Social engineering strategies involving the deployment of the Emotet malware botnet have been observed utilizing “unconventional” IP tackle formats for the to start with time in a bid to sidestep detection by security answers.
This includes the use of hexadecimal and octal representations of the IP tackle that, when processed by the underlying running programs, get quickly transformed “to the dotted decimal quad illustration to initiate the request from the distant servers,” Development Micro’s Danger Analyst, Ian Kenefick, claimed in a report Friday.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
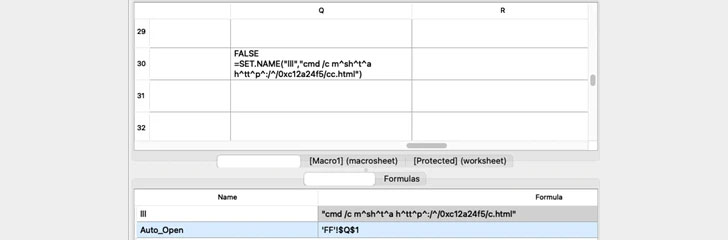
The infection chains, as with past Emotet-linked attacks, intention to trick users into enabling document macros and automate malware execution. The document takes advantage of Excel 4. Macros, a function that has been frequently abused by malicious actors to provide malware.
As soon as enabled, the macro invokes a URL that’s obfuscated with carets, with the host incorporating a hexadecimal representation of the IP deal with — “h^tt^p^:/^/0xc12a24f5/cc.html” — to execute an HTML software (HTA) code from the distant host.
A second variant of the phishing attack follows the exact same modus operandi, the only difference currently being that the IP address is now coded in the octal structure — “h^tt^p^:/^/0056.0151.0121.0114/c.html”.
“The unconventional use of hexadecimal and octal IP addresses may well end result in evading recent methods reliant on pattern matching,” Kenefick stated. “Evasion tactics like these could be viewed as evidence of attackers continuing to innovate to thwart pattern-primarily based detection options.”
The improvement comes amid renewed Emotet action late past year following a 10-thirty day period-extensive hiatus in the wake of a coordinated legislation enforcement operation. In December 2021, researchers uncovered proof of the malware evolving its methods to fall Cobalt Strike Beacons specifically on to compromised systems.
The conclusions also get there as Microsoft discovered plans to disable Excel 4. (XLM) Macros by default to safeguard consumers from security threats. “This environment now defaults to Excel 4. (XLM) macros remaining disabled in Excel (Establish 16..14427.10000),” the organization declared past 7 days.
Uncovered this post exciting? Adhere to THN on Facebook, Twitter and LinkedIn to read through additional distinctive written content we article.
Some components of this short article are sourced from:
thehackernews.com



 High-Severity Rust Programming Bug Could Lead to File, Directory Deletion
High-Severity Rust Programming Bug Could Lead to File, Directory Deletion