Law enforcement authorities in the Netherlands have arrested two alleged persons belonging to a Dutch cybercriminal collective who have been concerned in producing, selling, and leasing innovative phishing frameworks to other danger actors in what’s acknowledged as a “Fraud-as-a-Company” operation.
The apprehended suspects, a 24-12 months-outdated program engineer, and a 15-calendar year-old boy, are claimed to have been the most important developer and vendor of the phishing frameworks that have been used to collect login data from lender consumers. The attacks mostly singled out customers in the Netherlands and Belgium.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The phishing frameworks let attackers with minimum techniques to improve the creation and structure of phishing strategies to carry out huge fraudulent operations all the even though bypassing 2FA,” Team-IB Europe’s Roberto Martinez, senior menace intelligence analyst, and Anton Ushakov, deputy head of the large-tech criminal offense investigation section, in a report, including the gang “advertises their companies and interacts with fellow cybercriminals on Telegram messenger.”
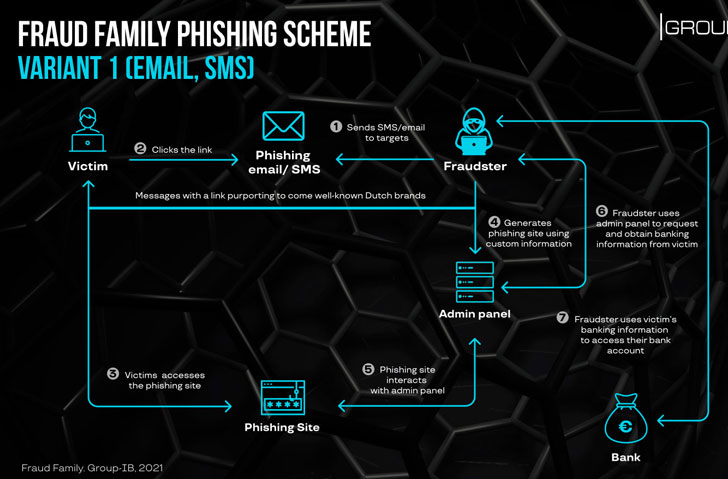
Infections involving Fraud Family commences with an email, SMS, or WhatsApp information impersonating very well-recognized nearby manufacturers made up of destructive hyperlinks that, when clicked, redirect the unsuspecting recipient to adversary-managed payment info-thieving phishing internet websites. In an alternative attack circumstance, the fraudsters were observed posing as a customer on a Dutch categorised advertising and marketing system to call a seller and subsequently go the discussion to WhatsApp to trick the latter into going to a phishing web page.
Group-IB researchers noted the “substantial level of personalization” presented by the phishing internet sites, which not only impersonate a respectable Dutch market, but also claims to use a effectively-known e-commerce payment technique in the country, only to direct the sufferer to a pretend bank webpage from wherever the qualifications are siphoned based mostly on the lender chosen.

“When victims submit their banking qualifications, the phishing website sends them to the fraudster-managed web panel,” Team-IB said. “This a person basically notifies the miscreants that a new victim is on the web. The scammers can then request extra information and facts that will aid them to get accessibility to the lender accounts, including two factor authentication tokens, and private identifiable information.”
According to messages posted by the group on Telegram, the web panels — just one of which is a fork of yet another panel called “U-Admin” — can be rented for €200 a month (Convey Panel), or for €250 should really other cybercriminals choose for the Trustworthy Panel (or Dependable Admin). No less than eight Telegram channels operated by Fraud Spouse and children have been recognized to date, with the channels boasting 2,000 subscribers concerning them.
“The attacks that count on Fraud Family’s infrastructure greater towards the ultimate months of 2020,” Group-IB scientists said. “This pattern proceeds in 2021 with the visual appearance of Categorical Panel and Dependable Panel.”
Found this posting exciting? Comply with THN on Facebook, Twitter and LinkedIn to read through much more unique information we post.
Some components of this posting are sourced from:
thehackernews.com


 Google coding typo effectively bricks Chrome OS devices
Google coding typo effectively bricks Chrome OS devices