There would seem to be a new ransomware story each individual day – a new ransomware attack, a new ransomware approach, criminals not offering encryption keys right after getting ransom payments, private info being publicly released by ransomware attackers—it by no means ends.
Just final month, the FBI, the Division of Overall health and Human Providers (HHS), and the Cybersecurity and Infrastructure Security Company (CISA) issued a report warning of an imminent menace of ransomware attacks on US hospitals and well being treatment suppliers.
The list of ransomware variants is extensive and developing, which include Maze, Ragnar Locker, Netlocker, Wastedlocker, FTCode, Tycoon, TrickBot, REvil, and numerous much more.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Ransomware takes advantage of a selection of procedures to infect techniques and finally steal and/or encrypt a company’s information. Several of the techniques are acknowledged, but new, unfamiliar tactics can arrive at any second.
SMEs Are Specifically Vulnerable
A new whitepaper about new approaches XDR platform safeguards from ransomware [download here] notes that little to medium-sized enterprises (SMEs) are particularly susceptible to ransomware attacks. SMEs typically have much less defense mechanisms in spot and less expert cybersecurity team as when compared to larger sized enterprises.
The crucial to defending towards ransomware is 1st, protecting against it from infecting any technique in the initially spot. But, if ransomware does attain a foothold, it is critical to straight away detect the infection and kill all related ransomware procedures, alongside with isolating all infected equipment to incorporate the an infection. So the ideal technique for defending from ransomware is initially avoidance, followed by speedy detection, containment, and removing.
Are living webinar: A layered, unified platform technique for ransomware protection
Cynet’s new ransomware safety overview lays out how the company relies on multiple preventions, detection, and remediation levels to avoid its customers from falling sufferer to ransomware.
The Cynet method appears to react to the present complexities of ransomware:
To sign up for a are living demonstration of the Cynet XDR layered solution for ransomware defense, click on here.
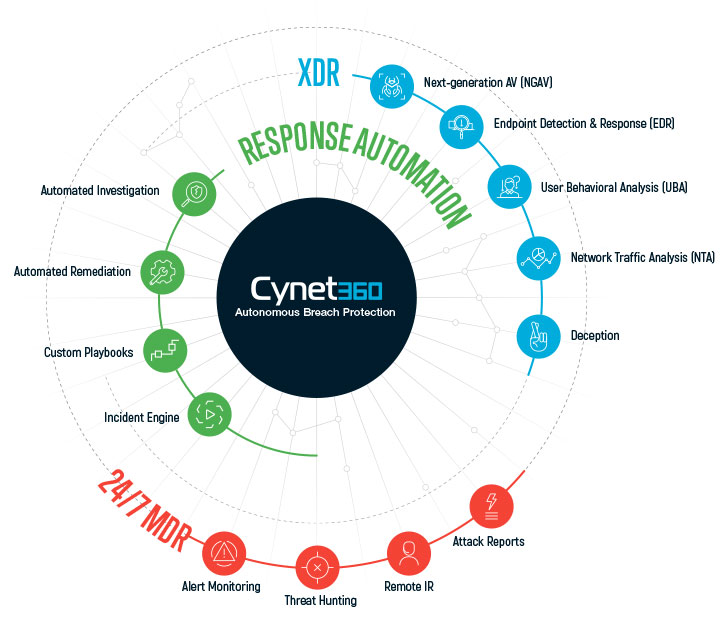 Cynet’s various security levels to avert ransomware
Cynet’s various security levels to avert ransomware
Because Cynet is routinely referred to as in to assist firms that have fallen sufferer to ransomware carry out a comprehensive Incident Response, they’ve made a remarkably robust set of ransomware protections.
Sad to say, quite a few corporations only study about the importance of having extensive ransomware protections in spot just after suffering from the devastation brought about by remaining a ransomware victim.
Avoidance and Detection
Cynet’s solution starts with various preventions and detection strategies, which includes widespread subsequent-technology antivirus (NGAV), and provides in serious-time memory protection to detect ransomware behaviors from unknown variants, critical part filtering to avert ransomware from harvesting credentials and spreading, true-time file filtering to stop ransomware from altering existing documents and deception technology to entice ransomware into accessing decoy hosts and documents.
Investigation and Remediation
Whilst most ransomware security solution providers concentration pretty much solely on prevention and detection, Cynet also spots sizeable emphasis on swiftly and carefully responding to ransomware attacks submit-detection.
Importantly, Cynet emphasizes that the prevention and detection of an attack occasion are critical, but only the initially phase. Businesses have to believe that the malicious artifact determined is only the tip of an iceberg.
 Instance of Cynet’s Remediation Playbook for Instantly Responding to Ransomware Alerts
Instance of Cynet’s Remediation Playbook for Instantly Responding to Ransomware Alerts
Cynet mechanically triggers an automatic investigation following just about every endpoint, person, or network inform, to disclose its root lead to and scope and implement necessary remediation actions throughout the ecosystem. Due to the fact Cynet is an XDR solution, it can utilize a quite broad assortment of remediation actions specifically from its platform throughout endpoints, networks, consumers, and data files.
They also offer automated remediation playbooks, which are quite important for stringing several remediation steps collectively to respond to ransomware threats.
Final Feelings
Following speaking with quite a few representatives from corporations that have had to dig them selves out of a popular ransomware an infection, you unquestionably do not want to be in that condition. Every one a single wished they had much better protections in spot so they could have averted the excruciating expertise.
Possessing a broad arsenal of avoidance, detection, and reaction applications are critical to protect against your firm from starting to be the up coming ransomware sufferer.
Download the Ransomware Protection Overview listed here.
Found this article fascinating? Observe THN on Facebook, Twitter and LinkedIn to browse more unique written content we article.
Some areas of this write-up are sourced from:
thehackernews.com


 ‘Amnesia:33’ TCP/IP Flaws Affect Millions of IoT Devices
‘Amnesia:33’ TCP/IP Flaws Affect Millions of IoT Devices