The Emotet malware is now staying leveraged by ransomware-as-a-assistance (RaaS) groups, including Quantum and BlackCat, just after Conti’s official retirement from the menace landscape this calendar year.
Emotet started off as a banking trojan in 2014, but updates additional to it more than time have reworked the malware into a extremely potent risk that is capable of downloading other payloads on to the victim’s machine, which would allow for the attacker to management it remotely.
Even though the infrastructure linked with the invasive malware loader was taken down as component of a legislation enforcement effort in January 2021, the Conti ransomware cartel is stated to have played an instrumental part in its comeback late last yr.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“From November 2021 to Conti’s dissolution in June 2022, Emotet was an distinctive Conti ransomware software, nevertheless, the Emotet an infection chain is at the moment attributed to Quantum and BlackCat,” AdvIntel explained in an advisory printed last 7 days.
Standard attack sequences entail the use of Emotet (aka SpmTools) as an preliminary obtain vector to drop Cobalt Strike, which then is utilised as a article-exploitation resource for ransomware functions.
The notorious Conti ransomware gang might have dissolved, but several of its customers stay as lively as at any time either as component of other ransomware crews like BlackCat and Hive or as independent groups concentrated on knowledge extortion and other legal endeavors.
Quantum is also a Conti spin-off team that, in the intervening months, has resorted to the technique of phone-again phishing – dubbed BazaCall or BazarCall – as a indicates to breach targeted networks.
“Conti affiliates use a assortment of original obtain vectors together with phishing, compromised credentials, malware distribution, and exploiting vulnerabilities,” Recorded Potential famous in a report revealed previous month.
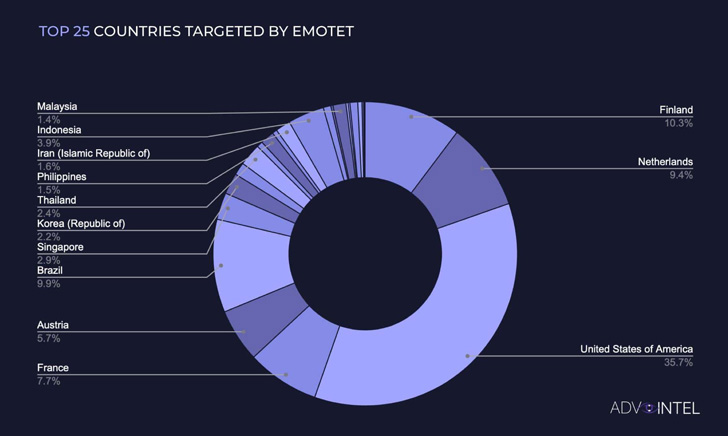
AdvIntel stated it observed more than 1,267,000 Emotet bacterial infections across the entire world because the start out of the 12 months, with action peaks registered in February and March coinciding with Russia’s invasion of Ukraine.

A second surge in infections happened in between June and July, owing to the use by ransomware teams these types of as Quantum and BlackCat. Data captured by the cybersecurity agency shows that the most Emotet-focused place is the U.S., adopted by Finland, Brazil, the Netherlands, and France.
ESET beforehand documented a 100-fold leap in Emotet detections in the course of the 1st 4 months of 2022 in comparison to the previous 4 months from September to December 2021.
In accordance to Israeli cybersecurity corporation Examine Level, Emotet dropped from very first to fifth location in the list of most common malware for August 2022, coming driving FormBook, Agent Tesla, XMRig, and GuLoader.
Located this write-up attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to examine much more unique information we write-up.
Some pieces of this short article are sourced from:
thehackernews.com


 Microsoft Teams’ GIFShell Attack: What Is It and How You Can Protect Yourself from It
Microsoft Teams’ GIFShell Attack: What Is It and How You Can Protect Yourself from It