Cybersecurity agencies in Australia and the U.S. are warning of an actively exploited vulnerability impacting ForgeRock’s OpenAM entry administration option that could be leveraged to execute arbitrary code on an afflicted procedure remotely.
“The [Australian Cyber Security Centre] has observed actors exploiting this vulnerability to compromise numerous hosts and deploy more malware and equipment,” the group stated in an notify. ACSC failed to disclose the character of the attacks, how common they are, or the identities of the menace actors exploiting them.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
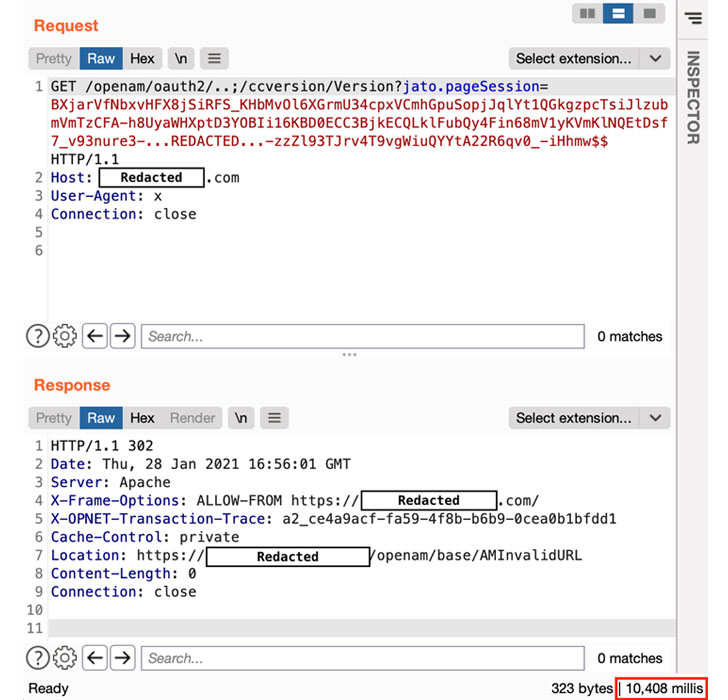
Tracked as CVE-2021-35464, the issue issues a pre-authentication remote code execution (RCE) vulnerability in ForgeRock Obtain Manager id and entry administration tool, and stems from an unsafe Java deserialization in the Jato framework made use of by the software program.
“An attacker exploiting the vulnerability will execute instructions in the context of the existing consumer, not as the root user (unless ForgeRock AM is working as the root consumer, which is not advisable),” the San Francisco-headquartered software program company famous in an advisory.

“An attacker can use the code execution to extract qualifications and certificates, or to attain a further foothold on the host by staging some sort of shell (this kind of as the popular implant Cobalt Strike),” it additional.
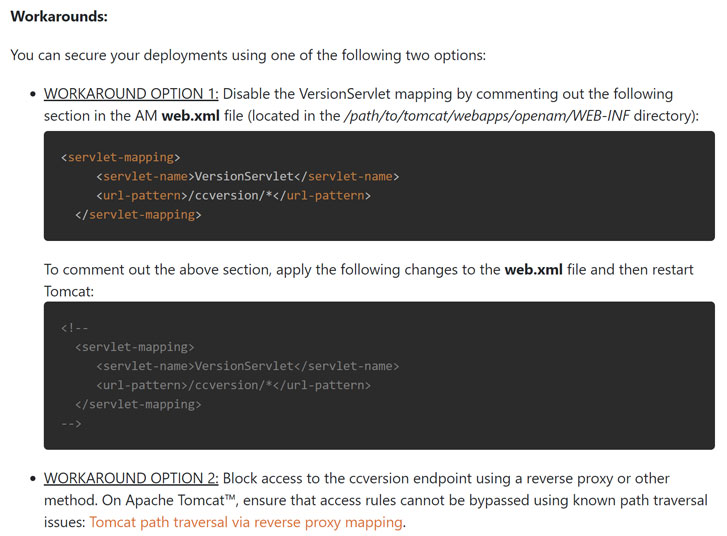
The vulnerability has an effect on variations 6…x and all variations of 6.5, up to and which include 6.5.3, and has been resolved in edition AM 7 released on June 29, 2021. ForgeRock buyers are recommended to move swiftly to deploy the patches to mitigate the risk linked with the flaw.
Identified this posting appealing? Observe THN on Facebook, Twitter and LinkedIn to study much more unique material we put up.
Some elements of this article are sourced from:
thehackernews.com


 A New Critical SolarWinds Zero-Day Vulnerability Under Active Attack
A New Critical SolarWinds Zero-Day Vulnerability Under Active Attack