Cybersecurity scientists have disclosed new security vulnerabilities in the Etherpad textual content editor (variation 1.8.13) that could most likely enable attackers to hijack administrator accounts, execute system commands, and even steal sensitive files.
The two flaws — tracked as CVE-2021-34816 and CVE-2021-34817 — were being found out and claimed on June 4 by scientists from SonarSource, subsequent which patches have been transported for the latter in model 1.8.14 of Etherpad released on July 4.
Etherpad is a serious-time collaborative interface that permits a document to be edited concurrently by numerous authors. It is an open up-resource alternate to Google Docs that can be hosted on your individual servers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The XSS vulnerability enables attackers to consider in excess of Etherpad users, together with admins. This can be utilised to steal or manipulate delicate data,” SonarSource vulnerability researcher Paul Gerste explained in a report shared with The Hacker Information.

“The argument injection vulnerability will allow attackers to execute arbitrary code on the server, which would enable [them] to steal, modify or delete all info, or to target other inside systems that are reachable from the server.”
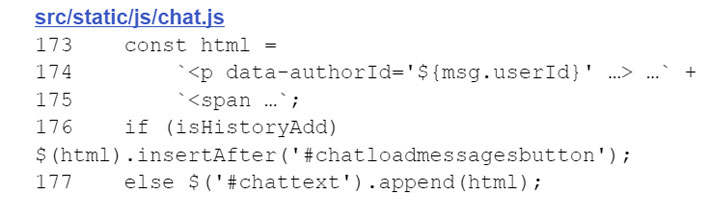
Precisely, the XSS vulnerability (CVE-2021-34817) resides in the chat aspect made available by Etherpad, with the “userId” house of a chat message — i.e., a unique identifier linked with a document creator — rendered on the entrance-finish without the need of correctly escaping unique figures, as a result permitting an adversary to insert a destructive JavaScript payload into the chat background and conduct actions as a victim consumer.
CVE-2021-34816, on the other hand, relates to how Etherpad manages plugins, whereby the identify of the bundle to be mounted through the “npm install” command is not adequately sanitized, primary to a scenario that could allow for an attacker to “specify a destructive package deal from the NPM repository or to basically use a URL that points to a bundle on the attacker’s server.”
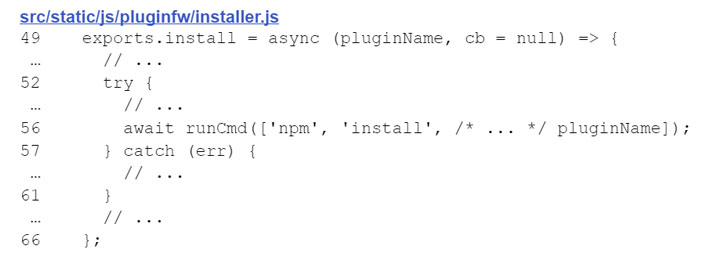
The consequence of thriving exploitation of CVE-2021-34816 is the execution of arbitrary code and technique instructions, therefore absolutely compromising the Etherpad instance and its data.
Concerningly, the two vulnerabilities can be chained alongside one another by an attacker first to choose more than an administrator account and then use individuals privileges to gain a shell and execute malicious code on the server.

“Fixed a persistent XSS vulnerability in the Chat component,” Etherpad maintainers mentioned in the launch notes for edition 1.8.14. “In scenario you can not update to 1.8.14 directly, we strongly advise to cherry-pick [commit] a796811.” It is worth pointing out that the argument injection vulnerability stays unpatched, though the scientists be aware that the flaw is “appreciably more durable to exploit on its personal.”
The investigate highlights “how essential information validation and sanitization is for staying away from this sort of flaws for the duration of improvement,” Gerste stated, introducing, “the smallest coding mistake can be the 1st stepping stone for an attacker to launch even more attacks in opposition to the application.”
Etherpad people are very encouraged to update their installations to model 1.8.14 to mitigate the risk involved with the flaw.
Identified this posting exciting? Abide by THN on Fb, Twitter and LinkedIn to browse more distinctive material we put up.
Some elements of this article are sourced from:
thehackernews.com


 Interpol calls for more action on ransomware pandemic
Interpol calls for more action on ransomware pandemic