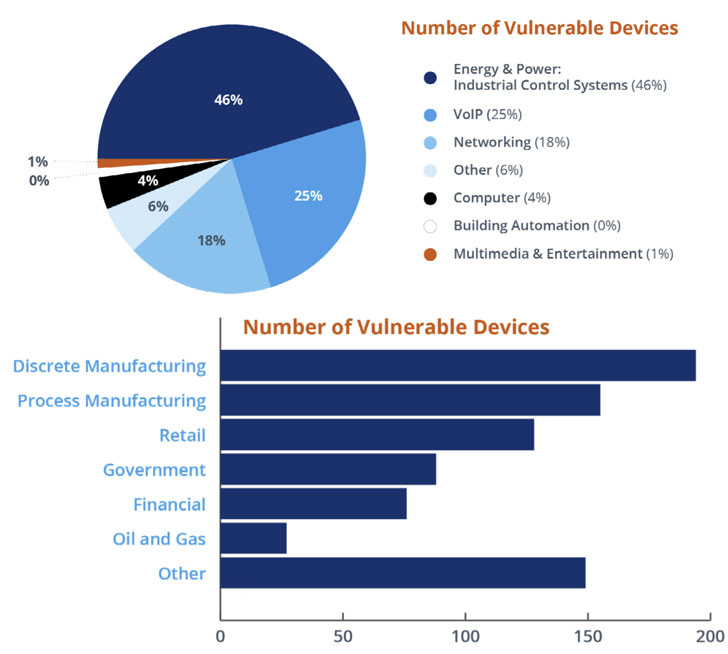
Cybersecurity scientists on Wednesday disclosed 14 vulnerabilities influencing a usually-made use of TCP/IP stack employed in millions of Operational Technology (OT) equipment manufactured by no much less than 200 distributors and deployed in producing crops, power generation, h2o treatment method, and critical infrastructure sectors.
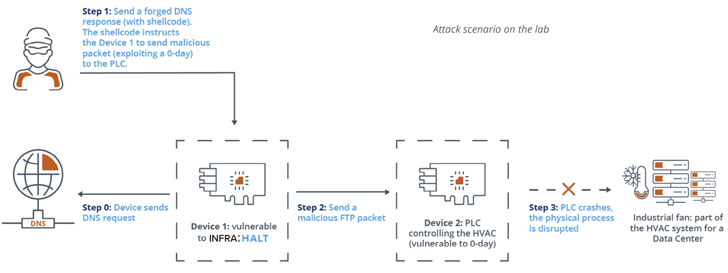
The shortcomings, collectively dubbed “INFRA:HALT,” concentrate on NicheStack, possibly enabling an attacker to accomplish remote code execution, denial of assistance, information leak, TCP spoofing, and even DNS cache poisoning.
NicheStack (aka InterNiche stack) is a shut-source TCP/IP stack for embedded methods that is developed to supply internet connectivity industrial equipment, and is incorporated by important industrial automation vendors like Siemens, Emerson, Honeywell, Mitsubishi Electric powered, Rockwell Automation, and Schneider Electrical in their programmable logic controllers (PLCs) and other solutions.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Attackers could disrupt a building’s HVAC process or take above the controllers employed in manufacturing and other critical infrastructure,” researchers from JFrog and Forescout stated in a joint report posted these days. “Thriving attacks can consequence in using OT and ICS gadgets offline and having their logic hijacked. Hijacked products can distribute malware to in which they talk on the network.”
All variations of NicheStack just before model 4.3 are susceptible to INFRA:HALT, with approximately 6,400 OT gadgets uncovered on the net and linked to the internet as of March 2021, most of which are found in Canada, the U.S., Spain, Sweden, and Italy.
The listing of 14 flaws is as follows –
- CVE-2020-25928 (CVSS rating: 9.8) – An out-of-bounds study/publish when parsing DNS responses, top to remote code execution
- CVE-2021-31226 (CVSS rating: 9.1) – A heap buffer overflow flaw when parsing HTTP publish requests, leading to remote code execution
- CVE-2020-25927 (CVSS score: 8.2) – An out-of-bounds read through when parsing DNS responses, main to denial-of-service
- CVE-2020-25767 (CVSS score: 7.5) – An out-of-bounds study when parsing DNS area names, foremost to denial-of-services and data disclosure
- CVE-2021-31227 (CVSS score: 7.5) – A heap buffer overflow flaw when parsing HTTP article requests, leading to denial-of-assistance
- CVE-2021-31400 (CVSS rating: 7.5) – An infinite loop state of affairs in the TCP out of band urgent info processing function, producing a denial-of-services
- CVE-2021-31401 (CVSS rating: 7.5) – An integer overflow flaw in the TCP header processing code
- CVE-2020-35683 (CVSS score: 7.5) – An out-of-bounds browse when parsing ICMP packets, major to denial-of-service
- CVE-2020-35684 (CVSS score: 7.5) – An out-of-bounds study when parsing TCP packets, primary to denial-of-provider
- CVE-2020-35685 (CVSS score: 7.5) – Predictable first sequence figures (ISNs) in TCP connections, leading to TCP spoofing
- CVE-2021-27565 (CVSS score: 7.5) – A denial-of-services condition on receiving an unidentified HTTP request
- CVE-2021-36762 (CVSS rating: 7.5) – An out-of-bounds browse in the TFTP packet processing perform, top to denial-of-service
- CVE-2020-25926 (CVSS rating: 4.) – The DNS consumer does not set adequately random transaction IDs, resulting in cache poisoning
- CVE-2021-31228 (CVSS rating: 4.) – The supply port of DNS queries can be predicted to deliver cast DNS response packets, resulting in cache poisoning

The disclosures mark the sixth time security weaknesses have been determined in the protocol stacks that underpin hundreds of thousands of internet-related gadgets. It truly is also the fourth established of bugs to be uncovered as portion of a systematic investigation analyze termed Job Memoria to research the security of widely-used TCP/IP stacks that are integrated by various distributors in their firmware to present internet and network connectivity characteristics –
- URGENT/11
- Ripple20
- AMNESIA:33
- Variety:JACK
- Name:WRECK
HCC Embedded, which maintains the C library, has unveiled program patches to deal with the issues. “Total protection towards INFRA:HALT demands patching susceptible equipment but is tough owing to supply chain logistics and the critical mother nature of OT gadgets,” the researchers mentioned.
As mitigations, Forescout has released an open up-resource script that works by using energetic fingerprinting to detect devices working NicheStack. It is really also recommended to implement segmentation controls, check all network visitors for malicious packets to mitigate the risk from vulnerable units.
Found this report fascinating? Comply with THN on Facebook, Twitter and LinkedIn to browse a lot more distinctive material we article.
Some pieces of this report are sourced from:
thehackernews.com


 We COVID-Clicked on Garbage, Report Finds: Podcast
We COVID-Clicked on Garbage, Report Finds: Podcast