We have all heard of the “cybersecurity capabilities hole” — firms’ inability to employ and retain high-level cybersecurity expertise.
I see this hole manifesting in two means. 1st, firms that want to use cybersecurity expertise just are unable to find candidates with adequate abilities. Next, businesses that are unable to pay for specialized cybersecurity expertise and as a result lack the needed expertise to sufficiently defend their corporations from the rising and increasingly sophisticated cyber threats.
Equally of these are actual challenges, and both equally can lead to devastating consequences. It really is also reasonable to say that most cybersecurity teams these days are overworked and understaffed.
Just one of the most important explanations we want this kind of superior-amount cybersecurity expertise lies in the shortcomings of cybersecurity systems. Thanks to the transforming and increasingly subtle stream of attack tactics, the breadth and depth of cybersecurity defensive systems utilized to fight these threats and guard organizations in opposition to breaches have exploded. Now, there appears to be a specialized instrument to cover each individual element of the attack floor and response system.
Sad to say, all but the most significant corporations with the deepest pockets can find the money for to acquire and then sufficiently integrate and maintain the expansive established of systems required to secure present day-day organizations from breaches. Most smaller companies suffer from a lack of technologies to defend their companies.
We are in dire need to have of techniques that simplify and consolidate the cybersecurity toolset so that firms can find the money for the coverage needed and to make effective breach safety obtainable to all those other than world-course experts.
Enter Cynet
Just one enterprise that seems to get the need for simplification, without having sacrificing the effectiveness, is Cynet. Cynet was shaped precisely to consolidate a number of threat avoidance and detection controls into a one giving for two primary factors. To start with, holding all the controls on a solitary platform allows for far far better benefits than integrating and running technologies from a number of suppliers.
2nd, it substantially simplifies the technology stack (not to mention affordability improvements). Then, Cynet goes further than these added benefits by automating numerous of the prevalent workflows necessary to answer to cyber threats that would otherwise require superior-level expertise, time, and exertion.
Products Evaluation: Cynet 360, 2020 Slide System Update
The Cynet 360 platform is designed on a few pillars Extended Detection and Response (XDR), Reaction Automation, and Managed Detection and Response (MDR). These a few components with each other supply what Cynet calls Autonomous Breach Security – in essence breach security on car-pilot. Let’s glance at just about every of these elements.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
XDR
When XDR is viewed as a new technology – it can be some thing Cynet has been carrying out considering that its inception. XDR technology effectively combines alerts from multiple handle points as section of a solitary platform to provide much better results than when deploying multiple siloed controls and then hoping to determine out the stream of alerts and data from just about every. Many analyst firms are touting XDR as “the following significant issue in cybersecurity.”
The Cynet XDR (discover a lot more about it listed here) combines avoidance, detection, and details from:
- Endpoint Protection – Up coming-Generation Antivirus (NGAV) for fundamental endpoint malware avoidance and detection and Endpoint Detection and Response (EDR) for a lot more superior endpoint safety, detection, and response,
- Network Website traffic Evaluation (NTA) for determining destructive action on your network,
- Entity and Person Behavior Monitoring (EUBA) to detect anomalous consumer behaviors,
- Deception technology to trick productive intruders into exposing their presence right before injury can be done.
Response Automation
Cynet automates many tasks involved with risk detection reaction and cross-natural environment remediation, including contaminated hosts, compromised user accounts, malicious processes, and attacker-controlled network visitors.
The New Cynet Incident Motor
Cynet’s new Incident Motor can promptly enhance cybersecurity operations for any organization and assist entire the cybersecurity techniques gap.
Lots of solutions can detect threats and then quickly avert them from executing and triggering hurt. This is great and beneficial, but only signifies the initially phase in addressing a danger. We must assume that the risk identified is probable only the suggestion of the iceberg and is probable only a piece of a more substantial, coordinated attack. This is wherever the cybersecurity skill gap will become perilous.
The Cynet Incident Engine triggers an automatic investigation pursuing specific superior-risk alerts, thoroughly disclosing its root induce and scope, and implementing all the demanded remediation activities. This is presented on a one system, out of the box, prepared to provide your cybersecurity to the next amount on working day one particular. This, my mates, is the most awesome and helpful cybersecurity breakthrough I have observed in some time.
How it Operates
On selected substantial-risk alerts, shoppers can click on the Incident View button:
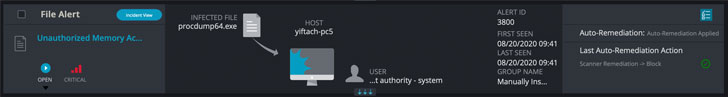
This potential customers to a web page that shows the complete established of investigation ways and remediation actions that the Incident Motor done as before long as the menace was detected.
As revealed in the screenshot beneath, a easy workflow diagram reveals the series of investigation queries and final results (blue) that lead to results (pink) that are tackled with remediation (eco-friendly). The Timeline on the suitable exhibits a additional in depth description of every move, even though the Incident Artifacts display the attack flow. The full incident is summarized in the upper textual content boxes.
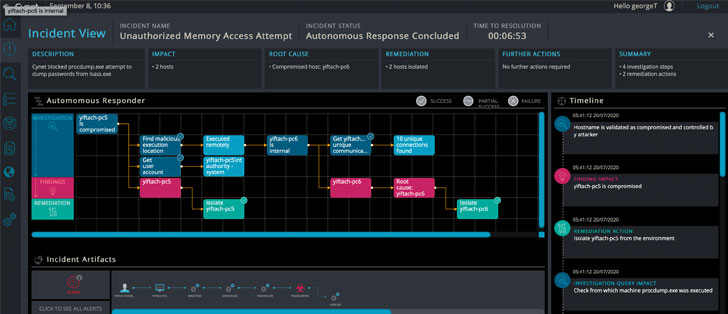
In the adhering to case in point, we see an Unauthorized Memory Entry Endeavor notify that was induced by an try to dump credentials – a popular attack circumstance. The initial warn implies that Cynet neutralized the attempt and that the qualifications have been not accessed. The Incident Engine then does its factor – it isolates the compromised host versus from which the attack was released and revealed a lateral motion. It turns out that the attack was in fact introduced remotely from another host in the atmosphere, which is the correct root bring about. This discovering is concluded by isolating the root bring about host as very well.
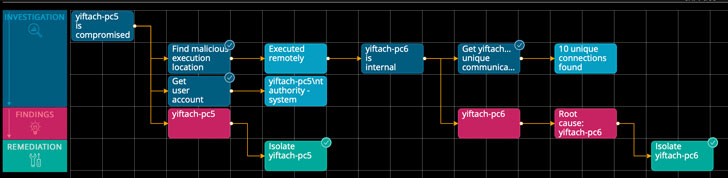
This off-the-shelf automated root lead to investigation, effects investigation, and remediation steps took Cynet’s system just beneath 7 minutes to totally carry out, all in the qualifications, saving practically hrs of analyst effort. Or, it executed a collection of duties to locate and remediate threats that some businesses would not have known have been necessary or how to do them.
MDR – CyOps
Cynet phone calls their MDR group of cybersecurity specialists CyOps. I find it awesome that Cynet incorporates 24×7 checking for all customers to be certain any authentic assaults are not ignored. They also present ad-hoc danger investigations and forensic assessment and guidebook their shoppers via any required remediation methods. CyOps is mechanically integrated in the Cynet system – at no additional cost.
This style of assistance is generally pretty highly-priced and oftentimes only available from 3rd-bash providers. With CyOps personal knowledge of the Cynet system, they can supply considerably excellent provider than MDR groups that some sellers deal with to assistance their system. Understand extra about CyOps right here.
Summary
The fully automatic Incident Motor, coupled with Cynet’s comprehensive Extended Detection and Response (XDR) system and involved Managed Detection and Reaction (MDR) provider, provides pretty a cyber safety package deal for any organization.
Several organizations proceed to rely only on EDR or a mixture of EDR and NGAV to guard the business from cyberattacks and breaches. Alternatively, Cynet’s option delivers a entire prevention and detection ability alongside with entirely automated reaction actions and a entire 24×7 MDR services to boot. If I ended up struggling from a lack of cybersecurity means, as most corporations are, my first get in touch with to increase my problem would be to Cynet.
Sign up for a Free Trial of Cynet 360 here.
Located this short article appealing? Observe THN on Fb, Twitter and LinkedIn to read through far more unique articles we submit.
Some areas of this report is sourced from:
thehackernews.com


 Bogus Notify Ripoffs Progressively Targeting Mobile Networks
Bogus Notify Ripoffs Progressively Targeting Mobile Networks