Threat actors are capitalizing on the escalating acceptance of proxyware platforms like Honeygain and Nanowire to monetize their very own malware campaigns, after all over again illustrating how attackers are speedy to repurpose and weaponize legitimate platforms to their advantage.
“Malware is presently leveraging these platforms to monetize the internet bandwidth of victims, identical to how destructive cryptocurrency mining attempts to monetize the CPU cycles of infected programs,” scientists from Cisco Talos stated in a Tuesday evaluation. “In several conditions, these applications are featured in multi-stage, multi-payload malware attacks that give adversaries with several monetization procedures.”
Proxyware, also called internet-sharing applications, are reputable products and services that permit users to carve out a share of their internet bandwidth for other devices, generally for a cost, by means of a customer application offered by the company, enabling other consumers to access the internet working with the internet connections available by nodes on the network. For consumers, these types of companies are “advertised as a usually means to circumvent geolocation checks on streaming or gaming platforms while making some earnings for the consumer offering up their bandwidth,” the researchers stated.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
But the illicit use of proxyware also introduces a multitude of hazards in that they could permit danger actors to obfuscate the source of their attacks, thereby not only providing them the ability to execute destructive steps by producing it look as if they are originating from authentic residential or corporate networks, but also render ineffective standard network defenses that rely on IP-based mostly blocklists.
“The very same mechanisms at this time utilised to watch and monitor Tor exit nodes, “nameless” proxies, and other prevalent visitors obfuscation procedures do not at present exist for tracking nodes within just these proxyware networks,” the researchers mentioned.
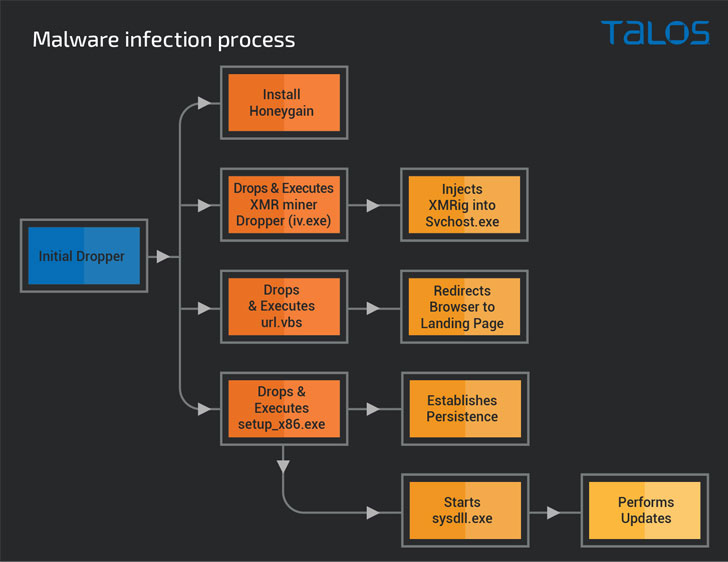
That is not all. Scientists determined quite a few strategies adopted by poor actors, together with trojanized proxyware installers that let for stealthy distribution of data stealers and remote accessibility trojans (RATs) without having the victims’ knowledge. In just one instance observed by Cisco Talos, attackers were being discovered working with the proxyware programs to monetize victims’ network bandwidth to create income as properly as exploit the compromised machine’s CPU means for mining cryptocurrency.
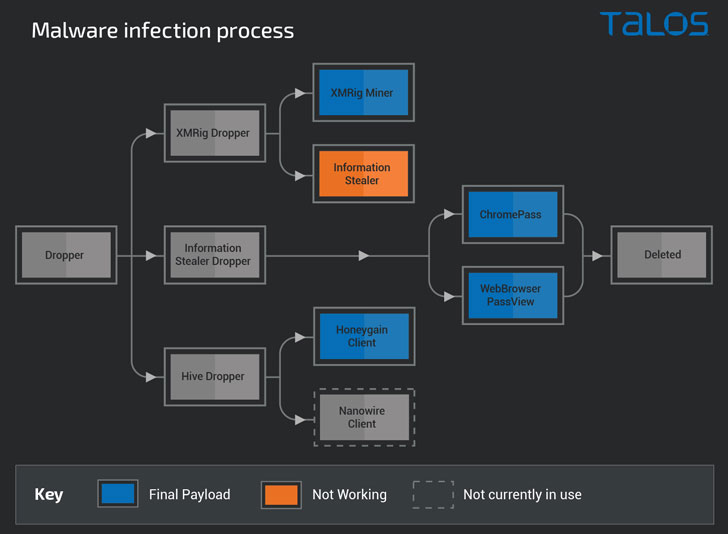
Yet another situation involved a multi-stage malware marketing campaign that culminated in the deployment of an details-stealer, a cryptocurrency mining payload, as effectively as proxyware software program, underscoring the “varied strategies accessible to adversaries,” who can now go past cryptojacking to also plunder important info and monetize prosperous infections in other strategies.
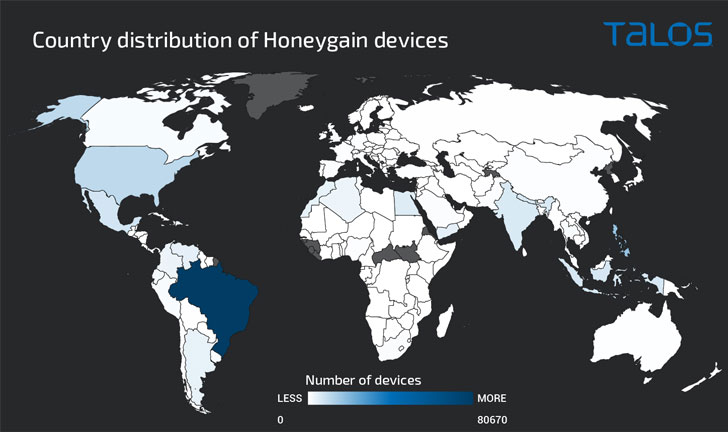
Even much more concerningly, researchers detected malware that was utilized to silently install Honeygain on contaminated techniques, and register the consumer with the adversary’s Honeygain account to gain off the victim’s internet bandwidth. This also means that an attacker can indication up for multiple Honeygain accounts to scale their procedure centered on the number of infected devices below their regulate.
“For corporations, these platforms pose two vital issues: The abuse of their assets, sooner or later staying blocklisted owing to activities they never even command and it will increase organizations’ attack surface, potentially developing an initial attack vector straight on the endpoint,” the researchers concluded. “Thanks to the numerous pitfalls related with these platforms, it is advised that corporations think about prohibiting the use of these applications on company property.”
Uncovered this posting intriguing? Adhere to THN on Fb, Twitter and LinkedIn to examine more exceptional content material we submit.
Some sections of this article are sourced from:
thehackernews.com

 Linphone SIP Stack Bug Could Let Attackers Remotely Crash Client Devices
Linphone SIP Stack Bug Could Let Attackers Remotely Crash Client Devices