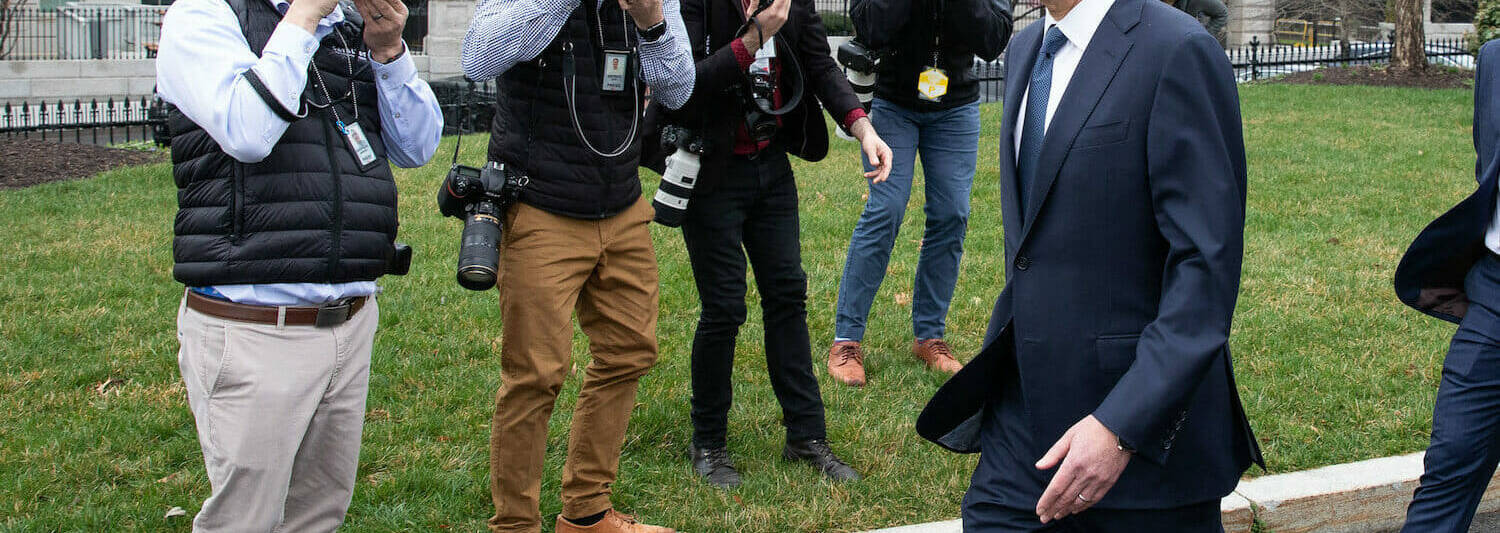
Secretary of the Treasury Steven Mnuchin, March 13, 2020, outside of the West Wing of the White House. The department was among the the entities breached in a malicious source chain attack applying the SolarWinds IT management system. (Formal White House Photograph by Keegan Barber)
The Section of Homeland Security’s cybersecurity agency is demanding drastic action of federal companies, after the Department of Treasury and Countrywide Telecommunications and Information and facts Administration have been breached in a malicious source chain attack using the SolarWinds IT management system.
The Cybersecurity and Infrastructure Security Company produced Emergency Directive 21-01 Sunday evening, adhering to a Reuters report that hackers experienced exfiltrated information and facts from NTIA and Treasury. The Washington Article afterwards tied those people attacks to past week’s FireEye attacks and all three to Russian intelligence, particularly APT 29.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The compromise of SolarWinds’ Orion Network Management Products and solutions poses unacceptable dangers to the security of federal networks,” CISA Acting Director Brandon Wales mentioned in a assertion to the press. “Tonight’s directive is supposed to mitigate possible compromises inside of federal civilian networks, and we urge all our companions — in the public and private sectors — to assess their publicity to this compromise and to safe their networks towards any exploitation.”
FireEye documented Sunday that SolarWinds pushed numerous trojanized updates involving March and May of 2020, installing what the security organization is calling the Sunburst backdoor.
The attacks are not minimal to governing administration, wrote FireEye, and also strike the consulting, technology, telecom sectors. Nor have been the attacks confined to The us, also focusing on Europe, Asia and the Center East.
Soon after putting in Sunburst, attackers leverage a memory-only dropper system to set up Cobolt Strike.
FireEye notes a number of prospects for detecting the attack, such as checking logs for “SMB sessions that demonstrate obtain to legit directories and stick to a delete-produce-execute-delete-produce pattern in a quick volume of time,” as effectively as single methods generating connections employing various accounts. The FireEye post also consists of details to blacklist command and command domain era algorithms and recognized infrastructure IPs.
But, notes FireEye, detecting can take dilligence. As the company writes in the weblog submit, “This is some of the best operational security that FireEye has noticed in a cyber attack, concentrating on evasion and leveraging inherent have confidence in. Having said that, it can be detected through persistent defense.”
SolarWinds is a popular system in and outdoors of governance. Sources assume lots of more victims will very likely surface.
Even though the CISA needs are only obligatory within just the governing administration devices to which it can issue an emergency order, other companies might be intrigued in subsequent accommodate.
CISA ordered govt businesses with the ability to forensically assess memory or network targeted visitors to look at for new accounts and indicators of compromise. It has purchased all agencies under its purchase to “immediately disconnect or electric power down SolarWinds Orion goods, versions 2019.4 through 2020.2.1 HF1, from their network” and block all connections from systems employing those solutions.
Some components of this short article are sourced from:
www.scmagazine.com

 New Windows Trojan Steals Browser Credentials, Outlook Files
New Windows Trojan Steals Browser Credentials, Outlook Files