Menace actors are significantly adopting Excel 4. paperwork as an first phase vector to distribute malware this sort of as ZLoader and Quakbot, in accordance to new investigation.
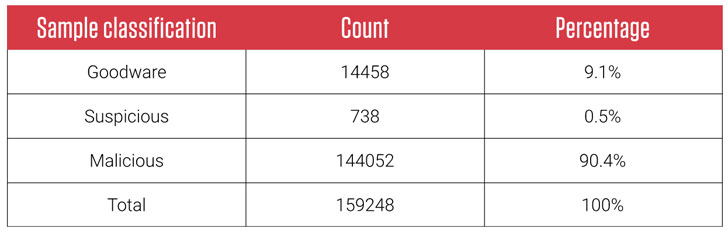
The conclusions arrive from an examination of 160,000 Excel 4. documents concerning November 2020 and March 2021, out of which a lot more than 90% were being categorised as destructive or suspicious.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The most significant risk for the targeted providers and people today is the actuality that security remedies nonetheless have a ton of challenges with detecting malicious Excel 4. documents, earning most of these slip by standard signature centered detections and analyst penned YARA principles,” researchers from ReversingLabs claimed in a report posted right now.
Excel 4. macros (XLM), the precursor to Visual Fundamental for Purposes (VBA), is a legacy feature integrated in Microsoft Excel for backward compatibility good reasons. Microsoft warns in its aid doc that enabling all macros can cause “likely perilous code” to run.
The ever-evolving Quakbot (aka QBOT), because its discovery in 2007, has remained a notorious banking trojan able of thieving banking qualifications and other economical details, when also attaining worm-like propagation options. Usually spread through weaponized Office environment files, variants of QakBot have been in a position to produce other malware payloads, log consumer keystrokes, and even produce a backdoor to compromised devices.

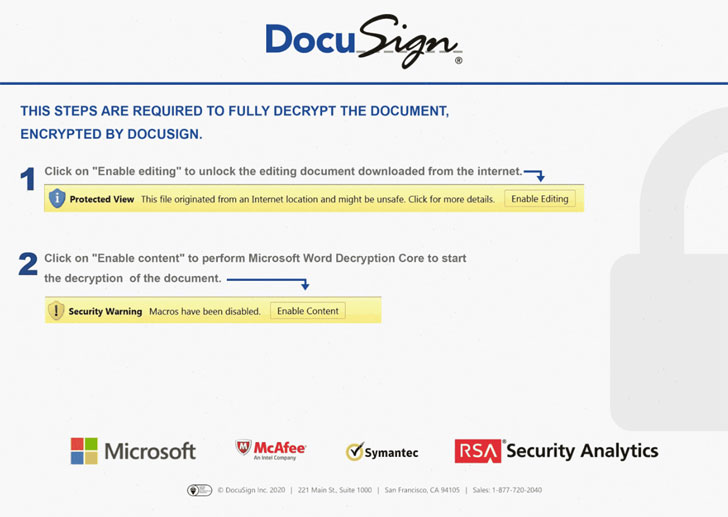
In a doc analyzed by ReversingLabs, the malware not only tricked end users into enabling macros with convincing lures, but also came with embedded information made up of XLM macros that obtain and execute a malicious 2nd-phase payload retrieved from a distant server. A further sample involved a Foundation64-encoded payload in a single of the sheets, which then attempted to download more malware from a sketchy URL.
“Even though backward compatibility is incredibly significant, some items should have a existence expectancy and, from a security viewpoint, it would likely be finest if they ended up deprecated at some level in time,” the researchers famous. “Price of keeping 30 year old macros ought to be weighed from the security risks making use of this sort of out-of-date technology provides.”
Found this posting attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to browse a lot more exclusive content material we put up.
Some pieces of this posting are sourced from:
thehackernews.com

 F5 BIG-IP Found Vulnerable to Kerberos KDC Spoofing Vulnerability
F5 BIG-IP Found Vulnerable to Kerberos KDC Spoofing Vulnerability