In a signal that destructive actors keep on to locate means to perform all over Google Participate in Store security protections, researchers have spotted a formerly undocumented Android dropper trojan that is at this time in advancement.
“This new malware tries to abuse equipment using a novel system, not observed prior to in Android malware, to distribute the exceptionally risky Xenomorph banking trojan, letting criminals to complete On-System Fraud on victim’s units,” ThreatFabric’s Han Sahin mentioned in a statement shared with The Hacker News.
Dubbed BugDrop by the Dutch security business, the dropper application is explicitly made to defeat new attributes introduced in the future variation of Android that purpose to make it hard for malware to request Accessibility Products and services privileges from victims.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

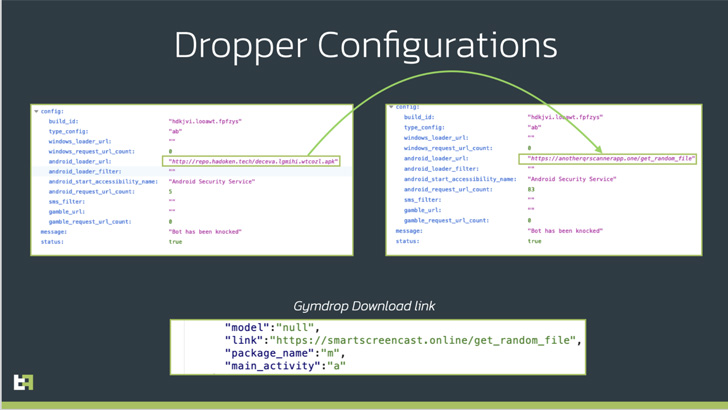
ThreatFabric attributed the dropper to a cybercriminal group regarded as “Hadoken Security,” which is also guiding the generation and distribution of the Xenomorph and Gymdrop Android malware people.
Banking trojans are typically deployed on Android devices via innocuous dropper applications that pose as productiveness and utility applications, which, once mounted, trick customers into granting invasive permissions.
Notably, the Accessibility API, which allows applications read the contents of the display and complete actions on behalf of the consumer, has occur less than weighty abuse, enabling malware operators to capture sensitive details these types of as qualifications and economic info.
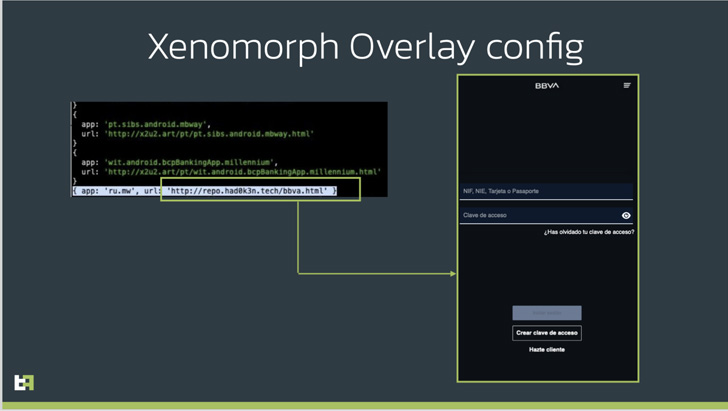
This is reached by implies of what’s named overlay attacks wherein the trojan injects a phony lookalike login sort retrieved from a remote server when a desired application these types of as a cryptocurrency wallet is opened by the target.
Given that most of these destructive apps are sideloaded – some thing which is only possible if the consumer has authorized set up from unknown resources – Google, with Android 13, has taken the step of blocking accessibility API entry to apps set up from outdoors of an application retail outlet.
But that hasn’t stopped adversaries from making an attempt to circumvent this restricted security placing. Enter BugDrop, which masquerades as a QR code reader app and is remaining examined by its authors to deploy malicious payloads by means of a session-primarily based set up course of action.

“What is very likely taking place is that actors are using an presently created malware, able of setting up new APKs on an infected machine, to examination a session-centered installation technique, which would then afterwards be included in a far more elaborate and refined dropper,” the scientists stated.
The alterations, should it develop into a fact, could make the banking trojans a extra hazardous threat able of bypassing security defenses even ahead of they are in put.
“With the completion and resolution of all the issues at the moment present in BugDrop, criminals will have an additional effective weapon in the war towards security teams and banking institutions, defeating answers that are presently remaining adopted by Google, which are plainly not ample to prevent criminals,” the business observed.
People are suggested to stay clear of slipping victim to malware hidden in official application shops by only downloading purposes from recognized builders and publishers, scrutinizing application assessments, and examining their privacy guidelines.
Identified this article attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to browse much more exceptional written content we publish.
Some parts of this report are sourced from:
thehackernews.com


 Can’t choose between public and private cloud? You don’t have to with IaaS
Can’t choose between public and private cloud? You don’t have to with IaaS