The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday issued an advisory concerning a critical application source-chain flaw impacting ThroughTek’s software program growth kit (SDK) that could be abused by an adversary to get improper entry to audio and video streams.
“Successful exploitation of this vulnerability could permit unauthorized access to sensitive facts, these as digital camera audio/video clip feeds,” CISA reported in the inform.
ThroughTek’s point-to-stage (P2P) SDK is broadly used by IoT equipment with online video surveillance or audio/video clip transmission ability these types of as IP cameras, child and pet checking cameras, intelligent household appliances, and sensors to deliver remote access to the media articles over the internet.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tracked as CVE-2021-32934 (CVSS rating: 9.1), the shortcoming affects ThroughTek P2P goods, variations 3.1.5 and right before as very well as SDK versions with nossl tag, and stems from a lack of adequate safety when transferring info in between the nearby unit and ThroughTek’s servers.
The flaw was reported by Nozomi Networks in March 2021, which famous that the use of vulnerable security cameras could go away critical infrastructure operators at risk by exposing delicate business, generation, and personnel details.
“The [P2P] protocol made use of by ThroughTek lacks a protected essential exchange [and] depends as an alternative on an obfuscation plan centered on a set key,” the San Francisco-headquartered IoT security company claimed. “Since this site visitors traverses the internet, an attacker that is able to accessibility it can reconstruct the audio/movie stream.”
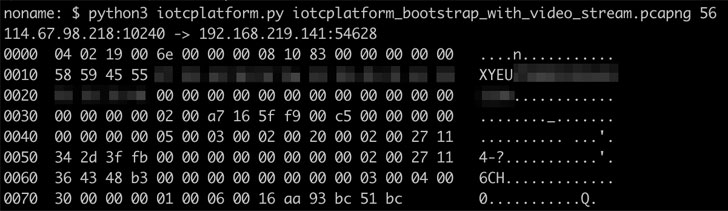
To show the vulnerability, the scientists developed a proof-of-idea (PoC) exploit that deobfuscates on-the-fly packets from the network targeted visitors.

ThroughTek recommends original machines suppliers (OEMs) utilizing SDK 3.1.10 and previously mentioned to permit AuthKey and DTLS, and those people relying on an SDK variation prior to 3.1.10 to upgrade the library to variation 3.3.1. or v3.4.2. and allow AuthKey/DTLS.
Given that the flaw influences a application element which is section of the provide chain for a lot of OEMs of shopper-grade security cameras and IoT equipment, the fallout from these exploitation could proficiently breach the security of the units, enabling the attacker to accessibility and look at confidential audio or online video streams.
“Simply because ThroughTek’s P2P library has been integrated by many vendors into numerous various products about the a long time, it can be pretty much impossible for a third-party to keep track of the affected goods,” the scientists said.
Identified this article attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to examine far more unique content material we post.
Some pieces of this write-up are sourced from:
thehackernews.com


 Deloitte acquires online antifraud firm Terbium Labs
Deloitte acquires online antifraud firm Terbium Labs