Scientists have unearthed a new distant entry trojan (RAT) for Linux that employs a never-ahead of-found stealth procedure that requires masking its destructive steps by scheduling them for execution on February 31st, a non-existent calendar working day.
Dubbed CronRAT, the sneaky malware “permits server-aspect Magecart info theft which bypasses browser-dependent security methods,” Sansec Threat Investigation claimed. The Dutch cybersecurity agency explained it observed samples of the RAT on quite a few on the internet merchants, together with an unnamed country’s greatest outlet.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CronRAT’s standout element is its skill to leverage the cron job-scheduler utility for Unix to hide destructive payloads employing undertaking names programmed to execute on February 31st. Not only does this let the malware to evade detection from security software program, but it also permits it to launch an array of attack instructions that could set Linux eCommerce servers at risk.
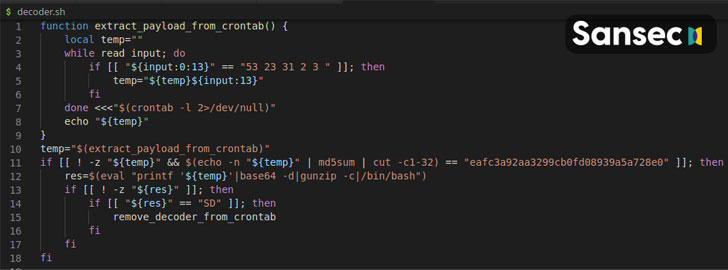
“The CronRAT adds a amount of jobs to crontab with a curious day specification: 52 23 31 2 3,” the scientists defined. “These traces are syntactically valid, but would deliver a operate time error when executed. Nonetheless, this will never ever happen as they are scheduled to run on February 31st.”
The RAT — a “refined Bash application” — also utilizes several levels of obfuscation to make evaluation tricky, these types of as putting code powering encoding and compression limitations, and applying a custom binary protocol with random checksums to slip past firewalls and packet inspectors, just before creating communications with a remote manage server to await more guidelines.

Armed with this backdoor access, the attackers involved with CronRAT can run any code on the compromised method, the researchers mentioned.
“Electronic skimming is relocating from the browser to the server and this is however one more illustration,” Sansec’s Director of Menace Exploration, Willem de Groot, explained. “Most on the web suppliers have only carried out browser-based mostly defenses, and criminals capitalize on the unprotected back again-end. Security gurus must seriously consider the entire attack area.”
Observed this article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to browse much more exclusive content we publish.
Some sections of this short article are sourced from:
thehackernews.com


 Gatekeeping the internet: Is UK net neutrality under threat?
Gatekeeping the internet: Is UK net neutrality under threat?