An adversary recognised for concentrating on the fintech sector at least considering the fact that 2018 has switched up its ways to incorporate a new Python-centered remote entry Trojan (RAT) that can steal passwords, files, browser cookies, email credentials, and other sensitive details.
In an investigation published by Cybereason researchers yesterday, the Evilnum group has not only tweaked its infection chain but has also deployed a Python RAT termed “PyVil RAT,” which possesses abilities to get data, get screenshots, capture keystrokes facts, open up an SSH shell and deploy new applications.
“Due to the fact the very first reports in 2018 via right now, the group’s TTPs have evolved with different applications whilst the team has continued to concentrate on fintech targets,” the cybersecurity company reported.
“These variations include things like a alter in the chain of an infection and persistence, new infrastructure that is expanding about time, and the use of a new Python-scripted Remote Obtain Trojan (RAT)” to spy on its infected targets.
In excess of the very last two a long time, Evilnum has been connected to various malware campaigns against companies across the United kingdom and EU involving backdoors composed in JavaScript and C# as effectively as as a result of applications bought from the Malware-as-a-Services service provider Golden Chickens.
Back in July, the APT team was located focusing on providers with spear-phishing emails that contain a website link to a ZIP file hosted on Google Travel to steal software package licenses, customer credit card data, and investments and investing files.
Although the modus operandi of gaining an initial foothold in the compromised system continues to be the similar, the infection course of action has witnessed a main shift.
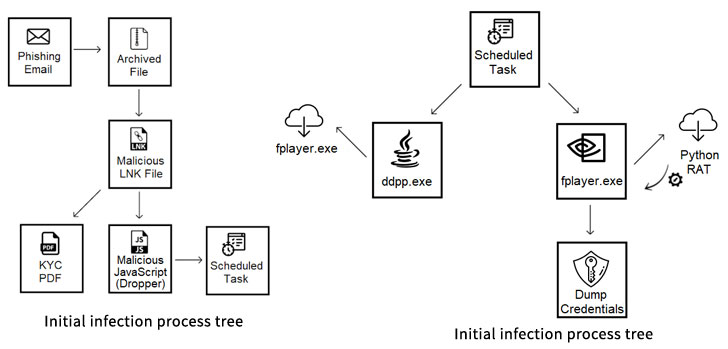
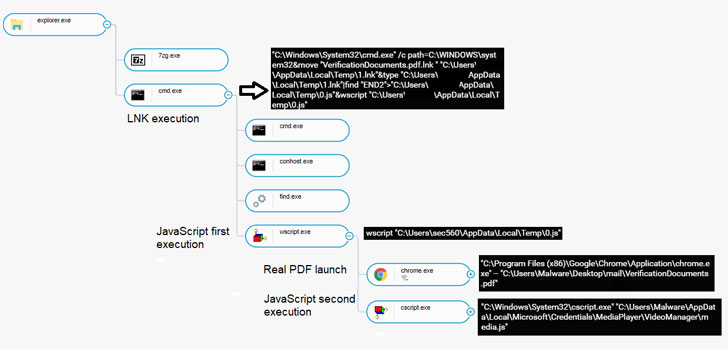
Apart from applying spear-phishing e-mail with phony know your customer (KYC) paperwork to trick workers of the finance industry into triggering the malware, the assaults have moved absent from applying JavaScript-based mostly Trojans with backdoor capabilities to a bare-bones JavaScript dropper that provides destructive payloads concealed in modified variations of authentic executables in an try to escape detection.
“This JavaScript is the 1st stage in this new an infection chain, culminating with the delivery of the payload, a Python created RAT compiled with py2exe that Nocturnus scientists dubbed PyVil RAT,” the scientists stated.
The multi-approach shipping and delivery treatment (“ddpp.exe”), upon execution, unpacks shellcode to establish communication with an attacker-managed server and receive a next encrypted executable (“fplayer.exe”) that capabilities as the next stage downloader to fetch the Python RAT.
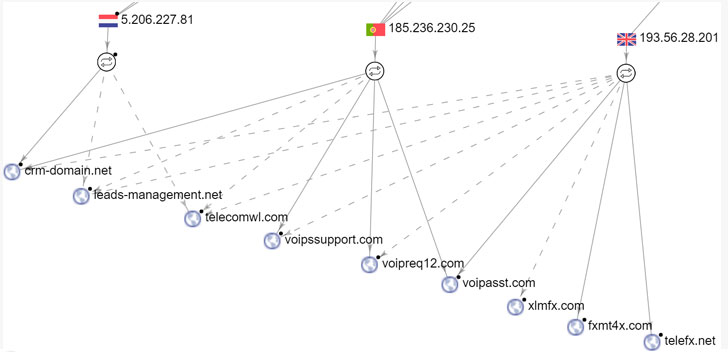
“In former campaigns of the group, Evilnum’s resources avoided working with domains in communications with the C2, only applying IP addresses,” the scientists mentioned. “Although the C2 IP tackle adjustments each individual handful of weeks, the listing of domains related with this IP tackle retains escalating.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Even though Evilnum’s precise origins still continue being unclear, it is apparent that their continuous improvisation of TTPs has aided them remain underneath the radar.
As the APT’s methods carry on to evolve, it is really crucial that organizations keep on being vigilant and workers keep an eye on their email messages for phishing makes an attempt and exercise warning when it comes to opening e-mails and attachments from unknown senders.
Found this short article interesting? Adhere to THN on Facebook, Twitter and LinkedIn to browse a lot more special content we submit.


 The cyber electronic divide: How to stage the playing industry
The cyber electronic divide: How to stage the playing industry