Numerous security weaknesses have been disclosed in MediaTek system-on-chips (SoCs) that could have enabled a threat actor to elevate privileges and execute arbitrary code in the firmware of the audio processor, properly making it possible for the attackers to carry out a “substantial eavesdrop marketing campaign” without the need of the users’ expertise.
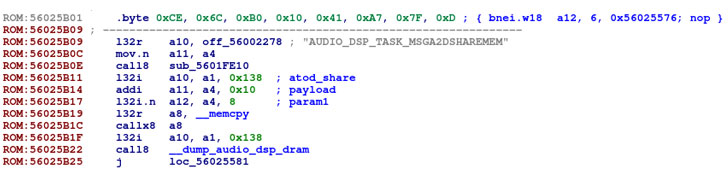
The discovery of the flaws is the final result of reverse-engineering the Taiwanese company’s audio digital sign processor (DSP) device by Israeli cybersecurity organization Test Issue Analysis, ultimately acquiring that by stringing them with each other with other flaws existing in a smartphone manufacturer’s libraries, the issues uncovered in the chip could direct to nearby privilege escalation from an Android software.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“A malformed inter-processor message could probably be utilized by an attacker to execute and conceal malicious code within the DSP firmware,” Verify Position security researcher Slava Makkaveev reported in a report. “Since the DSP firmware has entry to the audio details move, an attack on the DSP could probably be made use of to eavesdrop on the person.”
Tracked as CVE-2021-0661, CVE-2021-0662, and CVE-2021-0663, the a few security issues worry a heap-based buffer overflow in the audio DSP ingredient that could be exploited to accomplish elevated privileges. The flaws impact chipsets MT6779, MT6781, MT6785, MT6853, MT6853T, MT6873, MT6875, MT6877, MT6883, MT6885, MT6889, MT6891, MT6893, and MT8797 spanning throughout versions 9., 10., and 11. of Android.
“In audio DSP, there is a achievable out of bounds write thanks to an incorrect bounds look at. This could lead to neighborhood escalation of privilege with Technique execution privileges necessary. Person conversation is not wanted for exploitation,” the chipmaker stated in an advisory released past thirty day period.
A fourth issue uncovered in the MediaTek audio hardware abstraction layer aka HAL (CVE-2021-0673) has been fixed as of Oct and is envisioned to be published in the December 2021 MediaTek Security Bulletin.

In a hypothetical attack situation, a rogue application mounted by way of social engineering usually means could leverage its access to Android’s AudioManager API to goal a specialized library — named Android Aurisys HAL — which is provisioned to talk with the audio drivers on the gadget and send specially crafted messages, which could final result in the execution of attack code and theft of audio-relevant facts.
MediaTek, pursuing disclosure, reported it has created acceptable mitigations readily available to all unique equipment makers, including it located no evidence that the flaws are now becoming exploited. Furthermore, the firm has proposed consumers to update their gadgets as and when patches grow to be offered and to only install purposes from trusted marketplaces this sort of as the Google Perform Shop.
Observed this article attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to study much more special material we write-up.
Some elements of this write-up are sourced from:
thehackernews.com


 UK gov introduces cyber bill designed to clamp down on unsecure devices
UK gov introduces cyber bill designed to clamp down on unsecure devices