Cisco Programs on Wednesday issued patches to deal with a critical security vulnerability affecting the Software Plan Infrastructure Controller (APIC) interface made use of in its Nexus 9000 Collection Switches that could be possibly abused to go through or create arbitrary files on a vulnerable procedure.
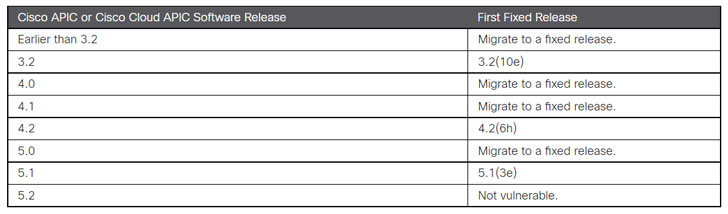
Tracked as CVE-2021-1577 (CVSS rating: 9.1), the issue — which is thanks to poor access control — could help an unauthenticated, remote attacker to add a file to the appliances. ” A profitable exploit could allow for the attacker to read through or compose arbitrary documents on an influenced device,” the business stated in an advisory.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The APIC appliance is a centralized, clustered controller that programmatically automates network provisioning and control based mostly on the application prerequisites and policies throughout physical and digital environments.
Cisco reported it found out the vulnerability all through inner security tests by the Cisco Highly developed Security Initiatives Team (ASIG).
Also, the network machines main reported it concluded its investigation into a new BadAlloc flaw in BlackBerry’s QNX genuine-time functioning procedure, reported on August 17 by the Canadian firm. “Cisco has done its investigation into its product line to establish which products may possibly be affected by this vulnerability. No merchandise are known to be influenced,” it mentioned.

Cisco solutions that operate QNX are stated underneath –
- Channelized shared port adapters (SPAs) (CSCvz34866)
- Circuit Emulation more than Packet (CEoP) SPAs (CSCvz34865)
- IOS XR 32-bit Software program (CSCvz34871)
- RF Gateway 10 (CSCvz34869)
Located this write-up appealing? Follow THN on Fb, Twitter and LinkedIn to go through extra distinctive written content we publish.
Some parts of this article are sourced from:
thehackernews.com


 Cisco Issues Critical Fixes for High-End Nexus Gear
Cisco Issues Critical Fixes for High-End Nexus Gear