really very frightening.”
This is not the initial time the security researcher has uncovered critical flaws in the way updates to software repositories are taken care of. In April 2021, RyotaK disclosed a critical vulnerability in the formal Homebrew Cask repository could have been exploited by an attacker to execute arbitrary code on users’ devices.
Observed this short article fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to study extra exceptional articles we post.
Some pieces of this write-up are sourced from:
thehackernews.com


 Linux Variant of HelloKitty Ransomware Targets VMware ESXi Servers
Linux Variant of HelloKitty Ransomware Targets VMware ESXi Servers