A new investigation released by a group of academics has located that anti-virus systems for Android keep on to remain susceptible against unique permutations of malware, in what could pose a serious risk as destructive actors evolve their toolsets to better evade evaluation.
“Malware writers use stealthy mutations (morphing/obfuscations) to repeatedly create malware clones, thwarting detection by signature based detectors,” the researchers explained. “This attack of clones critically threatens all the cellular platforms, in particular Android.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The results ended up released in a research last 7 days by scientists from Adana Science and Technology College, Turkey, and the Nationwide University of Science and Technology, Islamabad, Pakistan.
As opposed to iOS, apps can be downloaded from 3rd-party resources on Android devices, increasing the probability that unwitting people can install unverified and lookalike apps that clone a respectable app’s performance but are developed to trick targets into downloading apps laced with fraudulent code that are able of thieving sensitive info.
What is far more, malware authors can develop on this strategy to establish a number of clones of the rogue software package with various stages of abstraction and obfuscation to disguise their true intent and slip by way of the protection boundaries established by anti-malware engines.
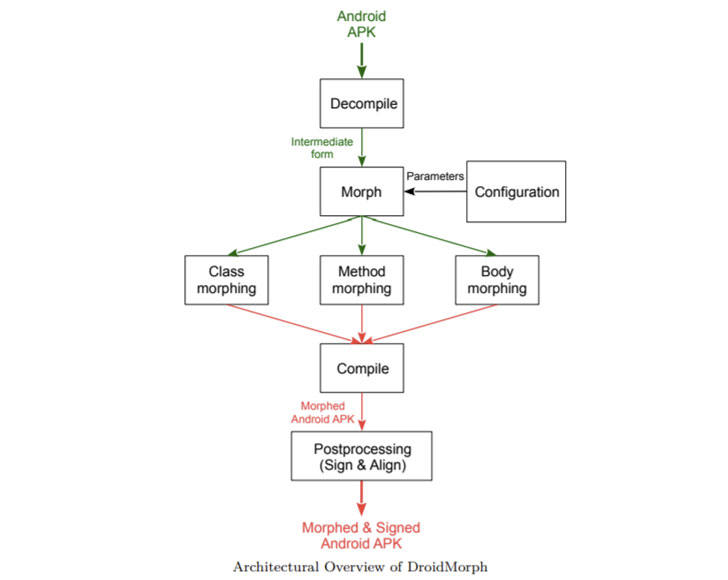
To exam and examine the resilience of commercially offered anti-malware goods towards this attack, the researchers designed a resource identified as DroidMorph, which allows Android purposes (APKs) to be “morphed” by decompiling the documents to an intermediate sort which is then modified and compiled to produce clones, the two benign and malware.

Morphing could be at distinctive ranges, the scientists mentioned, these as people that involve modifying the course and technique names in the supply code or one thing non-trivial that could alter the execution circulation of the application, which include the phone graph and the management-flow graph.
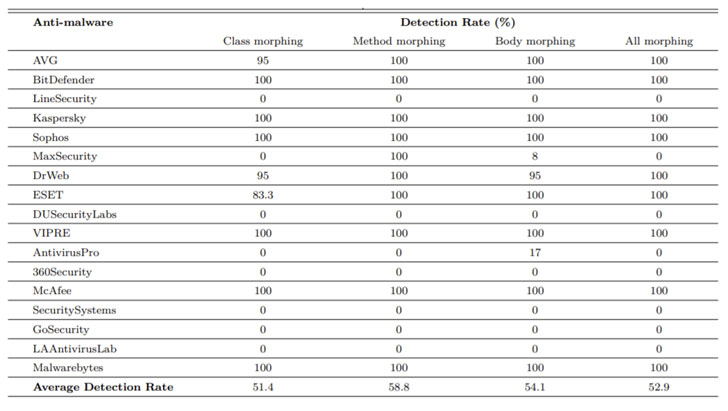
In a test conducted working with 1,771 morphed APK variants generated via DroidMorph, the researchers identified that 8 out of 17 main professional anti-malware plans unsuccessful to detect any of the cloned programs, with an ordinary detection amount of 51.4% for class morphing, 58.8% for approach morphing, and 54.1% for physique morphing observed throughout all courses.
The anti-malware programs that were effectively bypassed include LineSecurity, MaxSecurity, DUSecurityLabs, AntivirusPro, 360Security, SecuritySystems, GoSecurity, and LAAntivirusLab.
As upcoming function, the scientists outlined that they intend to add much more obfuscations at different degrees as perfectly as allow morphing of metadata facts this sort of as permissions that are embedded in an APK file with an purpose to bring down the detection costs.
Uncovered this write-up attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to browse much more unique articles we post.
Some sections of this write-up are sourced from:
thehackernews.com


 Nuclear Research Institute Breached by Suspected North Korean Hackers
Nuclear Research Institute Breached by Suspected North Korean Hackers