Practically 10 days immediately after software security company F5 Networks introduced patches for critical vulnerabilities in its Huge-IP and Massive-IQ products and solutions, adversaries have started opportunistically mass scanning and concentrating on exposed and unpatched networking units to crack into business networks.
News of in the wild exploitation improvement arrives on the heels of a proof-of-principle exploit code that surfaced on the internet before this week by reverse-engineering the Java software patch in Significant-IP. The mass scans are claimed to have spiked due to the fact March 18.
The flaws impact Huge-IP versions 11.6 or 12.x and newer, with a critical distant code execution (CVE-2021-22986) also impacting Major-IQ variations 6.x and 7.x. CVE-2021-22986 (CVSS rating: 9.8) is notable for the actuality that it truly is an unauthenticated, remote command execution vulnerability affecting the iControl Relaxation interface, enabling an attacker to execute arbitrary process commands, build or delete documents, and disable expert services without having the will need for any authentication.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Productive exploitation of these vulnerabilities could direct to a total compromise of susceptible methods, together with the probability of distant code execution as effectively as result in a buffer overflow, leading to a denial of service (DoS) attack.
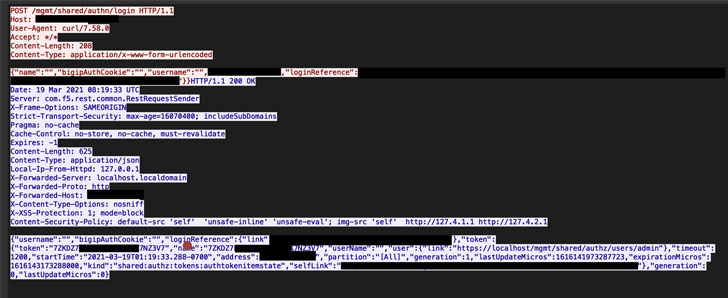
Even though F5 said it not knowledgeable of any public exploitation of these issues on March 10, scientists from NCC Team stated they have now located proof of “total chain exploitation of F5 Significant-IP/Major-IQ iControl Rest API vulnerabilities CVE-2021-22986” in the wake of many exploitation makes an attempt in opposition to its honeypot infrastructure.
In addition, Palo Alto Networks’ Device 42 menace intelligence group mentioned it located attempts to exploit CVE-2021-22986 to set up a variant of the Mirai botnet. But it can be not instantly crystal clear if those people attacks ended up profitable.
Presented the popularity of Large-IP/Massive-IQ in company and governing administration networks, it should arrive as no surprise that this is the 2nd time in a yr F5 appliances have turn into a valuable focus on for exploitation.
Past July, the organization dealt with a similar critical flaw (CVE-2020-5902), following which it was abused by Iranian and Chinese condition-sponsored hacking groups, prompting the U.S. Cybersecurity and Infrastructure Security Company (CISA) to issue an warn cautioning of a “broad scanning action for the presence of this vulnerability across federal departments and agencies.”
“The bottom line is that [the flaws] have an effect on all Major-IP and Massive-IQ prospects and circumstances — we urge all buyers to update their Massive-IP and Significant-IQ deployments to the set variations as shortly as probable,” F5 Senior Vice President Kara Sprague mentioned past 7 days.
Observed this posting exciting? Stick to THN on Facebook, Twitter and LinkedIn to read through additional special information we write-up.
Some elements of this report are sourced from:
thehackernews.com


 CopperStealer malware infected up to 5,000 hosts per day over first three months of 2021
CopperStealer malware infected up to 5,000 hosts per day over first three months of 2021