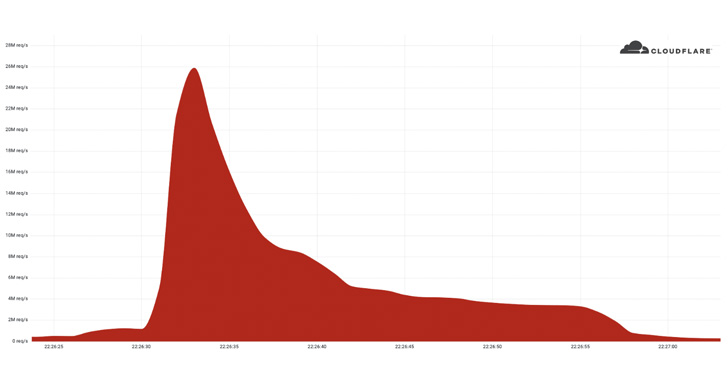
Cloudflare on Tuesday disclosed that it had acted to avoid a document-placing 26 million ask for for every 2nd (RPS) distributed denial-of-service (DDoS) attack past 7 days, generating it the biggest HTTPS DDoS attack detected to date.
The web performance and security enterprise mentioned the attack was directed from an unnamed buyer internet site applying its Free of charge plan and emanated from a “effective” botnet of 5,067 devices, with each node generating about 5,200 RPS at peak.
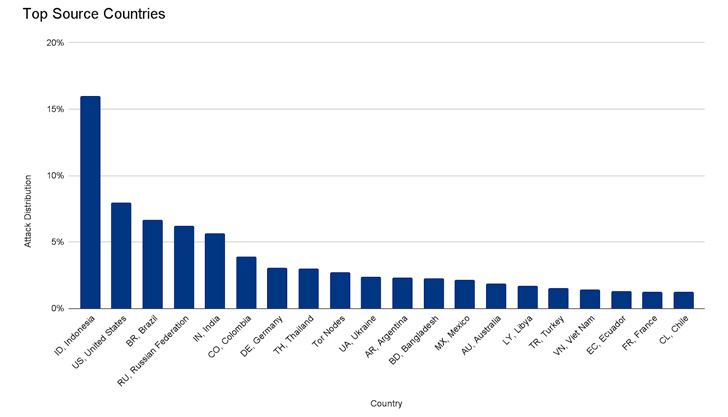
The botnet is explained to have established a flood of additional than 212 million HTTPS requests within just fewer than 30 seconds from more than 1,500 networks in 121 nations, which includes Indonesia, the U.S., Brazil, Russia, and India. Roughly 3% of the attack arrived as a result of Tor nodes.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The attack “originated typically from Cloud Support Providers as opposed to Household Internet Services Suppliers, indicating the use of hijacked virtual machines and highly effective servers to crank out the attack — as opposed to a great deal weaker Internet of Matters (IoT) gadgets,” Cloudflare’s Omer Yoachimik reported.
Launching HTTPS-centered DDoS attacks tend to be a lot more expensive computationally owing to the better expense affiliated with developing a safe TLS encrypted link.
This is the second such volumetric HTTPS DDoS attack to be thwarted by Cloudflare in as a lot of months. In late April 2022, it reported it staved off a 15.3 million RPS HTTPS DDoS attack aimed at a consumer working a crypto launchpad.
In accordance to the company’s DDoS attack tendencies report for Q1 2022, volumetric DDoS attacks in excess of 100 gigabits for each next (gbps) surged by up to 645% quarter-on-quarter.

“Attacks with substantial bit costs try to trigger a denial-of-assistance party by clogging the Internet backlink, while attacks with substantial packet premiums try to overwhelm the servers, routers, or other in-line components appliances,” the scientists claimed.
“In this kind of a situation, packets are ‘dropped,’ i.e., the appliance is not able to procedure them. For customers, this benefits in service disruptions and denial of company.”
Identified this write-up interesting? Follow THN on Fb, Twitter and LinkedIn to go through extra exceptional content we put up.
Some parts of this article are sourced from:
thehackernews.com

 Patch Tuesday: Microsoft Issues Fix for Actively Exploited ‘Follina’ Vulnerability
Patch Tuesday: Microsoft Issues Fix for Actively Exploited ‘Follina’ Vulnerability