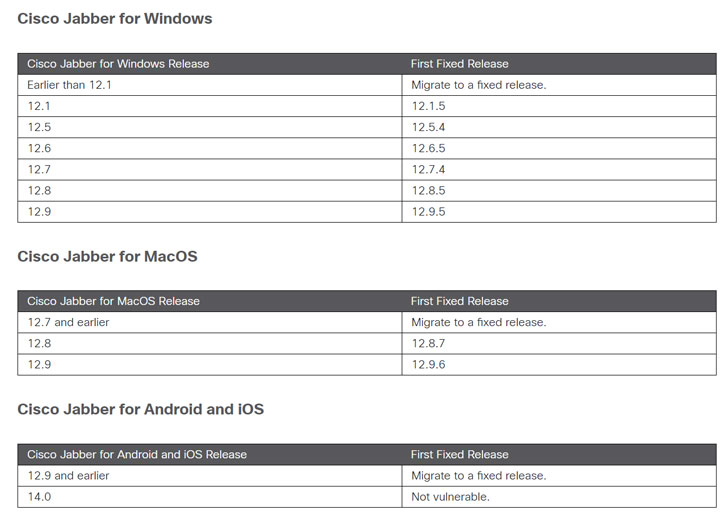
Cisco on Wednesday launched software program updates to deal with various vulnerabilities affecting its Jabber messaging purchasers throughout Windows, macOS, Android, and iOS.
Productive exploitation of the flaws could allow an “attacker to execute arbitrary applications on the underlying running method with elevated privileges, entry sensitive information, intercept shielded network targeted visitors, or trigger a denial of support (DoS) problem,” the networking major claimed in an advisory.
The issues concern a full of five security vulnerabilities, a few of which (CVE-2021-1411, CVE-2021-1417, and CVE-2021-1418) ended up noted to the organization by Olav Sortland Thoresen of Watchcom, with two many others (CVE-2021-1469 and CVE-2021-1471) uncovered for the duration of interior security testing.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Cisco notes that the flaws are not dependent on a single a further, and that exploitation of any just one of the vulnerabilities won’t hinge on the exploitation of another. But in purchase to do this, an attacker requires to be authenticated to an Extensible Messaging and Presence Protocol (XMPP) server working the vulnerable software program, as well as be in a position to ship XMPP messages.
CVE-2021-1411, which concerns an arbitrary system execution vulnerability in its Windows app, is also the most critical, with a CVSS rating of 9.9 out of a highest of 10. According to Cisco, the flaw is thanks to incorrect validation of concept material, consequently making it attainable for an attacker to deliver specifically-crafted XMPP messages to the vulnerable customer and execute arbitrary code with the similar privileges as that of the user account jogging the application.
Other than CVE-2021-1411, 4 other Jabber flaws have also been fastened by Cisco, counting —
- CVE-2021-1469 (Windows) – An issue with inappropriate validation of concept content that could final result in arbitrary code execution.
- CVE-2021-1417 (Windows) – A failure to validate message content that could be leveraged to leak sensitive information, which can then fuel further more attacks.
- CVE-2021-1471 (Windows, macOS, Android, iOS) – A certification validation vulnerability that could be abused to intercept network requests and even modify connections concerning the Jabber shopper and a server
- CVE-2021-1418 (Windows, macOS, Android, iOS) – An issue arising from poor validation of information articles that could be exploited by sending crafted XMPP messages to induce a denial-of-services (DoS) situation.
This is far from the very first time Norwegian cybersecurity firm Watchcom has uncovered flaws in Jabber purchasers. In September 2020, Cisco solved 4 flaws in its Windows app that could allow an authenticated, distant attacker to execute arbitrary code. But following 3 of the 4 vulnerabilities have been not “sufficiently mitigated,” the business ended up releasing the second round of patches in December.
In addition to the correct for Jabber, Cisco has also released 37 other advisories that go into depth about security updates for a variety of medium and substantial severity security issues impacting several Cisco goods.
Observed this posting intriguing? Follow THN on Facebook, Twitter and LinkedIn to study far more unique written content we publish.
Some areas of this post are sourced from:
thehackernews.com


 FatFace Faces Customer Anger After Controversial Breach Response
FatFace Faces Customer Anger After Controversial Breach Response