Unknown risk actors breached a server functioning an unpatched, 11-yr-aged edition of Adobe’s ColdFusion 9 software program in minutes to remotely consider in excess of manage and deploy file-encrypting Cring ransomware on the target’s network 79 hours just after the hack.
The server, which belonged to an unnamed solutions business, was made use of to collect timesheet and accounting information for payroll as well as to host a amount of virtual machines, according to a report posted by Sophos and shared with The Hacker Information. The attacks originated from an internet address assigned to the Ukrainian ISP Green Floid.
“Products functioning susceptible, outdated program are very low-hanging-fruit for cyberattackers hunting for an simple way into a focus on,” Sophos principal researcher Andrew Brandt said. “The astonishing matter is that this server was in lively day-to-day use. Often the most vulnerable devices are inactive or ghost devices, either neglected about or forgotten when it will come to patching and updates.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The British security program firm reported the “quick break-in” was built probable by exploiting an 11-12 months-aged installation of Adobe ColdFusion 9 working on Windows Server 2008, both equally of which have achieved close-of-daily life.
On getting an initial foothold, the attackers utilised a huge range of innovative strategies to conceal their data files, inject code into memory, and go over their tracks by overwriting files with garbled details, not to mention disarm security goods by capitalizing on the point that tamper-security functionalities were turned off.
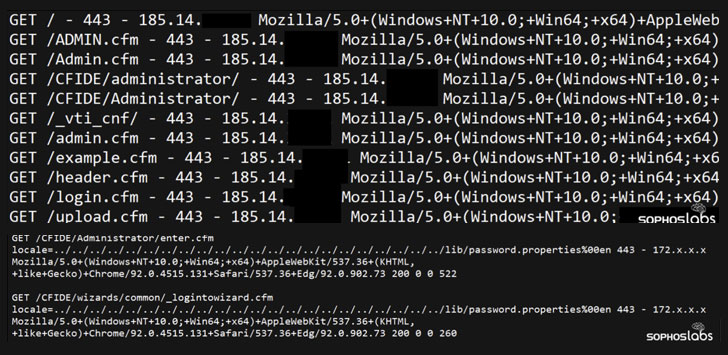
Specially, the adversary took advantage of CVE-2010-2861, a set of directory traversal vulnerabilities in the administrator console in Adobe ColdFusion 9..1 and earlier that could be abused by distant attackers to browse arbitrary data files, these kinds of as individuals made up of administrator password hashes (“password.attributes”).

In the future stage, the undesirable actor is considered to have exploited an additional vulnerability in ColdFusion, CVE-2009-3960, to upload a destructive Cascading Stylesheet (CSS) file to the server, for that reason applying it to load a Cobalt Strike Beacon executable. This binary, then, acted as a conduit for the distant attackers to fall more payloads, produce a user account with admin privileges, and even disable endpoint protection systems and anti-malware engines like Windows Defender, ahead of commencing the encryption procedure.
“This is a stark reminder that IT directors advantage from obtaining an correct inventory of all their connected assets and can’t go away out-of-day critical enterprise techniques facing the community internet,” Brandt mentioned. “If businesses have these units anyplace on their network, they can be positive that cyberattackers will be captivated to them.”
Uncovered this article exciting? Comply with THN on Facebook, Twitter and LinkedIn to browse a lot more exceptional written content we post.
Some elements of this write-up are sourced from:
thehackernews.com


 BlackMatter demands $5.9 million ransom from Iowa farm cooperative
BlackMatter demands $5.9 million ransom from Iowa farm cooperative