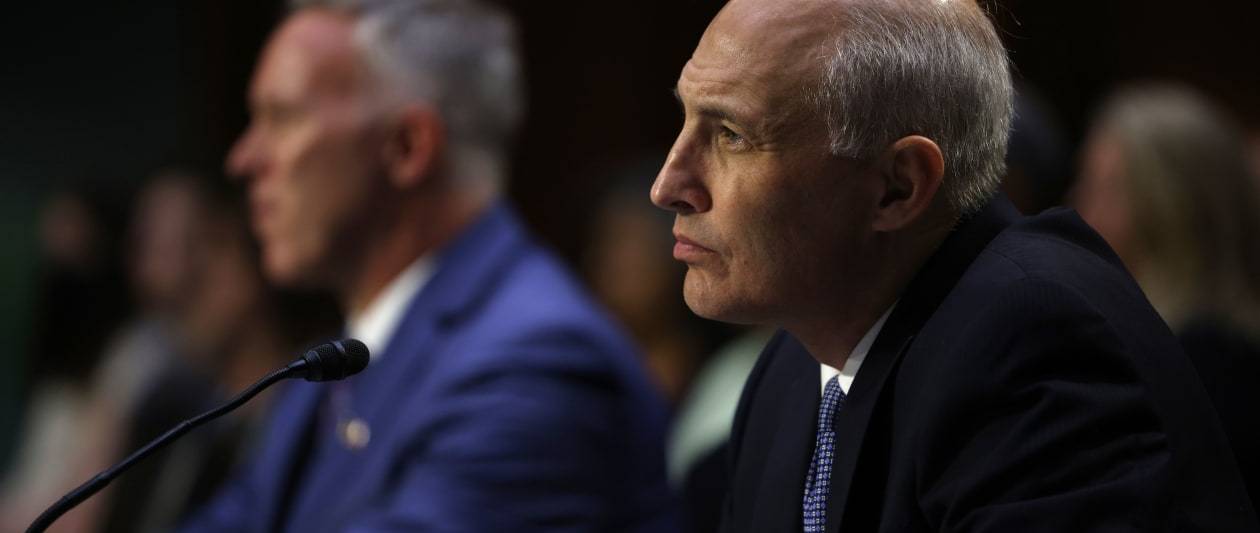
Getty Photographs
The US Justice Office has confirmed it is currently investigating a cyber security breach in the federal courtroom process dating again to early 2020.
The process “faced an very major and subtle cyber security breach” that imposed “lingering impacts on the office and other [federal] agencies”, the division said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
It is the very first public disclosure of the attack that is now far more than two many years old and different from the massively disruptive SolarWinds Orion attack that was performed by Russia-connected point out-sponsored hackers.
The comments have been manufactured at a listening to on the oversight of the Justice Office National Security Division (NSD), by House Judiciary Committee Chair Jerrold Nadler on Thursday.
Nadler explained the Committee “recently learned” about the attack in dilemma, a timeline the Democrat-party agent for New York in Congress afterwards clarified to be March 2022.
Responding to questioning from Nadler at the listening to, Assistant Attorney Standard for Nationwide Security Matthew Olsen explained the NSD will provide updates to the Committee as the investigation proceeds.
Olsen later on said that the effects of the cyber security breach on the federal court docket program did not influence any investigations of other scenarios that he could think of, despite an anonymous aide speaking to Politico, stating the “sweeping impact” it had on the office was “staggering”.
The breach mentioned this 7 days might refer to a disclosure on 6 January 2021 pertaining to a security incident impacting the judiciary’s circumstance submitting technique, which “greatly” risked compromising “highly sensitive non-public documents”.
Next the incident, enhanced security strategies ended up released to the method. The compromised electronic submitting process was not to be utilized and alternatively, extremely delicate files had been only submitted in paper sort or by means of a “secure electronic machine, this sort of as as a thumb push, and stored in a protected standalone computer system process”.
It truly is presently unclear who is liable for the early 2020 cyber attack and the entire aspects of the affect on the section and other organizations are also not known at this time.
Even with this, Olsen mentioned his workforce is generally tasked with investigating incidents performed by international entities, ordinarily involving nations these types of as Russia, China, Iran, and North Korea.
The US government has indicated that it has taken cyber security even additional very seriously in the latest times, especially at a federal level, subsequent a quantity of substantial-profile incidents in latest yrs.
The Biden administration categorised ransomware attacks in the exact group as terrorist incidents following the attack on Colonial Pipeline final yr.
All federal businesses have also been explained to that they ought to patch their units from a prolonged listing of the most-exploited security vulnerabilities to minimise the probable impression of an attack on governing administration procedures.
Some sections of this article are sourced from:
www.itpro.co.uk

 RaaS Groups Forced to Change Tack as Payments Decline
RaaS Groups Forced to Change Tack as Payments Decline