Four security vulnerabilities have been uncovered in the Sage X3 business source scheduling (ERP) solution, two of which could be chained jointly as aspect of an attack sequence to allow adversaries to execute destructive instructions and just take command of susceptible methods.
These issues were being found by scientists from Quick7, who notified Sage Team of their results on Feb. 3, 2021. The seller has considering the fact that rolled out fixes in the latest releases for Sage X3 Model 9 (Syracuse 9.22.7.2), Sage X3 HR & Payroll Edition 9 (Syracuse 9.24.1.3), Sage X3 Model 11 (Syracuse 11.25.2.6), and Sage X3 Version 12 (Syracuse 12.10.2.8) that ended up delivered in March.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The listing of vulnerabilities is as follows –
- CVE-2020-7388 (CVSS rating: 10.) – Sage X3 Unauthenticated Remote Command Execution (RCE) as Process in AdxDSrv.exe ingredient
- CVE-2020-7389 (CVSS score” 5.5) – System “CHAINE” Variable Script Command Injection (No repair prepared)
- CVE-2020-7387 (CVSS score: 5.3) – Sage X3 Installation Pathname Disclosure
- CVE-2020-7390 (CVSS score: 4.6) – Stored XSS Vulnerability on ‘Edit’ Website page of User Profile
“When combining CVE-2020-7387 and CVE-2020-7388, an attacker can 1st find out the installation route of the influenced software package, then use that facts to move commands to the host technique to be run in the Program context,” the researchers mentioned. “This can permit an attacker to run arbitrary operating program instructions to build Administrator amount buyers, set up destructive computer software, and otherwise get finish manage of the technique for any function.”
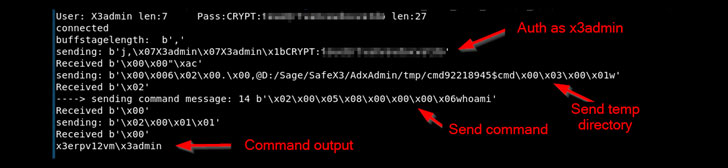
The most serious of the issues is CVE-2020-7388, which will take benefit of an administrative service which is accessible about the internet to craft malicious requests with the target of functioning arbitrary instructions on the server as the “NT AUTHORITY/Technique” person. The support in concern is applied for remote administration of the Sage ERP alternative as a result of the Sage X3 Console.

Independently, the ‘Edit’ website page involved with person profiles in the Sage X3 Syracuse web server part is vulnerable to a saved XSS attack (CVE-2020-7390), enabling the execution of arbitrary JavaScript code for the duration of ‘mouseOver’ events in the ‘First name’, ‘Last name’, and ‘Email’ fields.
“If thriving, even so, this vulnerability could make it possible for a frequent consumer of Sage X3 to execute privileged capabilities as a presently logged-in administrator or capture administrator session cookies for later impersonation as a at present-logged-in administrator,” the researchers claimed.
Productive exploitation of CVE-2020-7387, on the other hand, success in the publicity of Sage X3 set up paths to an unauthorized person, while CVE-2020-7389 issues a missing authentication in Syracuse growth environments that could be utilized to gain code execution by way of command injection.
“Usually speaking, Sage X3 installations should not be uncovered specifically to the internet, and should rather be designed available through a secure VPN link exactly where demanded,” the scientists noted in the disclosure. “Following this operational information successfully mitigates all four vulnerabilities, nevertheless prospects are still urged to update according to their normal patch cycle schedules.”
Uncovered this report exciting? Adhere to THN on Facebook, Twitter and LinkedIn to go through far more unique information we article.
Some parts of this article are sourced from:
thehackernews.com

 Regulator Probes Former Health Secretary’s Use of Private Email
Regulator Probes Former Health Secretary’s Use of Private Email