A threat actor, formerly regarded for striking organizations in the power and telecommunications sectors throughout the Center East as early as April 2018, has developed its malware arsenal to strike two entities in Tunisia.
Security scientists at Kaspersky, who offered their results at the VirusBulletin VB2021 conference previously this thirty day period, attributed the attacks to a team tracked as Lyceum (aka Hexane), which was first publicly documented in 2019 by Secureworks.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The victims we noticed had been all higher-profile Tunisian companies, these kinds of as telecommunications or aviation firms,” researchers Aseel Kayal, Mark Lechtik, and Paul Rascagneres detailed. “Centered on the focused industries, we think that the attackers could have been intrigued in compromising such entities to observe the movements and communications of individuals of fascination to them.”
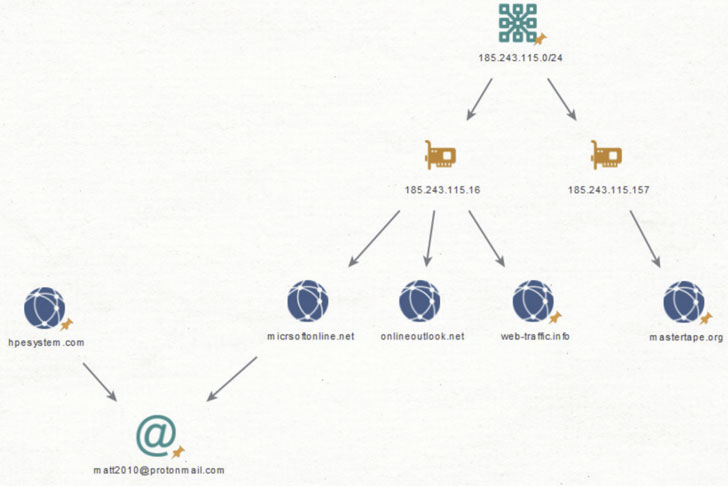
Examination of the threat actor’s toolset has shown that the attacks have shifted from leveraging a mixture of PowerShell scripts and a .NET-dependent distant administration device referred termed “DanBot” to two new malware variants penned in C++ referred to as “James” and “Kevin” owing to the recurring use of the names in the PDB paths of the fundamental samples.
Although the “James” sample is intensely primarily based on the DanBot, “Kevin” will come with main improvements in architecture and communication protocol, with the group predominantly relying on the latter as of December 2020, indicating an try to revamp its attack infrastructure in response to general public disclosure.
That mentioned, equally the artifacts guidance conversation with a distant command-and-server server by means of custom made-developed protocols tunneled above DNS or HTTP, mirroring the same system as that of DanBot. In addition, the attackers are also believed to have deployed a personalized keylogger as perfectly as a PowerShell script in compromised environments to report keystrokes and plunder credentials stored in web browsers.

The Russian cybersecurity seller mentioned that the attack approaches utilized in the marketing campaign versus Tunisian companies resembled tactics beforehand attributed to hacking operations connected with the DNSpionage team, which, in flip, has exhibited tradecraft overlaps to an Iranian risk actor dubbed OilRig (aka APT34), though contacting out the “significant similarities” involving lure paperwork sent by Lyceum in 2018-2019 and those people utilised by DNSpionage.
“With significant revelations on the action of DNSpionage in 2018, as perfectly as further info points that lose mild on an apparent marriage with APT34, […] the latter may possibly have modified some of its modus operandi and organizational construction, manifesting into new operational entities, applications and strategies,” the researchers claimed. “One these types of entity is the Lyceum group, which after further exposure by Secureworks in 2019, experienced to retool nonetheless one more time.”
Identified this write-up appealing? Abide by THN on Facebook, Twitter and LinkedIn to examine additional distinctive information we write-up.
Some parts of this short article are sourced from:
thehackernews.com

 iPhone Hackers Win $300K
iPhone Hackers Win $300K