Emotet, the notorious email-centered Windows malware powering a number of botnet-driven spam strategies and ransomware attacks, was routinely wiped from contaminated personal computers en masse subsequent a European law enforcement operation.
The growth comes 3 months immediately after a coordinated disruption of Emotet as aspect of “Procedure Ladybird” to seize manage of servers utilised to run and retain the malware network. The orchestrated work noticed at minimum 700 servers linked with the botnet’s infrastructure neutered from the within, as a result avoiding further exploitation.
Law enforcement authorities from the Netherlands, Germany, the U.S., U.K., France, Lithuania, Canada, and Ukraine were included in the worldwide motion.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Previously, the Dutch police, which seized two central servers found in the country, said it experienced deployed a software program update to counter the menace posed by Emotet effectively. “All infected computer units will quickly retrieve the update there, soon after which the Emotet infection will be quarantined,” the agency pointed out back in January.
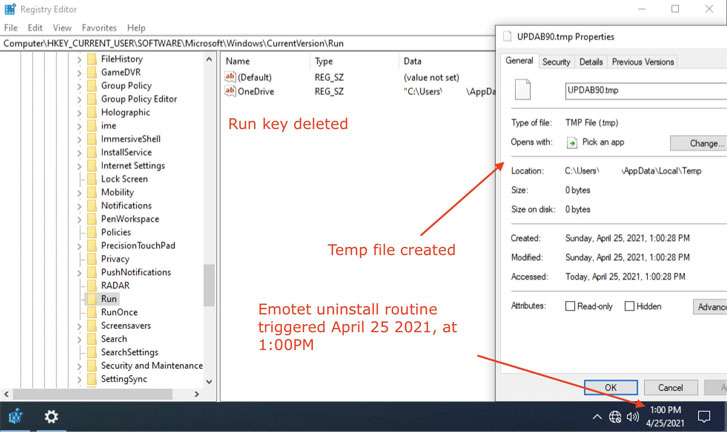
This concerned pushing a 32-bit payload named “EmotetLoader.dll” by way of the same channels that had been used to distribute the primary Emotet to all compromised machines. The cleanup routine, which was set to induce by itself mechanically on April 25, 2021, worked by getting rid of the malware from the unit, in addition to deleting the autorun Registry vital and terminating the method.
Now on Sunday, cybersecurity firm Malwarebytes Sunday verified that its Emotet-infected device that experienced received the regulation enforcement payload experienced properly initiated the uninstallation regime and taken off by itself from the Windows technique.

As of crafting, Abuse.ch’s Feodo Tracker exhibits none of the Emotet servers are online.
The mass motion marks the 2nd time regulation enforcement organizations have intervened to take out malware from compromised machines.
Earlier this thirty day period, the U.S. governing administration took methods to remove web shell backdoors dropped by the Hafnium risk actor from Microsoft Exchange servers situated in the nation that ended up breached making use of ProxyLogon exploits.
Pursuing the court-authorized operation, the Federal Bureau of Investigation mentioned it’s in the procedure of notifying all the corporations from which it experienced eradicated web shells, implying the intelligence company accessed the methods with out their know-how.
Located this short article attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to examine extra distinctive articles we put up.
Some areas of this posting are sourced from:
thehackernews.com


 US Drilling Giant Gyrodata Reveals Employee Data Breach
US Drilling Giant Gyrodata Reveals Employee Data Breach