Regulation enforcement companies from as lots of as eight nations around the world dismantled the infrastructure of Emotet, a notorious email-centered Windows malware guiding numerous botnet-driven spam strategies and ransomware attacks about the previous decade.
The coordinated takedown of the botnet on Tuesday — dubbed “Operation Ladybird” — is the consequence of a joint effort amongst authorities in the Netherlands, Germany, the U.S., the U.K., France, Lithuania, Canada, and Ukraine to take manage of servers used to run and regulate the malware network.
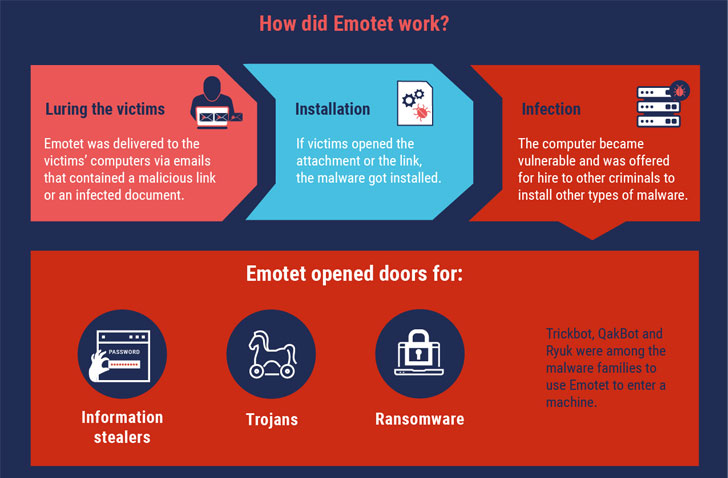
“The Emotet infrastructure fundamentally acted as a primary doorway opener for personal computer devices on a world wide scale,” Europol claimed. “What designed Emotet so hazardous is that the malware was presented for retain the services of to other cybercriminals to install other sorts of malware, these as banking Trojans or ransomware, on to a victim’s personal computer.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
More Than a Malware
Given that its initially identification in 2014, Emotet has progressed from its initial roots as a credential stealer and banking Trojan to a potent “Swiss Army knife” that can serve as a downloader, information stealer, and spambot relying on how it can be deployed.

Identified for currently being continuously underneath enhancement, cybercrime assistance updates itself on a regular basis to strengthen stealthiness, persistence, and add new spying capabilities by means of a extensive vary of modules, such as a Wi-Fi spreader to detect and compromise contemporary victims connected to close by Wi-Fi networks.
Very last 12 months, the malware was linked to many botnet-driven spam campaigns and even capable of offering more hazardous payloads such as TrickBot and Ryuk ransomware by renting its botnet of compromised equipment to other malware teams.
“The Emotet team managed to acquire e-mail as an attack vector to a subsequent stage,” Europol explained.
700 Emotet Servers Seized
The U.K.’s Countrywide Crime Company (NCA) said the procedure took virtually two yrs to map the infrastructure of Emotet, with a number of attributes in the Ukrainian city of Kharkiv raided to confiscate laptop tools utilised by the hackers.
The Ukrainian Cyberpolice Office also arrested two people today allegedly involved in the botnet’s infrastructure routine maintenance, both equally of whom are facing 12 decades in jail if observed guilty.
“Assessment of accounts utilized by the group guiding Emotet showed $10.5 million becoming moved in excess of a two-year interval on just one Digital Forex system,” the NCA explained, incorporating “practically $500,000 had been used by the team more than the very same time period to preserve its legal infrastructure.”
Globally, Emotet-joined damages are explained to have price tag about $2.5 billion, Ukrainian authorities mentioned.
With at the very least 700 servers operated by Emotet across the earth now getting been taken down from the inside, machines contaminated by the malware are now directed to this regulation enforcement-infrastructure, so preventing even more exploitation.
In addition, the Dutch National Law enforcement has released a tool to verify for probable compromise, based on a dataset that contains 600,000 e-mail addresses, usernames, and passwords that were being discovered during the operation.
Emotet to Be Wiped En Masse on March 25, 2021
The Dutch law enforcement, which seized two central servers located in the place, said it has deployed a application update to neutralize the threat posed by Emotet effectively.
“All infected computer units will quickly retrieve the update there, following which the Emotet an infection will be quarantined,” the agency explained. In accordance to a tweet from a security researcher who goes by the Twitter manage milkream, Emotet is envisioned to be wiped on April 25, 2021, at 12:00 nearby time from all compromised devices.
Supplied the character of the takedown operation, it remains to be noticed if Emotet can phase a comeback. If it does, it would not be the to start with time a botnet survived important disruption attempts.
As of creating, Abuse.ch’s Feodo Tracker exhibits at the very least 20 Emotet servers are however online.
“A blend of each up-to-date cybersecurity tools (antivirus and functioning devices) and cybersecurity recognition is vital to prevent falling sufferer to subtle botnets like Emotet,” Europol cautioned.
“Buyers need to cautiously verify their e-mail and stay away from opening messages and primarily attachments from mysterious senders. If a message seems far too very good to be legitimate, it most likely is and e-mails that implore a sense of urgency really should be averted at all expenditures.”
Located this post interesting? Comply with THN on Facebook, Twitter and LinkedIn to go through additional exclusive content material we article.
Some pieces of this posting are sourced from:
thehackernews.com


 Even dead employees pose a security risk when their accounts are still active
Even dead employees pose a security risk when their accounts are still active