Twin cyber operations performed by point out-sponsored Iranian risk actors show their ongoing target on compiling in-depth dossiers on Iranian citizens that could threaten the security of the Islamic Republic, together with dissidents, opposition forces, and ISIS supporters, and Kurdish natives.
Tracing the considerable espionage operations to two innovative Iranian cyber-groups Domestic Kitten (or APT-C-50) and Infy, cybersecurity agency Check out Point uncovered new and current evidence of their ongoing routines that contain the use of a revamped malware toolset as perfectly as tricking unwitting end users into downloading destructive software underneath the guise of well known apps.
“Equally teams have conducted prolonged-functioning cyberattacks and intrusive surveillance strategies which goal both equally individuals’ mobile equipment and particular computers,” Look at Level researchers claimed in a new examination. “The operators of these campaigns are evidently energetic, responsive and regularly in search of new attack vectors and methods to be certain the longevity of their functions.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Even with overlaps in the victims and the variety of information amassed, the two risk actors are regarded to be independently working from a person a different. But the “synergistic impact” established by using two diverse sets of attack vectors to strike the very same targets can’t be overlooked, the researchers explained.
Domestic Kitten Mimics a Tehran Cafe Application
Domestic Kitten, which has been lively due to the fact 2016, has been recognized to goal certain groups of people today with malicious Android applications that gather sensitive data such as SMS messages, connect with logs, shots, video clips, and location details on the gadget along with their voice recordings.
Spotting four lively campaigns, the most current of which commenced in November 2020 according to Look at Level, the APT-C-50 actor has been found to leverage a large wide variety of deal with apps, counting VIPRE Mobile Security (a faux cell security software), Unique Bouquets (a repackaged variant of a sport offered on Google Play), and Iranian Lady Ninja (a wallpaper application), to distribute a piece of malware referred to as FurBall.
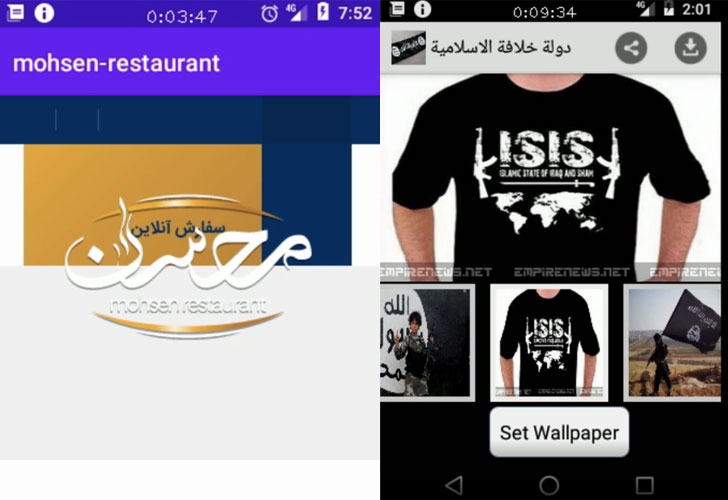
The newest November operation is no different, which can take gain of a faux app for Mohsen Cafe found in Tehran to obtain the similar aim by luring victims into setting up the app by various vectors — SMS messages with a hyperlink to download the malware, an Iranian blog site that hosts the payload, and even shared by using Telegram channels.
Outstanding targets of the attack bundled 1,200 people located in Iran, the US, Great Britain, Pakistan, Afghanistan, Turkey, and Uzbekistan, the researchers stated, with above 600 effective infections claimed.
As soon as set up, FurBall grants alone extensive permissions to execute the app just about every time routinely on machine startup and proceeds to accumulate browser heritage, hardware details, data files on the exterior SD card, and periodically exfiltrate videos, pictures, and contact documents just about every 20 seconds.
It also monitors clipboard content material, gains entry to all notifications received by the unit, and comes with abilities to remotely execute instructions issued from a command-and-control (C2) server to history audio, movie, and phone phone calls.
Curiously, FurBall appears to be dependent on a commercially readily available Spy ware known as KidLogger, implying the actors “either obtained the KidLogger source-code, or reverse-engineered a sample and stripped all extraneous areas, then added far more abilities.”
Infy Returns With New, Previously Unknown, Next-Stage Malware
First uncovered in Could 2016 by Palo Alto Networks, Infy’s (also identified as Prince of Persia) renewed action in April 2020 marks a continuation of the group’s cyber functions that have qualified Iranian dissidents and diplomatic companies across Europe for more than a ten years.
Though their surveillance endeavours took a beating in June 2016 adhering to a takedown operation by Palo Alto Networks to sinkhole the group’s C2 infrastructure, Infy resurfaced in August 2017 with anti-takeover procedures together with a new Windows data-stealer termed Foudre.
The team is also suggested to have ties to the Telecommunication Business of Iran following researchers Claudio Guarnieri and Collin Anderson disclosed proof in July 2016 that a subset of the C2 domains redirecting to the sinkhole was blocked by DNS tampering and HTTP filtering, as a result avoiding access to the sinkhole.
Then in 2018, Intezer Labs found a new model of the Foudre malware, named variation 8, that also contained an “unfamiliar binary” — now named Tonnerre by Test Place that’s utilized to increase on the abilities of the former.
“It seems that pursuing a extensive downtime, the Iranian cyber attackers have been able to regroup, fix prior issues and considerably reinforce their OPSEC functions as effectively as the technical proficiency and talents of their tools,” the scientists reported.
As several as three variations of Foudre (20-22) have been uncovered due to the fact April 2020, with the new variants downloading Tonnerre 11 as the up coming-phase payload.
The attack chain commences by sending phishing e-mails that contains lure paperwork published in Persian, that when closed, runs a malicious macro that drops and executes the Foudre backdoor, which then connects to the C2 server to down load the Tonnerre implant.
Aside from executing commands from the C2 server, recording appears, and capturing screenshots, what makes Tonnerre stand out is its use of two sets of C2 servers — one to acquire instructions and down load updates using HTTP and a second server to which the stolen details is exfiltrated through FTP.
At 56MB, Tonnerre’s unusual dimensions is also most likely to get the job done in its favor and evade detection as quite a few sellers ignore significant documents in the course of malware scans, the researchers noted.
However, as opposed to Domestic Kitten, only a couple of dozen victims were being found to be specific in this attack, together with these from Iraq, Azerbaijan, the U.K., Russia, Romania, Germany, Canada, Turkey, the U.S., Netherlands, and Sweden.
“The operators of these Iranian cyber espionage strategies appear to be fully unaffected by any counter-pursuits carried out by others, even although they were being unveiled and even stopped in the previous — they simply just will not quit,” claimed Yaniv Balmas, head of cyber study at Verify Issue.
“These marketing campaign operators only master from the earlier, modify their ways, and go on to wait around for a while for the storm to move to only go at it all over again. Additionally, it can be worthy to be aware the sheer volume of means the Iranian routine is willing to devote on exerting their handle.”
Discovered this posting appealing? Abide by THN on Facebook, Twitter and LinkedIn to read far more distinctive information we publish.
Some pieces of this posting are sourced from:
thehackernews.com


 Tens of Thousands of Patient Files Leaked in US Hospital Attacks
Tens of Thousands of Patient Files Leaked in US Hospital Attacks