Technological aspects have been disclosed regarding a number of security vulnerabilities impacting Moxa’s MXview web-primarily based network management process, some of which could be chained by an unauthenticated adversary to achieve distant code execution on unpatched servers.
The five security weaknesses “could enable a remote, unauthenticated attacker to execute code on the hosting equipment with the greatest privileges readily available: NT AUTHORITYSYSTEM,” Claroty security researcher Noam Moshe explained in a report published this 7 days.
Moxa MXview is designed for configuring, checking, and diagnosing networking units in industrial networks. The flaws, which have an effect on versions 3.x to 3.2.2 of the network administration software, ended up rectified in edition 3.2.4 or higher pursuing a coordinated disclosure approach in October 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Profitable exploitation of these vulnerabilities might permit an attacker to make or overwrite critical information to execute code, acquire access to the system, receive credentials, disable the software package, read through and modify in any other case inaccessible facts, enable distant connections to inside communication channels, or interact and use MQTT remotely,” the U.S. Cybersecurity and Infrastructure Security Agency (CISA) reported in an advisory.
MQTT refers to a messaging protocol that facilitates remote asynchronous interaction, enabling the transfer of messages to and from unique elements in an MXview atmosphere.
The checklist of flaws is as follows —
- CVE-2021-38452 (CVSS score: 7.5) – A route traversal vulnerability in the software, allowing the entry or overwrite of critical documents utilized to execute code
- CVE-2021-38454 (CVSS rating: 10.) – A misconfigured company that enables distant connections to MQTT, earning it probable to remotely interact and use the conversation channel
- CVE-2021-38456 (CVSS rating: 9.8) – Use of tough-coded passwords
- CVE-2021-38458 (CVSS score: 9.8) – An issue with poor neutralization of special elements that could guide to remote execution of unauthorized instructions
- CVE-2021-38460 (CVSS rating: 7.5) – A case of password leakage that may perhaps permit an attacker to get hold of credentials
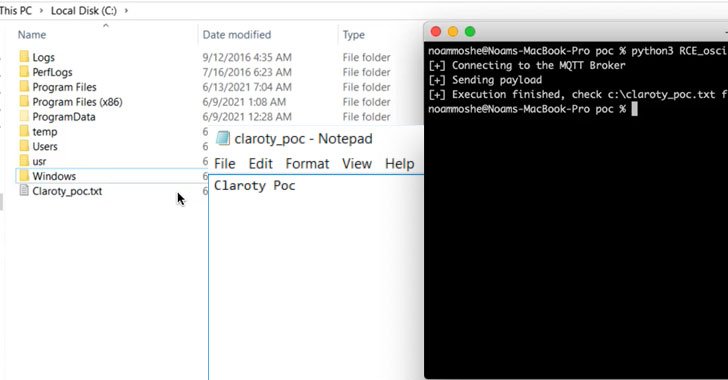
Three of the aforementioned flaws — CVE-2021-38452, CVE-2021-38454, and CVE-2021-38458, could be strung with each other to reach pre-authenticated distant code execution on susceptible MXView instances with Program privileges.
In a hypothetical attack scenario devised by Claroty, CVE-2021-38452 could be abused to get keep of the plain-text MQTT password by reading the configuration file gateway-upper.ini, adopted by leveraging CVE-2021-38454 to inject rogue MQTT messages, triggering code execution through command injection on the server.
“An attacker injects malicious messages to the MQTT broker instantly, bypassing all input validation carried out by the server, and achieves arbitrary remote code execution via the OS command injection vulnerability,” Moshe explained.
Located this post interesting? Comply with THN on Fb, Twitter and LinkedIn to study far more distinctive material we article.
Some areas of this report are sourced from:
thehackernews.com


 Critical Magento 0-Day Vulnerability Under Active Exploitation — Patch Released
Critical Magento 0-Day Vulnerability Under Active Exploitation — Patch Released