A new investigate has uncovered multiple significant reverse RDP vulnerabilities in Apache Guacamole, a well-known distant desktop application utilised by process administrators to accessibility and control Windows and Linux machines remotely.
The documented flaws could likely enable negative actors achieve comprehensive control over the Guacamole server, intercept, and command all other connected sessions.
In accordance to a report released by Examine Issue Research and shared with The Hacker Information, the flaws grant “an attacker, who has previously successfully compromised a computer system inside the business, to start an assault on the Guacamole gateway when an unsuspecting worker attempts to join to an contaminated machine.”
After the cybersecurity business responsibly disclosed its findings to Apache, the maintainers of Guacamole, on March 31, the organization released a patched model in June 2020. Apache Guacamole is a well-liked open up-supply clientless remote desktop gateways answer. When installed on a firm’s server, it enables people to remotely link to their desktops simply just applying a world-wide-web browser post an authentication system.
Notably, Apache Guacamole distant desktop application has amassed around 10 million downloads to date on Docker Hub.
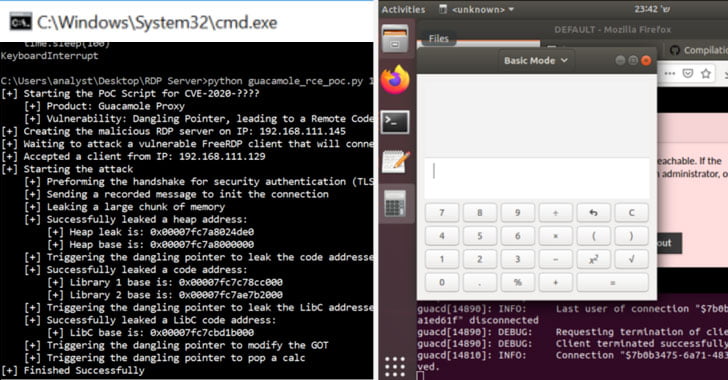
Memory Corruption Flaw to RCE
The attacks stem from 1 of the two probable strategies the gateway can be taken about: either by a compromised equipment inside the company community that leverages an incoming benign connection to assault the Apache gateway or a rogue personnel who works by using a laptop within the network to hijack the gateway.
Test Position crew claimed it recognized the flaws as part of Guacamole’s the latest stability audit, which also included assist for FreeRDP 2.. toward the finish of January 2020.
It really is value pointing out that FreeRDP, an open-supply RDP client, experienced its own fair share of remote code execution flaws, which have been disclosed early last yr adhering to the release of 2..-rc4.
“Being aware of that vulnerabilities in FreeRDP were being only patched on edition 2..-rc4, this indicates that all variations that have been released ahead of January 2020 are making use of vulnerable versions of FreeRDP,” Examine Position researcher Eyal Itkin mentioned.
Here is a quick summary of all flaws discovered:

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
- Facts disclosure vulnerabilities (CVE-2020-9497) — Two independent flaws have been determined in the developers’ custom implementation of an RDP channel used to manage audio packets from the server (“rdpsnd”). The initial of the two flaws permits an attacker to craft a malicious rdpsnd concept that could guide to an out-of-bounds examine identical to Heartbleed. A 2nd bug in the identical channel is a data leak that transmits the out-of-bounds information to a linked client.
The third details disclosure bug is a variant of the aforementioned flaw that resides in a unique channel referred to as “guacai,” dependable for audio input and is disabled by default.
- Out-of-bounds reads in FreeRDP — Looking to discover a memory corruption vulnerability that could be leveraged to exploit the higher than knowledge leaks, Examine Stage reported they uncovered two additional scenarios of out-of-bounds reads that just take gain of a layout flaw in FreeRDP.
- Memory Corruption flaw in Guacamole (CVE-2020-9498) — This flaw, present in an abstraction layer (“guac_popular_svc.c”) laid more than rdpsnd and rdpdr (Device Redirection) channels, arises from a memory security violation, ensuing in a dangling pointer that allows an attacker to attain code execution by combining the two flaws.
Use-immediately after-free vulnerabilities are memory corruption bugs that generally manifest when an application tries to use memory house that is no for a longer period assigned to it. This usually brings about a application to crash but can also in some cases lead to other unintended effects, these as code execution that can be exploited by malicious actors.
By utilizing vulnerabilities CVE-2020-9497 and CVE-2020-9498, “a malicious corporate computer (our RDP ‘server’) can take regulate of the guacd approach when a remote user requests to hook up to his (contaminated) pc,” Itkin explained.
A Situation of Privilege Escalation
Additional concerning, Examine Issue found it was probable to seize manage of all of the connections in the gateway from only a solitary guacd approach, which runs on the Guacamole server to take care of distant connections to the corporate community.
In addition to managing the gateway, this privilege escalation permits an attacker to eavesdrop on all incoming classes, history the credentials made use of, and even start new sessions to handle the relaxation of the organization’s desktops.
“Whilst the changeover to distant perform from dwelling is a necessity in these hard periods of the COVID-19 pandemic, we can not neglect the stability implications of these kinds of remote connections,” Itkin concluded. “When most of the organization is operating remotely, this foothold is equivalent to attaining total regulate in excess of the overall organizational network.”
“We strongly suggest that anyone will make positive that all servers are up-to-date, and that whatsoever technological know-how applied for operating from dwelling is entirely patched to block these types of attack makes an attempt.”
Identified this article interesting? Stick to THN on Facebook, Twitter and LinkedIn to browse far more special written content we article.

 Alina Point-of-Sale Malware Spotted in Ongoing Campaign
Alina Point-of-Sale Malware Spotted in Ongoing Campaign