Emotet is one of the most perilous and widespread malware threats active nowadays.
At any time because its discovery in 2014—when Emotet was a conventional credential stealer and banking Trojan, the malware has developed into a modular, polymorphic system for distributing other types of pc viruses.
Becoming continually beneath growth, Emotet updates by itself consistently to make improvements to stealthiness, persistence, and insert new spying capabilities.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
This notorious Trojan is just one of the most usually malicious packages discovered in the wild. Typically, it is a part of a phishing attack, email spam that infects PCs with malware and spreads among the other pcs in the network.
If you’d like to locate out extra about the malware, gather IOCs, and get contemporary samples, test the following post in the Malware traits tracker, the provider with dynamic posts.
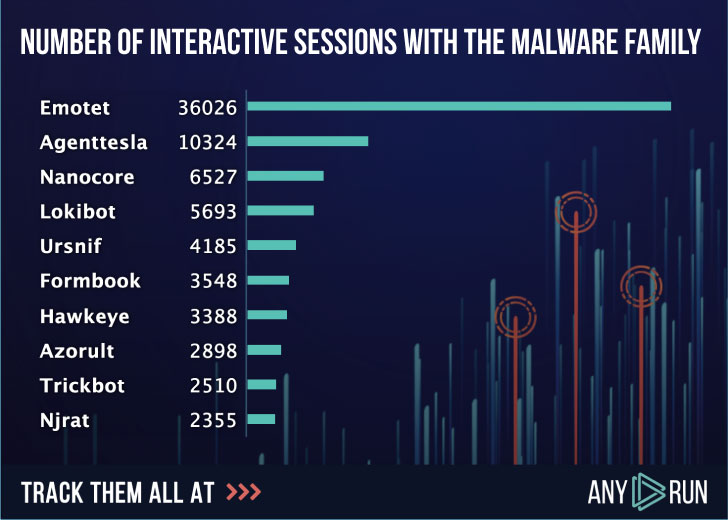
Emotet is the most uploaded malware during the earlier several years. Right here beneath is the score of uploads to ANY.Run services in 2019, where customers ran more than 36000 interactive classes of Emotet malware evaluation on the web.
The malware has transformed a whole lot over time, and with every single new edition, it receives additional and far more threatening for victims. Let’s have a closer look at how it developed.
When it was just like any other standard banking Trojan, the malware’s most important objective was to steal smaller companies’ qualifications, largely in Germany and Austria. By faking invoices or other monetary documents, it designed buyers click on the hyperlinks and enable the malware in.
Later on that calendar year, it acquired a assorted modular architecture, whose principal focuses had been downloading a malware payload, spreading onto as quite a few equipment as achievable, and sending malicious email messages to infect other companies.
In early 2015 soon after a small crack, Emotet confirmed up again. The general public RSA crucial, new deal with lists, RC4 encryption were being amongst the new capabilities of Trojan. From this point, the victims’ assortment commenced to enhance — Swiss financial institutions joined it. And all round, evasion techniques had been improved a lot.
In the latest variations, a substantial adjust in the system has took place. Emotet has turned into polymorphic malware, downloading other malicious packages to the infected computer system and the complete network as perfectly. It steals facts, adapts to various detection units, rents the contaminated hosts to other cybercriminals as a Malware-as-a-Services model.
Since Emotet utilizes stolen email messages to achieve victims’ rely on, spam has continuously remained the principal shipping approach for Emotet—making it convincing, extremely profitable, and harmful.
For case in point, in 2018, the federal government technique suffered an Emotet an infection in Allentown, a metropolis in eastern Pennsylvania, which value them $1 million for restoration.
The total city of Frankfurt experienced to shut down the network for the reason that of Emotet in 2019. Unique kinds of businesses, from the authorities to smaller companies, all public solutions ended up compelled to quit their get the job done by means of IT.
According to the latest exploration, Emotet is a globally danger that impacts all sorts of spheres. Just glance at the adhering to map, Italy, Spain, and the United Arab Emirates are the prime nations with the most attacked people.
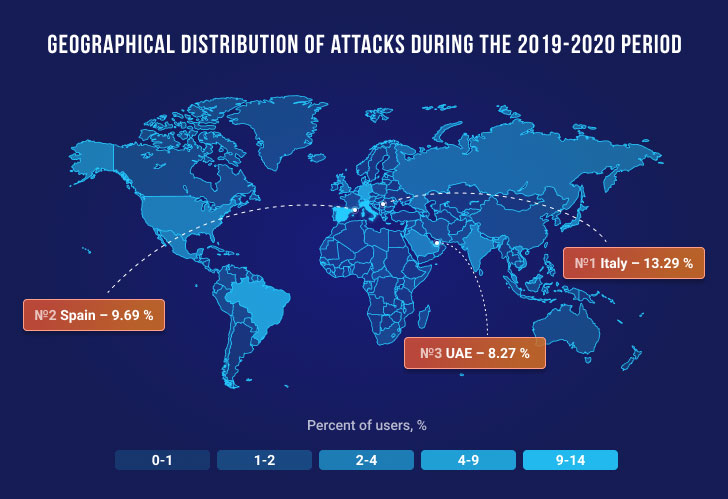
Recently France, Japan, and New Zealand’s cybersecurity corporations have introduced a increase in Emotet attacks concentrating on their nations around the world.
Emotet then and now
According to a graph of the Emotet samples uploaded to ANY.Run assistance, you can see the habits of the malware in 2019 and 2020.
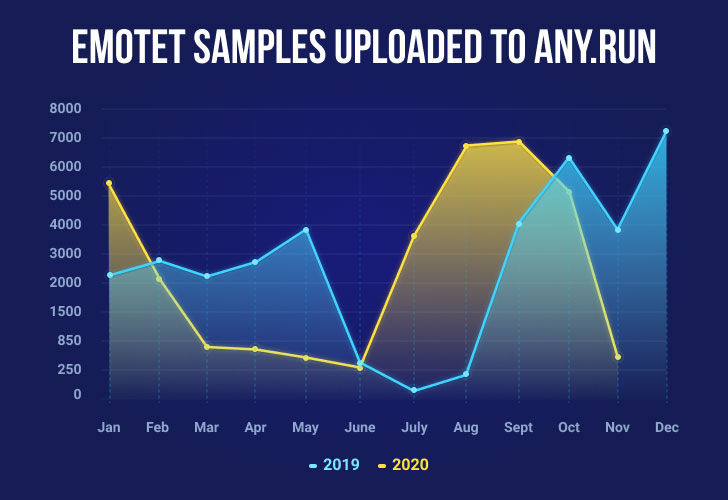
We can notice some similarities in its exercise. For instance, in June, Emotet tends to be on the decrease. On the other hand, it seems to present an raising pattern from August until Oct. In 2019 the stop of the calendar year was pretty lively for this type of attack, so we can hope it to be on the rise this yr as properly.
Emotet has remained a risk for yrs as it alterations forever. Early variations differ from the recent one particular, even by its intentions — Emotet has designed from the banking Trojan to the loader. When it arrives to execution evolution and doc templates, we will explain only variations that arrive soon after 2018. There had been variations even over these two decades, but the only issue that remains unchanged is supply.
For distribution and person execution, Emotet is using destructive spam and paperwork with VBA macros. Just after a target downloads the hooked up destructive paperwork from an email and opens it, the Business doc tricks the consumer into enabling the macro. After that, the embedded macro starts off its execution, and subsequent situations could range. The most popular variant in excess of the previous several years is that macros begin a Base64 encoded Powershell script that afterwards downloads an executable. But at this level, Emotet brings a great deal of various executions.
Numerous variants come to its existence when we converse about the initial measures following a maldoc was opened. VBA macro in Business office paperwork can begin cmd, Powershell, WScript, and, currently, for the very first time, Сertutil was utilised by the Emotet’s execution chain.
Other improvements in the execution process occurred in the chain amongst malicious documents and dropped/downloaded executable documents.
Not only has the execution chain reworked over time, but also the Emotet’s executable file itself — registry keys, information, and baby procedures in the file method. For illustration, in the 2018-2019 yrs, Emotet dropped its executable at the folder underneath a distinct route and produced a filename and the title of a folder working with a individual algorithm.
It improved the file identify era algorithm, procedure tree, and route technology algorithm for C2 interaction.
A further significant portion that characterizes this malware household is the maldocs’ templates it uses. They are continuously switching, and most of the time, Emotet utilizes its individual kinds. But in between them can also be discovered templates that beforehand had been used to distribute other malware family members these types of as Valak and Icedid.
Emotet from the ANY.RUN’s point of view
Of course, the principal obstacle with Emotet is to locate a way to discover it and fully grasp its behavior, so following that, you could strengthen the weak points in security.
There is a instrument that can give you a hand with that. ANY.Run is an interactive online sandbox that detects, analyzes, and screens cybersecurity threats, necessary if you offer with Emotet.
Furthermore, ANY.Operate has a exclusive resource — the investigation of general public submissions. It can be a vast database where by consumers share their investigations. And really usually, Emotet will become the “hero” of the working day: it has a leading posture of the most downloaded samples into ANY.Operate. That is why ANY.RUN’s encounter with the malware is interesting.
The initially stage of protecting your infrastructure from Emotet infection is — detecting the malware. ANY.Run sandbox has outstanding resources for Emotet detection and assessment.
The on line provider deals with Emotet frequently. So, let us attempt the interactive solution for Emotet detection and investigate just one of the samples jointly:
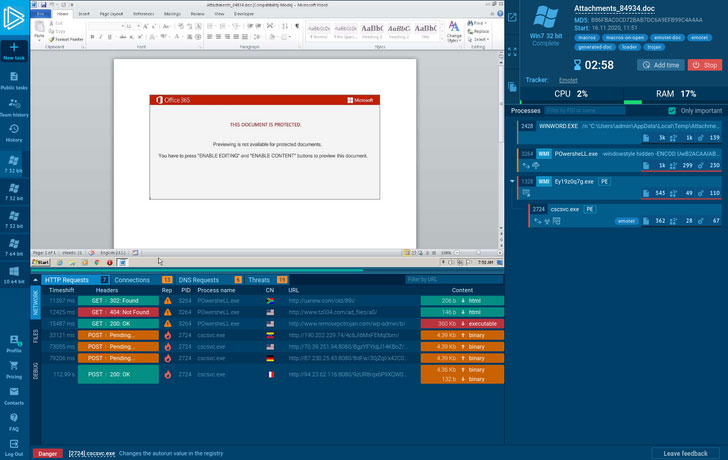
In this article is a destructive attachment from the phishing email that we uploaded to ANY.Operate and right away get the very first benefits. The procedure tree on the suitable demonstrates all operations that have been manufactured.
As shown, the first method commences to produce new data files in the user directory. Then POwersheLL.exe connects to the network and downloads executable files from the Internet. The past 1, winhttp.exe alterations the autorun worth in the registry and connects to the command-and-command server, both equally to retrieve instructions for subsequent malicious functions and exfiltrate stolen facts.
And ultimately, Emotet was detected by network activity. New Suricata rulesets from quality vendors these kinds of as Proofpoint (Rising Threats) and Positive Systems are a massive portion of the detection course of action.
In addition, ANY.Operate gives a handy Phony Net aspect. When turned on, it returns a 404 error that forces malware to reveal its C2 one-way links that assist accumulate Emotet’s IOCs a lot more effectively. That assists malware analysts improve their time as there is no want to deobfuscate it manually.
Interestingly, a established of destructive files with the similar template can have embedded VBA macro, main to creating different execution chains. All of them have the most important goal to trick a user who opened this maldoc to help VBA macro.
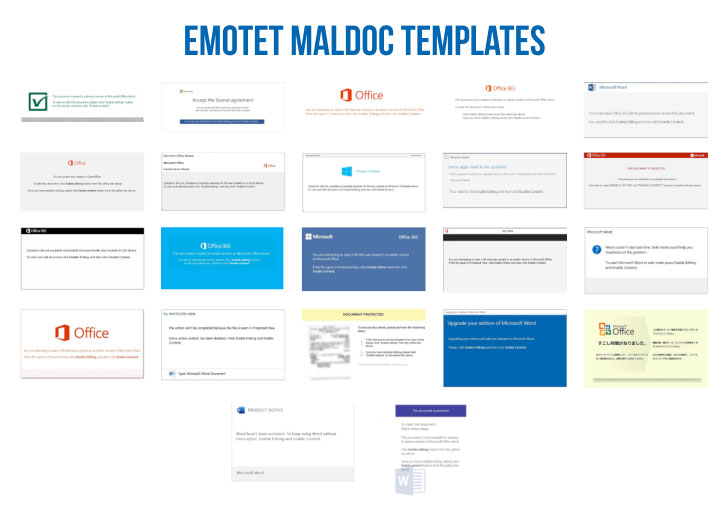
If you’d like to just take a appear at all of all those templates, just search by tag “emotet-doc” in ANY. RUN’s community submissions — these maldocs are clustered by material similarity.
Conclusion
This sort of tendency proves that Emotet is just not going to give up or shed the floor. Its evolution showed that the malware develops extremely promptly and adapts to almost everything.
If your company is linked to the Internet, the challenges may be broader and further than you know. Which is why it is accurate that combating complex threats like Emotet calls for a concerted effort and hard work from both people and organizations.
Also, the target of services like ANY.Run is to be mindful of this kind of potential threats and aid providers identify malware early and stay clear of bacterial infections at any price.
Investigation and detection with ANY.Operate is effortless, and any one can assess a bunch of clean samples every single day.
What is additional, the service is no cost to use and for downloading samples, and there is no doubt you can make use of ANY.Run — just give it a attempt!
Uncovered this article intriguing? Abide by THN on Facebook, Twitter and LinkedIn to study a lot more unique material we publish.
Some areas of this post are sourced from:
thehackernews.com

 Chinese Cloud Hopper Attackers Use Zerologon in New Campaign
Chinese Cloud Hopper Attackers Use Zerologon in New Campaign