A Nigerian risk actor has been observed attempting to recruit workforce by presenting them to pay back $1 million in bitcoins to deploy Black Kingdom ransomware on companies’ networks as aspect of an insider danger plan.
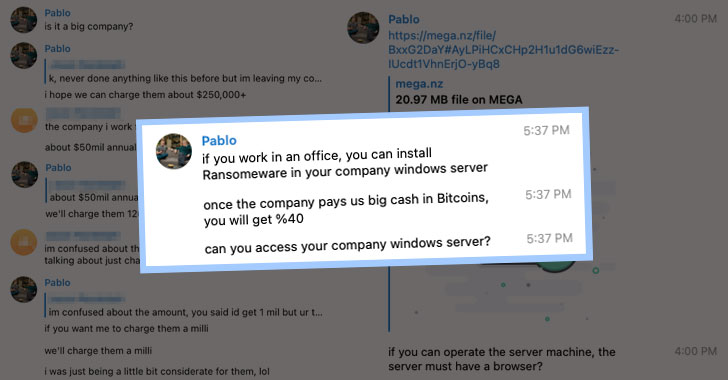
“The sender tells the worker that if they’re ready to deploy ransomware on a corporation laptop or computer or Windows server, then they would be compensated $1 million in bitcoin, or 40% of the presumed $2.5 million ransom,” Irregular Security mentioned in a report revealed Thursday. “The worker is instructed they can launch the ransomware bodily or remotely. The sender presented two strategies to call them if the personnel is interested—an Outlook email account and a Telegram username.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
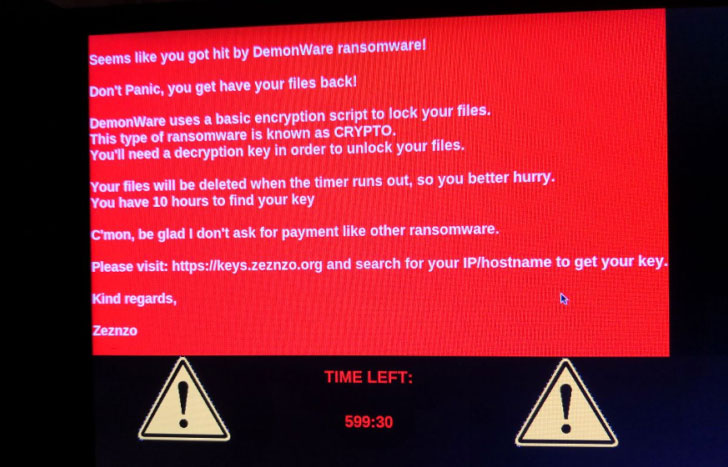
Black Kingdom, also recognised as DemonWare and DEMON, attracted awareness before this March when menace actors were being observed exploiting ProxyLogon flaws impacting Microsoft Trade Servers to infect unpatched methods with the ransomware pressure.
Irregular Security, which detected and blocked the phishing e-mail on August 12, responded to the solicitation try by producing a fictitious persona and achieved out to the actor on Telegram messenger, only to have the specific inadvertently spill the attack’s modus operandi, which integrated two links for an executable ransomware payload that the “staff” could obtain from WeTransfer or Mega.nz.
“The actor also instructed us to dispose of the .EXE file and delete it from the recycle bin. Based on the actor’s responses, it looks obvious that he 1) expects an worker to have physical accessibility to a server, and 2) he’s not extremely common with digital forensics or incident reaction investigations,” explained Crane Hassold, director of threat intelligence at Irregular Security.
Moreover getting a adaptable method to their ransom calls for, the plan is believed to have been concocted by the main govt of a Lagos-based mostly social networking startup named Sociogram, with the intention of utilizing the siphoned funds to “construct my very own company.” In just one of the conversations that took position around the course of five days, the personal even took to calling himself “the future Mark Zuckerberg.”
Also of certain observe is the process of employing LinkedIn to obtain corporate email addresses of senior-level executives, when once again highlighting how company email compromise (BEC) attacks originating from Nigeria continue on to evolve and expose companies to complex attacks like ransomware.

“There is generally been a blurry line among cyberattacks and social engineering, and this is an illustration of how the two are intertwined. As people come to be far better at recognizing and avoiding phishing, it really should be no shock to see attackers undertake new strategies to attain their aims,” Tim Erlin, vice president of solution management and technique at Tripwire, said.
“The thought of a disgruntled insider as a cybersecurity risk is just not new. As extensive as companies demand workforce, there will constantly be some insider risk. The assure of getting a share of the ransom may possibly seem to be attractive, but there is pretty much zero warranty that this kind of complicity will in fact be rewarded, and it can be highly possible that somebody getting this attacker up on their offer would get caught,” Erlin extra.
Uncovered this short article interesting? Observe THN on Facebook, Twitter and LinkedIn to browse much more unique articles we put up.
Some components of this post are sourced from:
thehackernews.com

 Anti-Money Laundering Fines Fall by 50% in 1H 2021
Anti-Money Laundering Fines Fall by 50% in 1H 2021