Three significant-impression security vulnerabilities have been disclosed in APC Sensible-UPS devices that could be abused by distant adversaries as a physical weapon to obtain and manage them in an unauthorized method.
Collectively dubbed TLStorm, the flaws “enable for full distant takeover of Sensible-UPS gadgets and the means to have out extraordinary cyber-actual physical attacks,” Ben Seri and Barak Hadad, scientists from IoT security corporation Armis, reported in a report posted Tuesday.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Uninterruptible electric power offer (UPS) products functionality as crisis backup electric power providers in mission-critical environments these as clinical facilities, server rooms, and industrial programs. Most of the afflicted units, totaling about 20 million, have been identified so considerably in healthcare, retail, industrial, and governing administration sectors.
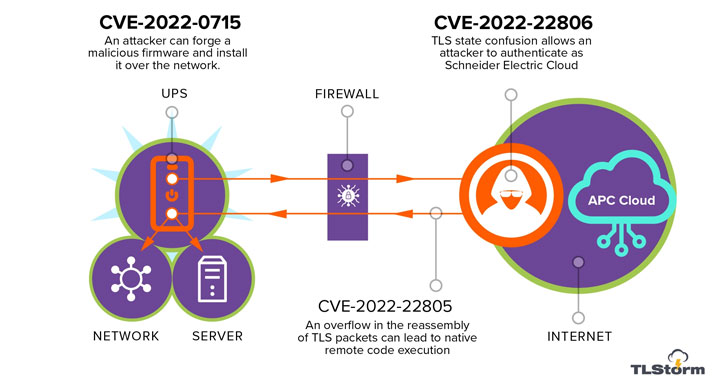
TLStorm is composed of a trio of critical flaws that can be activated through unauthenticated network packets without having requiring any user conversation, indicating it’s a zero-click attack, with two of the issues involving a scenario of defective TLS handshake in between the UPS and the APC cloud –
- CVE-2022-22805 (CVSS rating: 9.) – TLS buffer overflow
- CVE-2022-22806 (CVSS score: 9.) – TLS authentication bypass
- CVE-2022-0715 (CVSS score: 8.9) – Unsigned firmware enhance that can be current more than the network
Thriving exploitation of any of the flaws could outcome in remote code execution (RCE) attacks on vulnerable gadgets, which in flip could be weaponized to tamper with the operations of the UPS to bodily hurt the system or other belongings connected to it.
“By working with our RCE vulnerability we have been ready to bypass the software package safety and let the recent spike periods run above and in excess of until finally the DC backlink capacitor heated up to ~150 levels celsius (~300F), which brought on the capacitor to burst and brick the UPS in a cloud of electrolyte gas, resulting in collateral hurt to the gadget,” the researchers discussed.
To make issues worse, the flaw in the firmware up grade mechanism could be leveraged to plant a destructive update on UPS units, enabling the attackers to set up persistence for extended intervals of time and use the compromised host as a gateway for more attacks.
“Abusing flaws in firmware update mechanisms is starting to be a common apply of APTs, as has been not too long ago detailed in the examination of the Cyclops Blink malware, and inappropriate signing of firmwares of embedded devices is a recurring flaw in many embedded systems,” the researchers stated.
Subsequent dependable disclosure to Schneider Electrical on Oct 31, 2021, fixes have been launched as portion of Patch Tuesday updates on March 8, 2022. Clients are suggested to set up the updates supplied to lessen the risk of productive exploitation of these vulnerabilities.
“UPS units, like a lot of other digital infrastructure appliances, are normally put in and neglected,” the scientists concluded. “Due to the fact these equipment are linked to the exact inside networks as the main small business systems, exploitation tries can have severe implications.”
Located this short article appealing? Observe THN on Fb, Twitter and LinkedIn to read more unique content we write-up.
Some parts of this posting are sourced from:
thehackernews.com



 Over half of London councils lack cyber insurance
Over half of London councils lack cyber insurance