An assessment of off-the-shelf packages hosted on the NuGet repository has disclosed 51 unique software package elements to be vulnerable to actively exploited, substantial-severity vulnerabilities, at the time yet again underscoring the risk posed by 3rd-party dependencies to the software package development procedure.
In mild of the escalating selection of cyber incidents that concentrate on the software program source chain, there is an urgent require to assess this sort of third-party modules for any security challenges and lower the attack floor, ReversingLabs researcher Karlo Zanki said in a report shared with The Hacker Information.
NuGet is a Microsoft-supported mechanism for the .NET platform and features as a offer supervisor built to allow builders to share reusable code. The framework maintains a central repository of above 264,000 exceptional offers that have collectively produced extra than 109 billion package downloads.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“All recognized precompiled application components in our study ended up different versions of 7Zip, WinSCP and PuTTYgen, plans that present intricate compression and network performance,” Zanki discussed. “They are continuously up to date to strengthen their features and to handle recognized security vulnerabilities. Having said that, sometimes it transpires that other application packages get up-to-date but continue to preserve making use of numerous a long time old dependencies containing recognised vulnerabilities.”
In a single occasion, it was identified that “WinSCPHelper” — a remote server file administration library and which has been downloaded more than 35,000 moments — use an old and vulnerable WinSCP variation 5.11.2, while WinSCP edition 5.17.10 released previously this January addresses a critical arbitrary execution flaw (CVE-2021-3331), so exposing end users of the offer to the vulnerability.
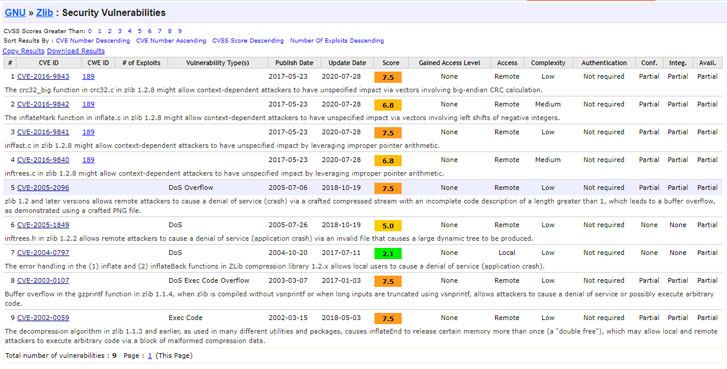
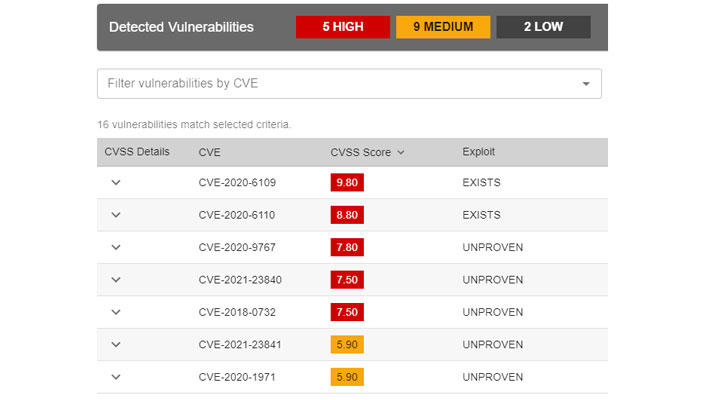
On top of that, the researchers recognized that extra than 50,000 software program elements extracted from NuGet packages have been statically joined to a susceptible model of “zlib” knowledge compression library, rendering them vulnerable to a amount of identified security issues this kind of as CVE-2016-9840, CVE-2016-9841, CVE-2016-9842, and CVE-2016-9843.

Some of the packages that were observed to have a zlib vulnerability are “DicomObjects” and “librdkafka.redist”, just about every of which have been downloaded no fewer than 50,000 and 18.2 million situations. A make a difference of far more issue is that “librdkafka.redist” is outlined as a dependency for a number of other common offers, counting Confluent’s .NET Client for Apache Kafka (Confluent.Kafka), which, in turn, has been downloaded more than 17.6 million times to date.
“Organizations building application methods will need to develop into additional mindful of such risks, and require to come to be additional associated in their handling,” Zanki said. “Equally the inputs and final outputs of the application improvement course of action require to be checked for tampering and code high quality issues. “Transparent application enhancement is 1 of the keystones essential to enable early detection and avoidance of application offer-chain attacks.”
Identified this post intriguing? Observe THN on Fb, Twitter and LinkedIn to browse extra distinctive material we submit.
Some sections of this report are sourced from:
thehackernews.com


![[whitepaper] xdr vs. ndr/nta – what do organizations truly need](https://thecybersecurity.news/data/2021/07/Whitepaper-XDR-vs-NDRNTA-–-What-do-Organizations-Truly-Need-80x80.jpg) [Whitepaper] XDR vs. NDR/NTA – What do Organizations Truly Need to Stay Safe?
[Whitepaper] XDR vs. NDR/NTA – What do Organizations Truly Need to Stay Safe?