A new malware marketing campaign has been identified concentrating on cryptocurrency, non-fungible token (NFT), and DeFi aficionados by way of Discord channels to deploy a crypter named “Babadeda” that’s able of bypassing antivirus solutions and stage a range of attacks.
“[T]his malware installer has been used in a selection of recent strategies to provide information and facts stealers, RATs, and even LockBit ransomware,” Morphisec scientists stated in a report released this week. The malware distribution attacks are reported to have commenced in Could 2021.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
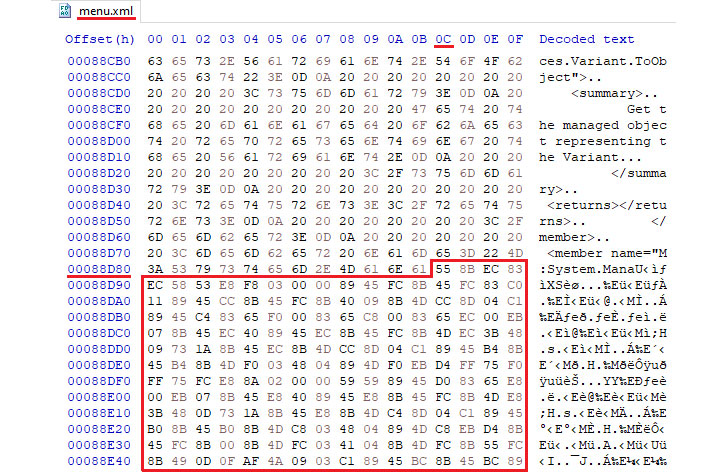
Crypters are a style of software package employed by cybercriminals that can encrypt, obfuscate, and manipulate malicious code so as to show up seemingly innocuous and make it harder to detect by security programs — a holy grail for malware authors.
The infiltrations observed by Morphisec included the menace actor sending decoy messages to potential end users on Discord channels similar to blockchain-primarily based video games such as Mines of Dalarnia, urging them to down load an software. Should really a target click a URL embedded in the message, the specific is directed to a phishing area created to resemble the game’s legitimate internet site and includes a backlink to a malicious installer that contains the Babadeda crypter.
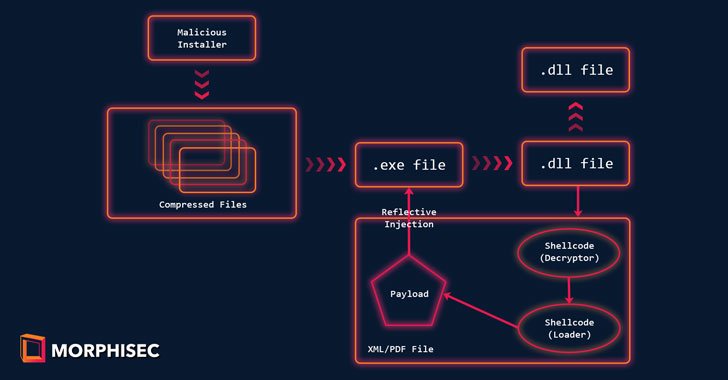
Upon execution, the installer triggers an an infection sequence that decodes and masses the encrypted payload, in this circumstance BitRAT and Remcos, to harvest precious details.

Morphisec attributed the attacks to a threat actor from a Russian-talking region, owing to the Russian language text exhibited on one of the decoy internet sites. As numerous as 84 destructive domains, made amongst July 24, 2021, and November 17, 2021, have been recognized to day.
“Concentrating on cryptocurrency consumers by way of trustworthy attack vectors offers its distributors a fast-developing choice of opportunity victims,” the researchers stated. “When on a victim’s machine, masquerading as a recognised application with a advanced obfuscation also means that any one relying on signature-dependent malware efficiently has no way of knowing Babadeda is on their device — or of stopping it from executing.”
Discovered this write-up intriguing? Adhere to THN on Fb, Twitter and LinkedIn to read through much more exceptional content material we publish.
Some areas of this posting are sourced from:
thehackernews.com

 Flaw in Android phones could let attackers eavesdrop on calls
Flaw in Android phones could let attackers eavesdrop on calls